Last updated on Apr 10, 2026

Get the free Hackers
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is hackers
The hackers form is a registration document used by individuals interested in cybersecurity and ethical hacking to join related communities and initiatives.
pdfFiller scores top ratings on review platforms




Who needs hackers?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to hackers
Understanding the Hackers Form
The hackers form is a crucial document designed to facilitate essential processes within various sectors. Its primary purpose is to gather specific information that streamlines compliance and ensures that all parties are held accountable. Accurately completing this form is vital, as any discrepancies can substantially impact users' responsibilities and the outcomes of their applications.
-
Defines the hackers form and its core function.
-
Stresses the significance of precise data entry.
-
Explains the ramifications on users' duties and results.
Benefits of Using the Hackers Form
Utilizing the hackers form offers numerous advantages that significantly enhance user experience and operational efficiency. By adopting this form, users can enjoy a more streamlined process that minimizes compliance issues and reduces chances of errors. Submitting through a trusted platform like pdfFiller adds another layer of reliability, ensuring that submissions are handled with care.
-
Streamlines processes effectively for users.
-
Improves compliance while minimizing errors.
-
Offers the security of a trusted platform for form submissions.
Key Features of the Hackers Form
The hackers form boasts several essential features designed to simplify the completion process for users. Among these functionalities are fillable fields equipped with automated error checks that guide users in filling out the required information accurately. Additionally, digital signatures and eSigning options enhance the security and efficiency of the submission process, while compatibility with various document formats facilitated through pdfFiller ensures versatility.
-
Includes fillable fields that facilitate easy data entry.
-
Automated error checks to ensure accuracy.
-
Enables digital signatures for added security.
-
Offers compatibility with multiple document formats.
Who Needs to Complete the Hackers Form?
The hackers form is required by various individuals across different professions, particularly those engaged in compliance-sensitive industries. Scenarios where the form is critical include regulatory requirements where accurate documentation is essential. Specific sectors, such as technology, cybersecurity, and any business handling sensitive information, often rely on this form to ensure compliance.
-
Individuals in compliance-heavy professions.
-
Scenarios requiring documented compliance.
-
Industries such as technology and cybersecurity.
How to Fill Out the Hackers Form Online (Step-by-Step)
Completing the hackers form online through pdfFiller can be achieved through a straightforward process. Follow these clear steps for efficient form completion:
-
Access the hackers form via pdfFiller.
-
Fill out required fields while ensuring accurate information.
-
Utilize available tools to assist with complex sections.
-
Review entries to verify that all information is correct.
-
Submit the completed form securely online.
Common Errors and How to Avoid Them
Understanding common mistakes users often make while completing the hackers form can substantially improve submission outcomes. Frequent errors include incomplete fields and incorrect data entries. To mitigate such mistakes, double-checking information before submission is key, along with utilizing pdfFiller’s tools designed to minimize errors throughout the process.
-
Incomplete sections leading to submission issues.
-
Incorrectly entered data that can cause delays.
-
Double-checking information before final submission.
Submission Methods for the Hackers Form
There are several methods available for submitting the completed hackers form, catering to different preferences and requirements. Users can opt to submit the form online via pdfFiller, or choose traditional methods such as mailing the document. Each method has its specific requirements, and submitting digitally offers notable benefits such as faster processing and immediate confirmation.
-
Online submission through the pdfFiller platform.
