UNM HSC IT Security Review Cover free printable template
Show details
Section 1: IT Security Checklist. Begin addressing listed items at the outset of IT projects involving Vendor access, processing, or storage of patient, student,
pdfFiller is not affiliated with any government organization
Get, Create, Make and Sign UNM HSC IT Security Review Cover
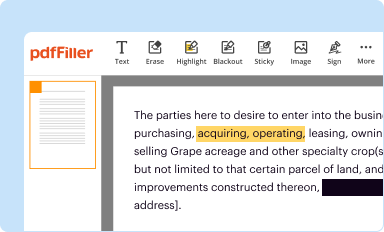
Edit your UNM HSC IT Security Review Cover form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
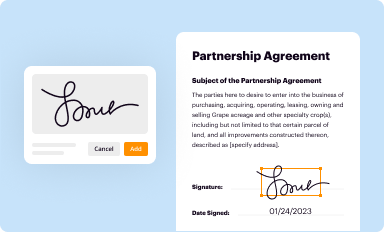
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
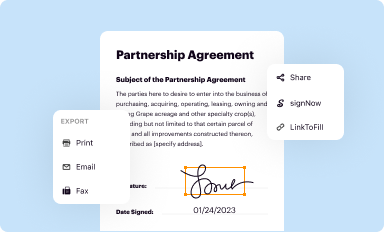
Share your form instantly
Email, fax, or share your UNM HSC IT Security Review Cover form via URL. You can also download, print, or export forms to your preferred cloud storage service.
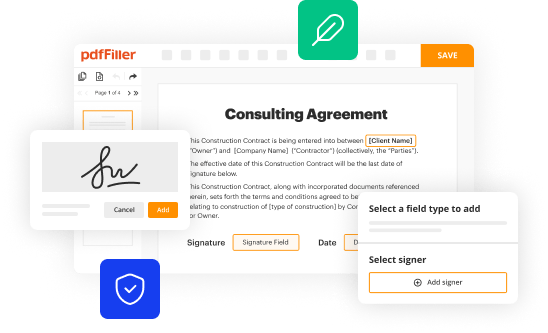
Editing UNM HSC IT Security Review Cover online
Follow the steps down below to benefit from a competent PDF editor:
1
Log in to account. Start Free Trial and register a profile if you don't have one.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit UNM HSC IT Security Review Cover. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Save your file. Select it in the list of your records. Then, move the cursor to the right toolbar and choose one of the available exporting methods: save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud.
It's easier to work with documents with pdfFiller than you could have believed. You can sign up for an account to see for yourself.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out UNM HSC IT Security Review Cover
How to fill out UNM HSC IT Security Review Cover Sheet
01
Download the UNM HSC IT Security Review Cover Sheet from the official website.
02
Provide the project name and a brief description of the project in the designated fields.
03
Fill in the date of submission.
04
Identify the stakeholders involved by listing their names and roles.
05
Complete the section regarding data classification, including the types of data being handled.
06
Answer all security-related questions honestly and thoroughly.
07
Attach any necessary supplementary documentation as required by the review process.
08
Review the entire cover sheet for accuracy and completeness before submission.
09
Submit the completed cover sheet to the appropriate IT security office.
Who needs UNM HSC IT Security Review Cover Sheet?
01
All departments and personnel at UNM HSC that are implementing new IT projects or handling sensitive data.
02
Researchers and administrative staff involved in projects that require access to or management of private or sensitive information.
03
Any individuals or teams that are introducing new technologies, processes, or systems likely to impact IT security.
Fill
form
: Try Risk Free






People Also Ask about
What is the purpose of an editing checklist?
Through a good editing checklist, you can edit content for blogs and other pieces efficiently. It also helps you produce work that resonates with your audience and helps them gain value from it.
What are the checklist for revising?
Revision Checklist What's the most important thing I want to say about my subject? Who am I writing this paper for? Why do I think the subject is worth writing about? What verb explains what I'm trying to do in this paper (tell a story, compare X and Y, describe Z)? Does my first paragraph answer questions 1-4?
How do you create an edit checklist?
Editing Checklist for Self-Editing or Peer Review Are there any run-on sentences? Are proper nouns capitalized? Are there any unnecessary capital letters? Are quotation marks in the right place? Are any sentences written in the passive voice? Are apostrophes in the right places? Are there any sentence fragments?
What are examples of peer editing?
For example, in a classroom setting, a teacher might create a peer editing assignment in which two students share their essays, revise each other's papers and later discuss their suggestions. This can help them improve each other's writing.
What is peer editing checklist?
Does the paper meet the length requirement? Does each subsection contain the appropriate information? Is any information missing from a subsection? Is there any information that needs to be moved to a different section?
What is an editing checklist?
An editing checklist is a one or two-page document that lists all of the issues to check for, while reviewing a piece. For example, instances of the passive voice, common spelling mistakes and so on. It also provides an overview of tone of voice and house style.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I edit UNM HSC IT Security Review Cover online?
The editing procedure is simple with pdfFiller. Open your UNM HSC IT Security Review Cover in the editor, which is quite user-friendly. You may use it to blackout, redact, write, and erase text, add photos, draw arrows and lines, set sticky notes and text boxes, and much more.
Can I edit UNM HSC IT Security Review Cover on an Android device?
You can edit, sign, and distribute UNM HSC IT Security Review Cover on your mobile device from anywhere using the pdfFiller mobile app for Android; all you need is an internet connection. Download the app and begin streamlining your document workflow from anywhere.
How do I complete UNM HSC IT Security Review Cover on an Android device?
Use the pdfFiller app for Android to finish your UNM HSC IT Security Review Cover. The application lets you do all the things you need to do with documents, like add, edit, and remove text, sign, annotate, and more. There is nothing else you need except your smartphone and an internet connection to do this.
What is UNM HSC IT Security Review Cover Sheet?
The UNM HSC IT Security Review Cover Sheet is a document used to assess the security of information technology projects and systems within the UNM Health Sciences Center.
Who is required to file UNM HSC IT Security Review Cover Sheet?
Any department or individual within the UNM Health Sciences Center that is initiating a new IT project or system involving sensitive data is required to file the cover sheet.
How to fill out UNM HSC IT Security Review Cover Sheet?
To fill out the UNM HSC IT Security Review Cover Sheet, provide detailed information about the IT project, including the purpose, data involved, potential risks, and security measures implemented.
What is the purpose of UNM HSC IT Security Review Cover Sheet?
The purpose of the UNM HSC IT Security Review Cover Sheet is to ensure that all IT projects comply with security policies and to identify any potential risks associated with handling sensitive information.
What information must be reported on UNM HSC IT Security Review Cover Sheet?
The information that must be reported includes project details, type of data handled, security controls in place, risk assessments, and any compliance requirements.
Fill out your UNM HSC IT Security Review Cover online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

UNM HSC IT Security Review Cover is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.