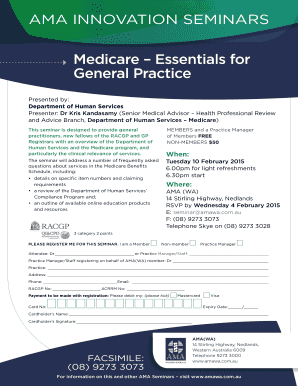
Get the free Physical Access Checklist. Cybersecurity Physical Access Checklist
Show details
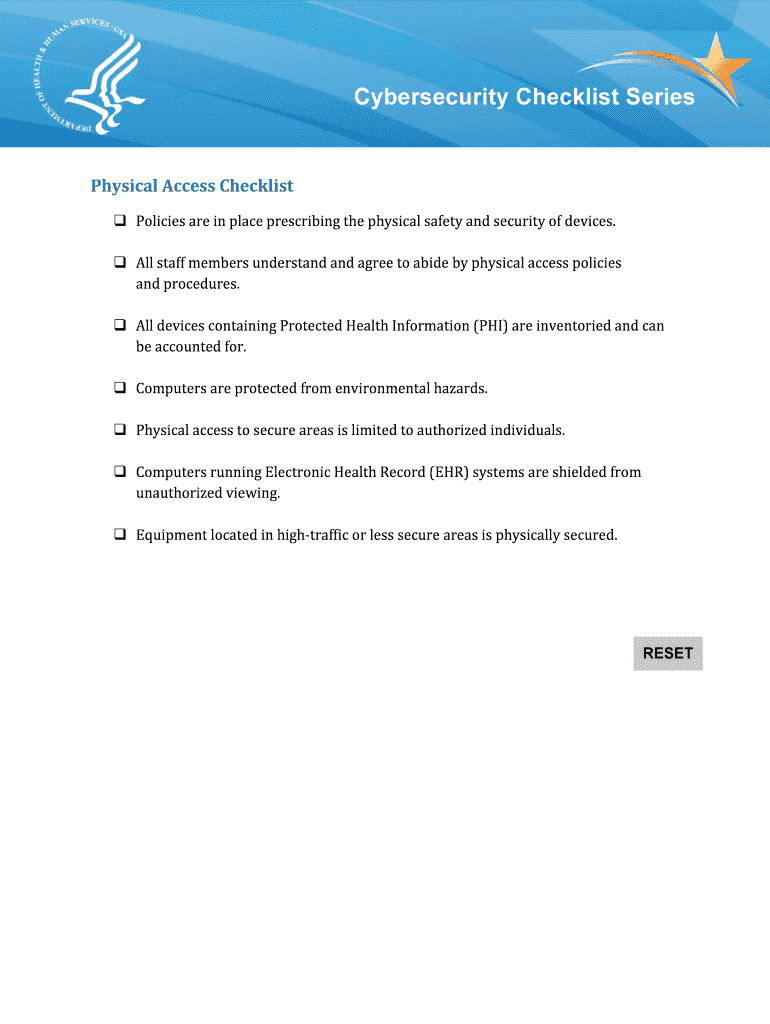
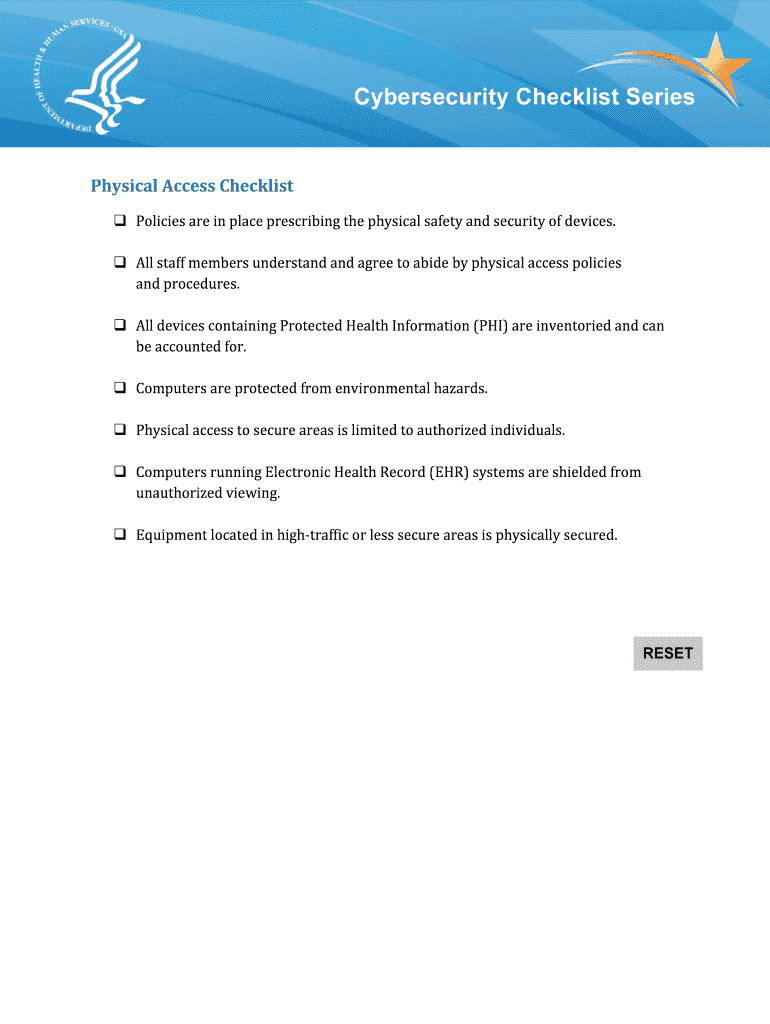
Cybersecurity Checklist Series Physical Access Checklist Policies are in place prescribing the physical safety and security of devices. All staff members understand and agree to abide by physical
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign physical access checklist cybersecurity
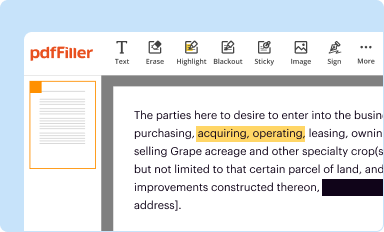
Edit your physical access checklist cybersecurity form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
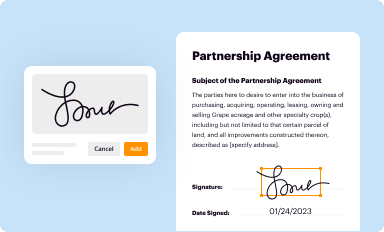
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
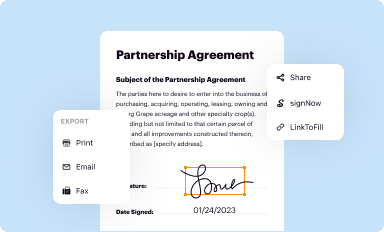
Share your form instantly
Email, fax, or share your physical access checklist cybersecurity form via URL. You can also download, print, or export forms to your preferred cloud storage service.
