Get the free SECURITY AND ACCESS
Show details
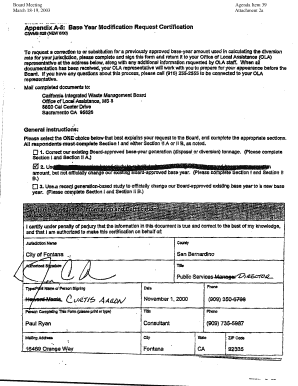
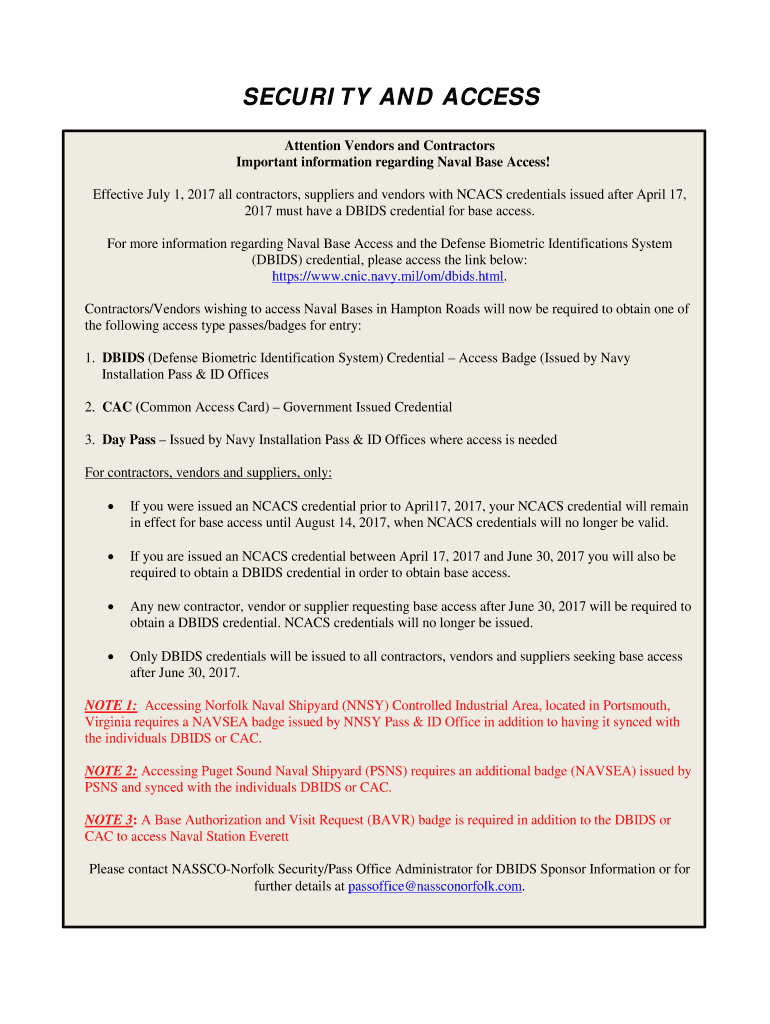
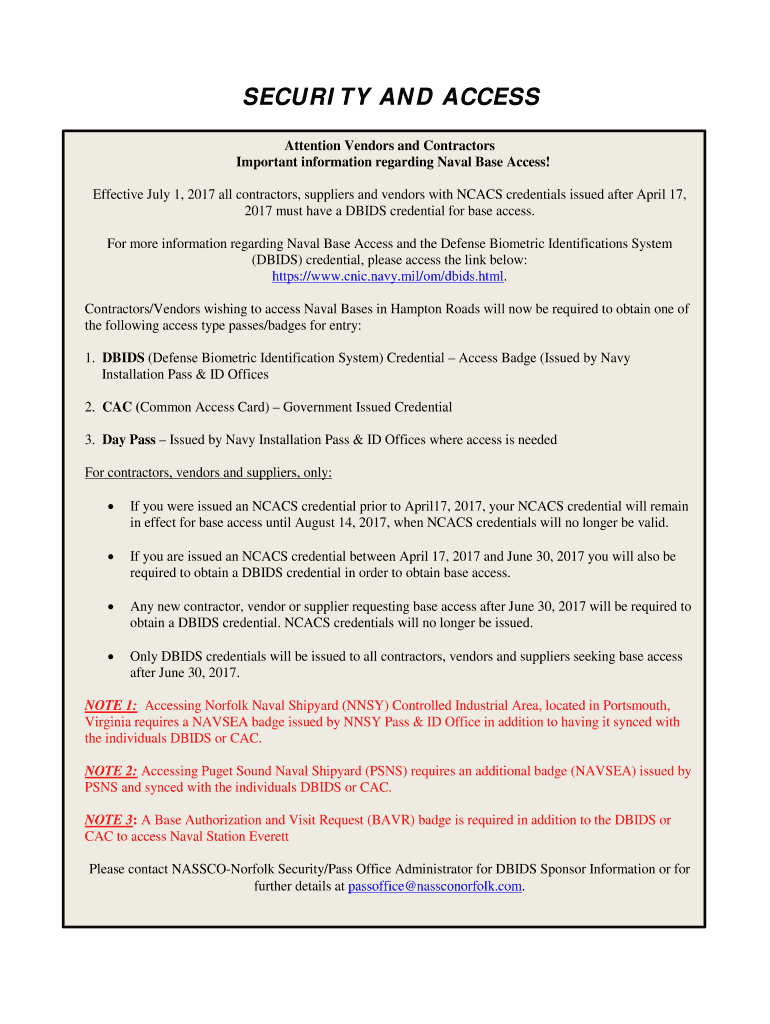
SECURITY AND ACCESS
Attention Vendors and Contractors
Important information regarding Naval Base Access!