-
Mail options for those preferring paper submissions.
-
Immediate confirmation when submitted digitally.
What Happens After Submission of the Hackers Form?
After users submit the hackers form, they can expect a systematic post-submission process. Confirmation methods, such as emails or notifications within pdfFiller, ensure users are aware of their submission status. Additionally, users may also have access to tracking options that allow them to monitor the progress and outcomes of their submissions, providing peace of mind.
-
Email or notification confirmations regarding submission.
-
Tracking options for monitoring submission status.
-
Potential timelines for results following submission.
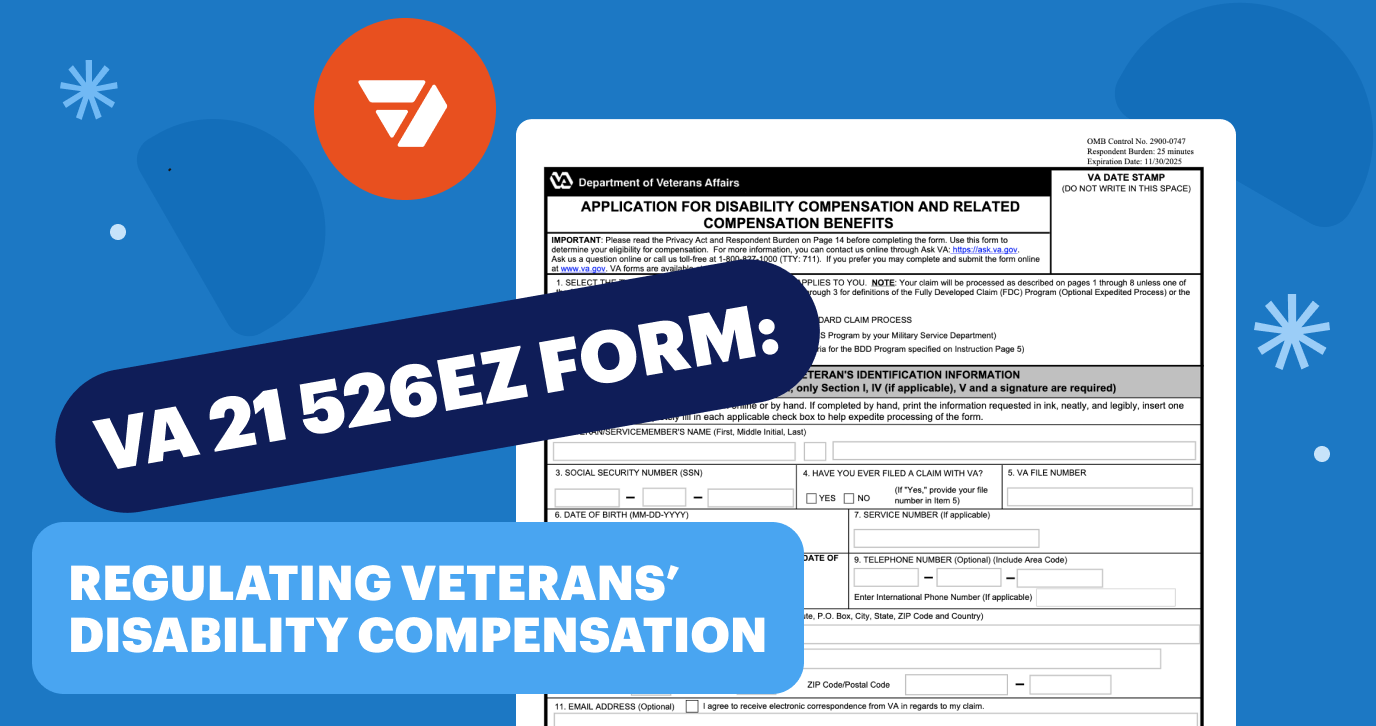
Security and Compliance When Using the Hackers Form
When utilizing pdfFiller to complete the hackers form, users can rest assured that their information is protected. pdfFiller employs advanced security measures such as 256-bit encryption and complies with regulations like HIPAA and GDPR, ensuring that sensitive data remains secure during transmission and storage. Users can trust pdfFiller's reputation, bolstered by compliance certifications, to handle their information responsibly.
-
Employs 256-bit encryption for data security.
-
Complies with HIPAA and GDPR regulations.
-
Offers user confidence in handling sensitive documents.
Experience Streamlined Form Completion with pdfFiller
Utilizing pdfFiller for completing the hackers form not only simplifies the process but also enhances usability. With intuitive features designed to aid users, pdfFiller makes form filling a less cumbersome task. Experience the numerous advantages of using pdfFiller and transform your document management tasks effectively.
-
Recaps benefits of utilizing pdfFiller for forms.
-
Highlights user-friendly features to ease the process.
-
Encourages beginning document management with pdfFiller.
How to fill out the hackers
-
1.To begin, visit pdfFiller and log into your account or create a new one if necessary. Search for the 'hackers' form in the template library.
-
2.Once you find the form, click to open it in the pdfFiller interface where you can start editing.
-
3.Before filling out the form, gather necessary information such as your personal details, contact information, and any experiences relevant to cybersecurity.
-
4.Proceed to fill in the required fields, which will typically include your name, email address, and any relevant skills or experiences in cybersecurity.
-
5.Use the navigation tools on pdfFiller to move smoothly between sections of the form. Don't forget to double-check any fields marked as mandatory.
-
6.After filling in all information, review the completed form to ensure accuracy and completeness. Look for any errors or incomplete sections.
-
7.Finally, save your filled form by clicking the 'Save' option. You can also download it in various formats or submit it directly through pdfFiller.

Who is eligible to fill out the hackers form?
Anyone interested in cybersecurity and ethical hacking can fill out the hackers form, including students, professionals, and enthusiasts.
Is there a deadline for submitting the hackers form?
Typically, deadlines depend on the specific event or organization associated with the form. Check the form's instructions for relevant dates.
How do I submit the completed hackers form?
Completed forms can be submitted directly through pdfFiller by emailing it to the designated contact address mentioned in your form or using the provided submission link.
What supporting documents do I need for the hackers form?
Generally, no supporting documents are needed to fill out the hackers form. However, having a résumé or portfolio may help if required.
What common mistakes should I avoid when filling out the hackers form?
Ensure that all required fields are completed. A common mistake is submitting without checking for accuracy or missing information.
What is the typical processing time after submitting the hackers form?
Processing times may vary, but you can generally expect a response within a few days to a week, especially during busy periods.
What if I encounter technical issues while using pdfFiller?
If you face technical issues, consult pdfFiller's support resources or contact their customer service for assistance.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.