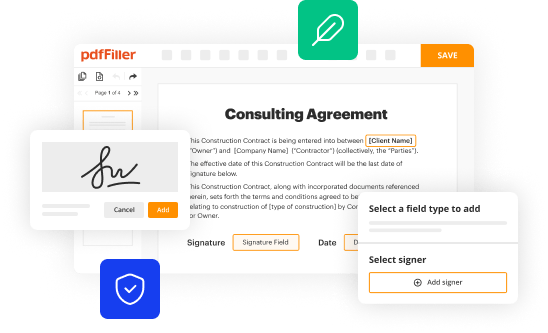
Editing physical access checklist cybersecurity online
Follow the steps below to use a professional PDF editor:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit physical access checklist cybersecurity. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
It's easier to work with documents with pdfFiller than you can have believed. You may try it out for yourself by signing up for an account.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out physical access checklist cybersecurity
How to fill out physical access checklist cybersecurity
01
Start by gathering all the necessary information and documents required for the physical access checklist.
02
Review the checklist and ensure you understand each point and requirement.
03
Begin with documenting the physical security policies and procedures in place.
04
Assess the physical access controls including doors, locks, card readers, biometric systems, and CCTV cameras.
05
Validate the existence and functionality of access control logs and monitoring systems.
06
Evaluate the physical security measures for server rooms, data centers, and other critical areas.
07
Check for the proper installation and functionality of surveillance systems.
08
Inspect the physical protection of network equipment, servers, and storage devices.
09
Conduct a thorough inspection of visitor management systems and processes.
10
Review the handling and disposal procedures for sensitive or classified materials.
11
Conduct an assessment of the signage, labeling, and access restriction notices.
12
Ensure all physical access points are properly secured and monitored.
13
Document all findings, observations, and recommendations in the checklist report.
14
Review and verify that all identified issues and recommendations have been addressed.
15
Repeat the physical access checklist periodically to ensure continuous compliance.
Who needs physical access checklist cybersecurity?
01
Organizations that handle sensitive data or confidential information.
02
Companies with physical infrastructure and equipment that require protection.
03
Government agencies and institutions dealing with classified or restricted materials.
04
Financial institutions and banks that need to comply with regulatory requirements.
05
Data centers and hosting providers with physical server infrastructure.
06
Healthcare facilities that store sensitive patient information.
07
Any entity concerned about physical security and preventing unauthorized access.
08
Businesses that value the integrity and protection of their assets and resources.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I execute physical access checklist cybersecurity online?
Filling out and eSigning physical access checklist cybersecurity is now simple. The solution allows you to change and reorganize PDF text, add fillable fields, and eSign the document. Start a free trial of pdfFiller, the best document editing solution.
How do I make edits in physical access checklist cybersecurity without leaving Chrome?
Download and install the pdfFiller Google Chrome Extension to your browser to edit, fill out, and eSign your physical access checklist cybersecurity, which you can open in the editor with a single click from a Google search page. Fillable documents may be executed from any internet-connected device without leaving Chrome.
How do I fill out physical access checklist cybersecurity using my mobile device?
Use the pdfFiller mobile app to fill out and sign physical access checklist cybersecurity. Visit our website (https://edit-pdf-ios-android.pdffiller.com/) to learn more about our mobile applications, their features, and how to get started.
What is physical access checklist cybersecurity?
Physical access checklist cybersecurity is a list of procedures and protocols to ensure that only authorized individuals have access to physical assets, such as server rooms and data centers, in order to prevent unauthorized access and protect sensitive information.
Who is required to file physical access checklist cybersecurity?
Businesses and organizations that handle sensitive information and have physical assets that need to be protected from unauthorized access are required to file physical access checklist cybersecurity.
How to fill out physical access checklist cybersecurity?
Physical access checklist cybersecurity can be filled out by reviewing and documenting all physical access control procedures and protocols in place, identifying any gaps or weaknesses, and implementing necessary changes to enhance security measures.
What is the purpose of physical access checklist cybersecurity?
The purpose of physical access checklist cybersecurity is to ensure that adequate measures are in place to protect physical assets from unauthorized access, reduce the risk of breaches and data theft, and comply with cybersecurity regulations and standards.
What information must be reported on physical access checklist cybersecurity?
Physical access checklist cybersecurity must include details of physical access control measures, such as access control policies, procedures, monitoring systems, and any incidents or breaches that have occurred.
Fill out your physical access checklist cybersecurity online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Physical Access Checklist Cybersecurity is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.