Effective July 1, 2017, all contractors, suppliers and vendors with NC ACS credentials issued
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign security and access

Edit your security and access form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your security and access form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit security and access online
Follow the guidelines below to benefit from a competent PDF editor:
1
Sign into your account. It's time to start your free trial.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit security and access. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Save your file. Select it in the list of your records. Then, move the cursor to the right toolbar and choose one of the available exporting methods: save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud.
With pdfFiller, it's always easy to deal with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out security and access

How to fill out security and access:
01
Start by gathering all the necessary information and documentation required to establish security and access. This may include personal identification, background checks, and references.
02
Fill out the appropriate forms or applications provided by the organization or entity responsible for granting security and access. Make sure to provide accurate and up-to-date information.
03
Be prepared to answer any additional questions or provide further documentation as requested. This may include explaining the purpose or reason for requiring security and access.
04
Review and double-check all the provided information before submitting the forms. Make sure there are no errors or missing details that could delay or hinder the approval process.
05
Submit the filled-out forms along with any supporting documentation to the designated authority. Follow any specific instructions given regarding submission methods or deadlines.
06
Once the forms are submitted, patiently wait for a response from the authority. This may involve a review process, background checks, and verification of the information provided.
07
If approved, follow any further instructions or requirements regarding access and security protocols. This may include attending training sessions, obtaining security clearances or identification cards, and adhering to specific guidelines or procedures.
08
Regularly update and renew your security and access if required. Some forms of security and access may have expiration dates or need to be reviewed periodically to ensure continued eligibility.
Who needs security and access?
01
Organizations and institutions: Organizations of various types, such as government agencies, corporations, and educational institutions, require security and access for their premises or sensitive information.
02
Government employees: Government employees often need security and access to perform their duties effectively, especially if they handle classified or confidential information.
03
Contractors and vendors: Contractors, vendors, or third-party service providers who work closely with organizations may require security and access to complete their assigned tasks or access restricted areas.
04
Individuals in high-risk or sensitive roles: Individuals working in roles that entail high-risk environments, such as law enforcement officers, military personnel, or employees in critical infrastructure sectors, often need heightened security and access measures.
05
Researchers or professionals in specialized fields: Certain researchers, scientists, or professionals working in specialized fields may require security and access to protect their research, inventions, or intellectual property.
06
Visitors and guests: In some cases, visitors or guests may need temporary security and access to attend events, conferences, or meetings held in secure facilities.
07
Homeowners: Homeowners may need security and access measures for their residences, such as alarm systems, surveillance cameras, or access control systems, to protect their property and ensure personal safety.
08
Individuals with sensitive personal information: People with sensitive personal information, such as medical records or financial data, may need security and access to safeguard their privacy and prevent unauthorized access or fraud.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I modify security and access without leaving Google Drive?
Using pdfFiller with Google Docs allows you to create, amend, and sign documents straight from your Google Drive. The add-on turns your security and access into a dynamic fillable form that you can manage and eSign from anywhere.
How do I make changes in security and access?
pdfFiller not only lets you change the content of your files, but you can also change the number and order of pages. Upload your security and access to the editor and make any changes in a few clicks. The editor lets you black out, type, and erase text in PDFs. You can also add images, sticky notes, and text boxes, as well as many other things.
How do I edit security and access in Chrome?
Add pdfFiller Google Chrome Extension to your web browser to start editing security and access and other documents directly from a Google search page. The service allows you to make changes in your documents when viewing them in Chrome. Create fillable documents and edit existing PDFs from any internet-connected device with pdfFiller.
What is security and access?
Security and access refers to the measures put in place to protect sensitive information and control who has permission to access it.
Who is required to file security and access?
Security and access filings are typically required by organizations that handle sensitive data, such as government agencies, financial institutions, or healthcare providers.
How to fill out security and access?
Filling out security and access forms typically involves providing detailed information about the security measures in place and who has access to sensitive data.
What is the purpose of security and access?
The purpose of security and access is to ensure that sensitive information is protected from unauthorized access or disclosure.
What information must be reported on security and access?
Information that may need to be reported on security and access forms includes details about encryption methods used, access controls, and data breach response procedures.
Fill out your security and access online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Security And Access is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.