
Get the free Use Cases for Securing Web Services Using Oracle Web Services
Show details
Oracle Fusion Middleware Use Cases for Securing Web Services Using Oracle Web Services Manager 12c (12.2.1.1) E71258 01June 2016 Documentation for developers and administrators that provides use cases
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign use cases for securing
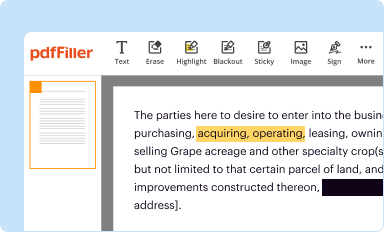
Edit your use cases for securing form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
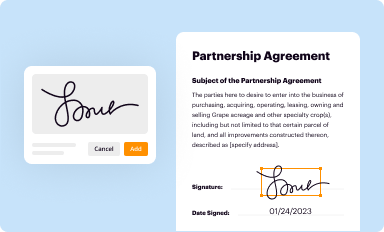
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
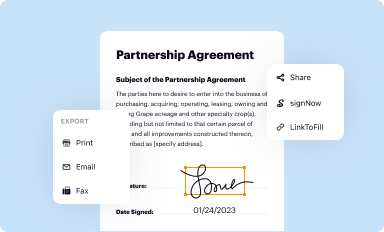
Share your form instantly
Email, fax, or share your use cases for securing form via URL. You can also download, print, or export forms to your preferred cloud storage service.
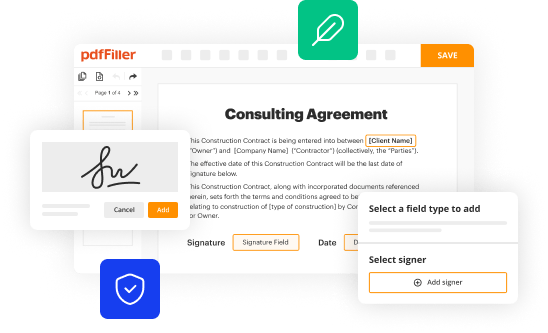
How to edit use cases for securing online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit use cases for securing. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out use cases for securing
How to fill out use cases for securing?
01
Identify the purpose: Start by clearly defining the objective of the use case for securing. Determine what specific aspect or area you want to secure and why it needs to be secured.
02
Identify the actors: Identify the different individuals or entities involved in the process of securing. This can include users, administrators, third-party services, or any other stakeholders.
03
Define the actions: Outline the specific actions or steps that need to be taken to ensure the security of the identified aspect. This can include implementing security measures, establishing access controls, conducting regular assessments, or any other relevant actions.
04
Determine the potential threats: Identify potential threats or vulnerabilities that could compromise the security. Consider both internal and external threats, such as unauthorized access, data breaches, or physical breaches.
05
Define the security measures: Determine the specific security measures that will be implemented to mitigate the identified threats. This can include firewalls, encryption, authentication methods, training programs, or any other relevant measures.
06
Establish the desired outcomes: Define the desired outcomes or objectives that you want to achieve by implementing the use case for securing. This could be ensuring data confidentiality, preventing unauthorized access, minimizing risks, or any other specific outcomes.
07
Testing and validation: Conduct testing and validation processes to ensure the effectiveness of the use case for securing. This can involve penetration testing, vulnerability scanning, or any other methods to assess the security measures.
Who needs use cases for securing?
01
Organizations: Businesses and organizations of all sizes need use cases for securing to protect their sensitive data, intellectual property, and infrastructure from potential threats.
02
IT Professionals: IT professionals, including system administrators, network engineers, and cybersecurity specialists, need use cases to design and implement robust security measures.
03
Developers: Developers need use cases for securing to understand the security requirements of their applications or software and incorporate necessary safeguards.
04
Compliance and regulatory bodies: Use cases for securing are essential for compliance and regulatory bodies to evaluate and ensure adherence to security standards and guidelines.
05
End Users: End users, such as employees, customers, or individuals utilizing online services, benefit from use cases for securing as they ensure the protection of their personal information and privacy.
Overall, use cases for securing serve as a crucial tool for various stakeholders involved in protecting sensitive data, infrastructure, and ensuring overall security.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I get use cases for securing?
With pdfFiller, an all-in-one online tool for professional document management, it's easy to fill out documents. Over 25 million fillable forms are available on our website, and you can find the use cases for securing in a matter of seconds. Open it right away and start making it your own with help from advanced editing tools.
Can I sign the use cases for securing electronically in Chrome?
You certainly can. You get not just a feature-rich PDF editor and fillable form builder with pdfFiller, but also a robust e-signature solution that you can add right to your Chrome browser. You may use our addon to produce a legally enforceable eSignature by typing, sketching, or photographing your signature with your webcam. Choose your preferred method and eSign your use cases for securing in minutes.
Can I create an electronic signature for signing my use cases for securing in Gmail?
Use pdfFiller's Gmail add-on to upload, type, or draw a signature. Your use cases for securing and other papers may be signed using pdfFiller. Register for a free account to preserve signed papers and signatures.
What is use cases for securing?
Use cases for securing are scenarios or examples that outline how a system or application should behave under certain conditions to ensure the security of data and information.
Who is required to file use cases for securing?
Developers, system architects, and security analysts are typically responsible for creating and filing use cases for securing.
How to fill out use cases for securing?
Use cases for securing can be filled out by documenting various scenarios, outlining potential threats, identifying security measures, and detailing how the system should respond to security incidents.
What is the purpose of use cases for securing?
The purpose of use cases for securing is to help design and implement security measures that protect against potential threats and vulnerabilities.
What information must be reported on use cases for securing?
Information such as system behavior, security requirements, threat assessments, risk mitigation strategies, and incident response plans should be reported on use cases for securing.
Fill out your use cases for securing online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Use Cases For Securing is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.




















