Get the free Guidelines for Assessing Threats and Managing Risks in the ...
Show details
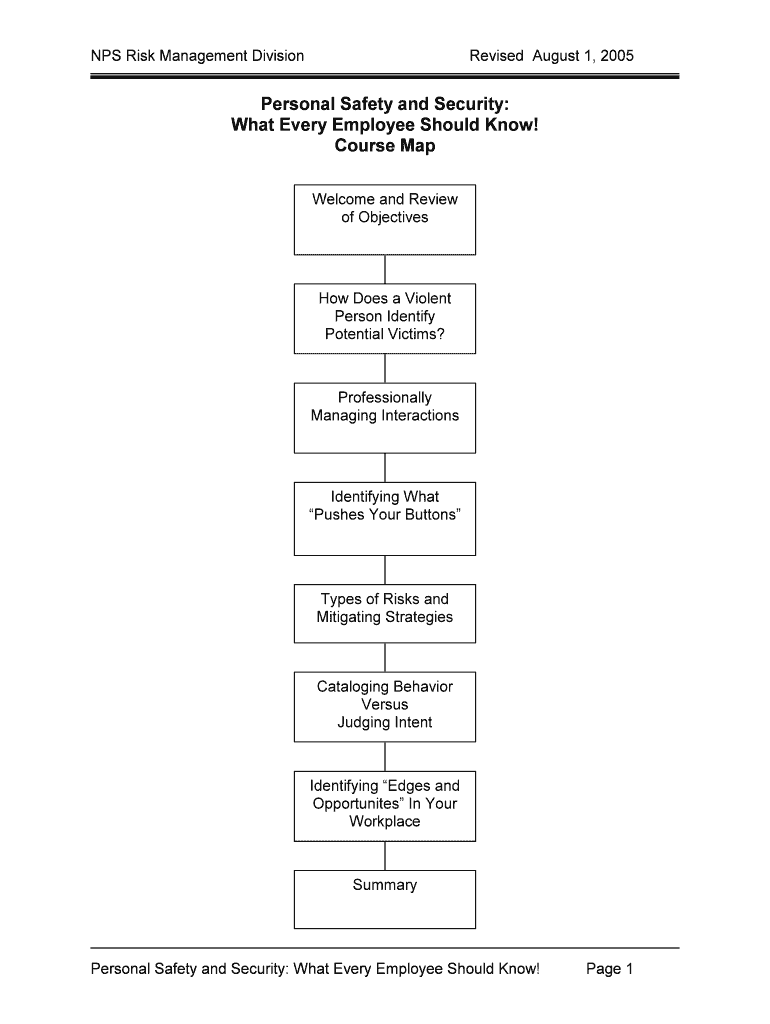
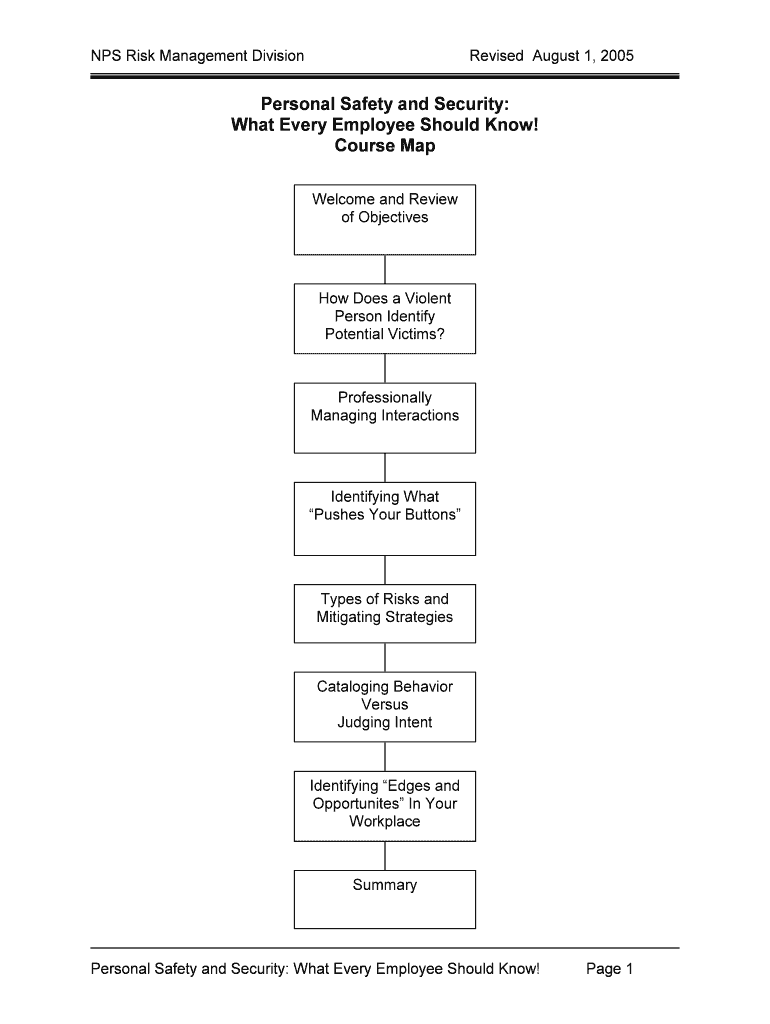
NPS Risk Management DivisionRevised August 1, 2005Personal Safety and Security:
What Every Employee Should Know!
