
Get the free Applied Cryptography
Show details
Applied Cryptography 2001 Otis Fotopoulos Boston 1 Contents Table Of Contents Introduction To Applied Cryptography ................................................. 3 1. 2. Lossless compression ..........................................................................
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign applied cryptography
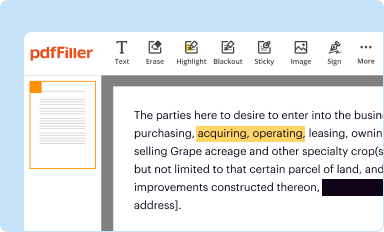
Edit your applied cryptography form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
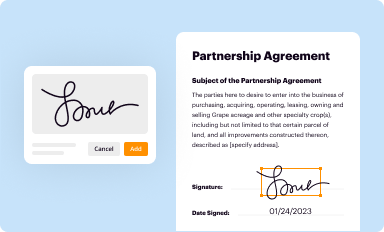
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
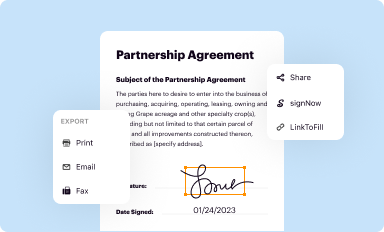
Share your form instantly
Email, fax, or share your applied cryptography form via URL. You can also download, print, or export forms to your preferred cloud storage service.
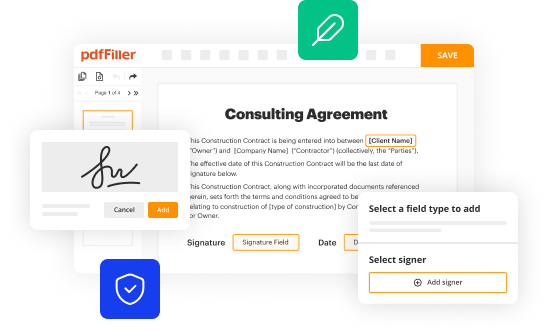
Editing applied cryptography online
To use our professional PDF editor, follow these steps:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit applied cryptography. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
With pdfFiller, it's always easy to deal with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out applied cryptography
How to fill out applied cryptography:
01
Familiarize yourself with the basics: Start by understanding the fundamentals of cryptography, including encryption algorithms, key management, and secure protocols. This will provide a solid foundation for exploring applied cryptography.
02
Identify your use case: Determine why you need applied cryptography. Are you looking to secure communication channels, protect sensitive data, or authenticate users? Knowing your specific requirements will guide your approach to filling out applied cryptography.
03
Choose appropriate cryptographic algorithms: Based on your use case, select the appropriate cryptographic algorithms. For example, if data confidentiality is a priority, symmetric encryption like AES may be suitable. If you need secure digital signatures, consider asymmetric algorithms like RSA or Elliptic Curve Cryptography.
04
Implement proper key management: Plan and implement a robust key management system. Keys play a crucial role in cryptography, so ensure they are properly generated, securely stored, rotated periodically, and revoked when necessary. This step is crucial to maintaining the overall security of your applied cryptography implementation.
05
Test for vulnerabilities: Conduct thorough testing to identify potential vulnerabilities in your applied cryptography setup. Use penetration testing, code reviews, and cryptographic analysis tools to assess the strength of your implementation. Identify and address any weaknesses to ensure the security of your system.
06
Keep up with advancements and best practices: Stay informed about the latest advancements, standards, and best practices in applied cryptography. Attend conferences, read research papers, and engage with the cryptography community to continuously enhance your knowledge and skills in this field.
Who needs applied cryptography:
01
Individuals and organizations handling sensitive data: Any individual or organization dealing with sensitive information needs applied cryptography to protect the confidentiality, integrity, and authenticity of their data. This includes government agencies, financial institutions, healthcare providers, and e-commerce platforms, among others.
02
Communication and network security professionals: Professionals working in the field of communication and network security require applied cryptography knowledge to ensure the secure transfer of data across networks and protect against unauthorized access, eavesdropping, and tampering.
03
Cybersecurity specialists and researchers: Applied cryptography is a crucial area of study and research for cybersecurity professionals. These specialists develop and analyze cryptographic algorithms, protocols, and systems to strengthen security measures and protect against emerging threats.
04
Software developers and engineers: Building secure software applications often involves implementing applied cryptography. Software developers and engineers need to understand cryptographic principles to design and incorporate encryption, digital signatures, and secure communication protocols into their applications.
In conclusion, filling out applied cryptography requires understanding its basics, identifying specific use cases, choosing appropriate algorithms, implementing proper key management, conducting vulnerability testing, and staying up to date with advancements. Individuals and organizations handling sensitive data, communication and network security professionals, cybersecurity specialists, and software developers are among those who need applied cryptography expertise.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I edit applied cryptography from Google Drive?
You can quickly improve your document management and form preparation by integrating pdfFiller with Google Docs so that you can create, edit and sign documents directly from your Google Drive. The add-on enables you to transform your applied cryptography into a dynamic fillable form that you can manage and eSign from any internet-connected device.
How do I make changes in applied cryptography?
The editing procedure is simple with pdfFiller. Open your applied cryptography in the editor. You may also add photos, draw arrows and lines, insert sticky notes and text boxes, and more.
Can I sign the applied cryptography electronically in Chrome?
Yes. You can use pdfFiller to sign documents and use all of the features of the PDF editor in one place if you add this solution to Chrome. In order to use the extension, you can draw or write an electronic signature. You can also upload a picture of your handwritten signature. There is no need to worry about how long it takes to sign your applied cryptography.
What is applied cryptography?
Applied cryptography is the practice of using cryptographic algorithms to secure data and communications.
Who is required to file applied cryptography?
Companies and organizations that handle sensitive information and want to protect it from unauthorized access are required to file applied cryptography.
How to fill out applied cryptography?
Applied cryptography can be filled out by using encryption techniques and secure communication protocols to safeguard data.
What is the purpose of applied cryptography?
The purpose of applied cryptography is to ensure confidentiality, integrity, and authenticity of data and communications.
What information must be reported on applied cryptography?
Information such as encryption keys, algorithms used, and security protocols implemented must be reported on applied cryptography.
Fill out your applied cryptography online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Applied Cryptography is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.




















