Get the free Cyberoam Internet Threats Trend Report April 2011
Show details
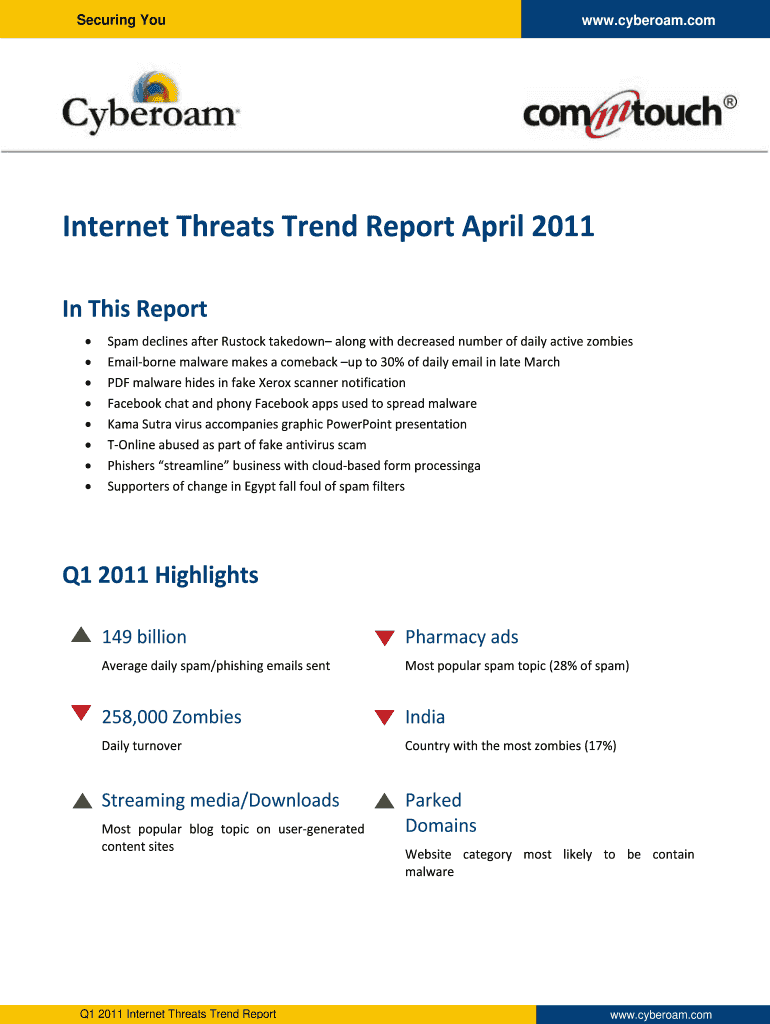
Securing You www.cyberoam.com Internet Threats Trend Report April 2011 In This Report Spam declines after Restock takedown along with decreased number of daily active zombies Email?borne malware makes
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign cyberoam internet threats trend

Edit your cyberoam internet threats trend form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your cyberoam internet threats trend form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit cyberoam internet threats trend online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit cyberoam internet threats trend. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out cyberoam internet threats trend

How to Fill Out Cyberoam Internet Threats Trend:
01
Start by identifying the purpose of filling out the Cyberoam Internet Threats Trend. Understand why you need to monitor and analyze internet threats to ensure the security of your network.
02
Familiarize yourself with the Cyberoam Internet Threats Trend form or platform. Understand the different sections or fields that need to be filled out and what information they require.
03
Gather the necessary data or information to accurately complete the Cyberoam Internet Threats Trend. This may include network logs, incident reports, and any other relevant documentation.
04
Analyze the gathered information to identify the different types of internet threats that your network is facing. This can include malware, phishing attacks, DDoS attacks, and more.
05
Assess the severity and impact of each identified threat. Categorize them based on their potential harm to your network, sensitive data, or users.
06
Prioritize the threats based on their severity and impact. This will help you determine which threats require immediate attention and which can be addressed later.
07
Fill out the Cyberoam Internet Threats Trend form or platform by entering the details of each identified threat. Include relevant information such as the type of threat, date and time of occurrence, and any additional details that may be required.
08
Submit the completed form or save the information in the Cyberoam Internet Threats Trend platform. Ensure that the data is safely stored and easily accessible for future reference or analysis.
09
Regularly review and update the Cyberoam Internet Threats Trend to stay updated with the evolving threat landscape. This will help you proactively address emerging threats and strengthen your network security.
Who Needs Cyberoam Internet Threats Trend:
01
Organizations and businesses with an online presence and network infrastructure.
02
IT administrators, network security professionals, and cybersecurity teams responsible for safeguarding the network against internet threats.
03
Any entity that values the security and integrity of their data, systems, and online operations.
04
Industries or sectors that are particularly vulnerable to cyber threats, such as finance, healthcare, and government agencies.
05
Organizations that have experienced previous internet threats and want to enhance their monitoring and response capabilities.
06
Any individual or entity that wants to stay informed about the latest internet threats and trends to ensure their network's security.
07
Companies that rely heavily on the internet for their daily operations and want to proactively mitigate any potential risks or vulnerabilities.
Note: Remember to consult the specific guidelines provided by Cyberoam or your organization when filling out the Cyberoam Internet Threats Trend form or platform.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I execute cyberoam internet threats trend online?
pdfFiller makes it easy to finish and sign cyberoam internet threats trend online. It lets you make changes to original PDF content, highlight, black out, erase, and write text anywhere on a page, legally eSign your form, and more, all from one place. Create a free account and use the web to keep track of professional documents.
How do I make changes in cyberoam internet threats trend?
The editing procedure is simple with pdfFiller. Open your cyberoam internet threats trend in the editor. You may also add photos, draw arrows and lines, insert sticky notes and text boxes, and more.
Can I sign the cyberoam internet threats trend electronically in Chrome?
Yes. You can use pdfFiller to sign documents and use all of the features of the PDF editor in one place if you add this solution to Chrome. In order to use the extension, you can draw or write an electronic signature. You can also upload a picture of your handwritten signature. There is no need to worry about how long it takes to sign your cyberoam internet threats trend.
What is cyberoam internet threats trend?
Cyberoam internet threats trend refers to the changing patterns of internet threats identified by Cyberoam to better protect users from cyber attacks.
Who is required to file cyberoam internet threats trend?
Network administrators and cybersecurity professionals are required to file cyberoam internet threats trend.
How to fill out cyberoam internet threats trend?
To fill out cyberoam internet threats trend, one must collect and analyze data on the latest internet threats, and then report findings using the specified format.
What is the purpose of cyberoam internet threats trend?
The purpose of cyberoam internet threats trend is to raise awareness about the evolving landscape of cyber threats and provide recommendations for proactive security measures.
What information must be reported on cyberoam internet threats trend?
Information such as types of threats, frequency of attacks, affected systems, and mitigation strategies must be reported on cyberoam internet threats trend.
Fill out your cyberoam internet threats trend online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Cyberoam Internet Threats Trend is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.


