Course Map
Welcome and Review
of Objectives Does a Violent
Person Identify
Potential
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign guidelines for assessing threats

Edit your guidelines for assessing threats form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your guidelines for assessing threats form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing guidelines for assessing threats online
To use our professional PDF editor, follow these steps:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit guidelines for assessing threats. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
It's easier to work with documents with pdfFiller than you can have ever thought. You may try it out for yourself by signing up for an account.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out guidelines for assessing threats

01
The first step in filling out guidelines for assessing threats is to gather relevant information. This includes identifying potential threats and their potential impact on the organization or individual. Research and gather data from reliable sources, such as previous security incidents or industry-specific threat assessments.
02
Next, carefully review and analyze the gathered information to identify patterns or common characteristics among threats. This can help in developing a comprehensive set of guidelines that cover a wide range of potential threats. Consider factors such as the likelihood of occurrence, potential severity, and impact on key assets or operations.
03
Once the information has been analyzed, it is time to outline the guidelines. Start by creating a clear and concise introduction that explains the purpose of the guidelines and who they are intended for. This sets the context for the rest of the document and ensures that readers understand the purpose and scope of the guidelines.
04
Divide the guidelines into specific sections or categories based on the types of threats being assessed. For example, you might have separate sections for physical security threats, cybersecurity threats, or natural disasters. Each section should include detailed instructions, criteria, or checklists for assessing and mitigating the specific threats covered.
05
It is important to involve relevant stakeholders in the development of the guidelines. Seek input and feedback from security experts, risk managers, and individuals responsible for the organization's overall security strategy. Their insights and expertise can help ensure that the guidelines are comprehensive and practical.
06
Review and revise the guidelines regularly to ensure they remain up-to-date and relevant. Threats evolve over time, so it is essential to stay current with emerging risks and vulnerabilities. Consider establishing a system for ongoing monitoring and updates to the guidelines to reflect changes in the threat landscape.
Who needs guidelines for assessing threats?
01
Organizations of all sizes and industries can benefit from having guidelines for assessing threats. This includes businesses, government agencies, educational institutions, healthcare facilities, and other entities that face security risks.
02
Individual professionals responsible for the security of their own assets, such as personal information or valuable possessions, can also benefit from having guidelines for assessing threats. This may include guidelines for assessing online security risks, home security risks, or travel-related threats.
03
Guidelines for assessing threats can be useful for decision-makers and security teams, helping them make informed decisions about resource allocation, risk mitigation strategies, and overall security planning. Additionally, these guidelines can provide a framework for training and educating employees or stakeholders about potential threats and appropriate responses.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I edit guidelines for assessing threats on a smartphone?
You can do so easily with pdfFiller’s applications for iOS and Android devices, which can be found at the Apple Store and Google Play Store, respectively. Alternatively, you can get the app on our web page: https://edit-pdf-ios-android.pdffiller.com/. Install the application, log in, and start editing guidelines for assessing threats right away.
How do I edit guidelines for assessing threats on an Android device?
With the pdfFiller Android app, you can edit, sign, and share guidelines for assessing threats on your mobile device from any place. All you need is an internet connection to do this. Keep your documents in order from anywhere with the help of the app!
How do I complete guidelines for assessing threats on an Android device?
On an Android device, use the pdfFiller mobile app to finish your guidelines for assessing threats. The program allows you to execute all necessary document management operations, such as adding, editing, and removing text, signing, annotating, and more. You only need a smartphone and an internet connection.
What is guidelines for assessing threats?
The guidelines for assessing threats provide a framework for evaluating potential risks and dangers.
Who is required to file guidelines for assessing threats?
Individuals or organizations that may be at risk of facing threats are required to file the guidelines for assessing threats.
How to fill out guidelines for assessing threats?
Guidelines for assessing threats can be filled out by providing detailed information about potential risks, mitigation strategies, and contact information for relevant parties.
What is the purpose of guidelines for assessing threats?
The purpose of guidelines for assessing threats is to proactively identify and address potential risks to ensure the safety and security of individuals or organizations.
What information must be reported on guidelines for assessing threats?
Information such as identified threats, risk assessments, mitigation strategies, and contact information must be reported on guidelines for assessing threats.
Fill out your guidelines for assessing threats online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Guidelines For Assessing Threats is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.