
Get the free Malicious Control System Cyber Security Attack Case Study
Show details
Malicious Control System Cybersecurity Attack Case Study
March Water Services, Australia1
Marshall Abrams, The MITE Corporation, Abrams×mite.org
Joe Weiss, Applied Control Solutions, Joe. Weiss×mealtimes.abstract
The
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign malicious control system cyber
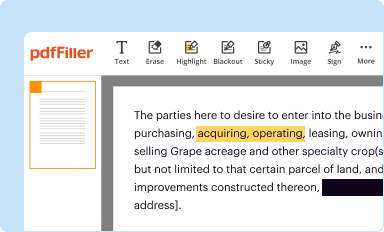
Edit your malicious control system cyber form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
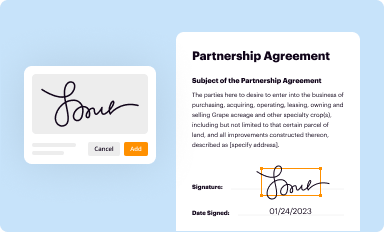
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
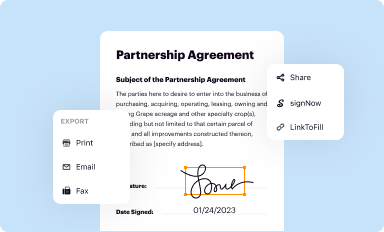
Share your form instantly
Email, fax, or share your malicious control system cyber form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit malicious control system cyber online
To use our professional PDF editor, follow these steps:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
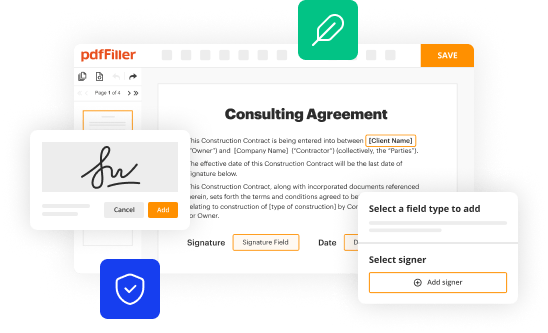
Edit malicious control system cyber. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out malicious control system cyber
How to fill out malicious control system cyber
01
To fill out a malicious control system cyber, follow these steps:
02
Identify the target system that you want to compromise.
03
Gather information about the vulnerabilities and weaknesses of the target system.
04
Choose a suitable exploit or attack technique to gain control over the system.
05
Develop or utilize a malware or remote access tool to establish control over the compromised system.
06
Test the malicious control system cyber to ensure its effectiveness and stealthiness.
07
Perform actions and commands through the control system to manipulate or harm the target system.
08
Continuously monitor and maintain access to the compromised system to avoid detection and defend against countermeasures.
09
Cover tracks and remove evidence of the malicious activities to maintain anonymity and avoid being traced back.
10
Please note that engaging in malicious activities, such as filling out a malicious control system cyber, is illegal and unethical. This answer is provided for educational purposes only.
Who needs malicious control system cyber?
01
Malicious control system cyber is typically sought after by individuals or groups with malicious intent, including:
02
- Hackers and cybercriminals who want to gain unauthorized access to systems for personal gain, such as stealing sensitive information or carrying out financial fraud.
03
- State-sponsored actors or intelligence agencies looking to conduct cyber espionage or sabotage operations against targeted organizations or countries.
04
- Competitors seeking to gain an advantage by compromising the systems of rival companies or organizations.
05
- Cybersecurity researchers and professionals who utilize controlled and isolated environments to study and understand the behavior of malicious control systems for defensive purposes.
06
It's important to emphasize that the use of malicious control systems is illegal and unethical. This answer is provided for informational purposes only.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I make changes in malicious control system cyber?
pdfFiller allows you to edit not only the content of your files, but also the quantity and sequence of the pages. Upload your malicious control system cyber to the editor and make adjustments in a matter of seconds. Text in PDFs may be blacked out, typed in, and erased using the editor. You may also include photos, sticky notes, and text boxes, among other things.
How do I make edits in malicious control system cyber without leaving Chrome?
Install the pdfFiller Chrome Extension to modify, fill out, and eSign your malicious control system cyber, which you can access right from a Google search page. Fillable documents without leaving Chrome on any internet-connected device.
Can I sign the malicious control system cyber electronically in Chrome?
Yes. By adding the solution to your Chrome browser, you can use pdfFiller to eSign documents and enjoy all of the features of the PDF editor in one place. Use the extension to create a legally-binding eSignature by drawing it, typing it, or uploading a picture of your handwritten signature. Whatever you choose, you will be able to eSign your malicious control system cyber in seconds.
What is malicious control system cyber?
Malicious control system cyber refers to unauthorized access or manipulation of computer systems controlling critical infrastructure.
Who is required to file malicious control system cyber?
Organizations operating critical infrastructure systems are required to file malicious control system cyber.
How to fill out malicious control system cyber?
Malicious control system cyber can be filled out online through the designated reporting portal.
What is the purpose of malicious control system cyber?
The purpose of malicious control system cyber is to identify and report any potential cyber threats to critical infrastructure systems.
What information must be reported on malicious control system cyber?
Information such as details of the cyber incident, impact on critical infrastructure, and any remediation steps taken must be reported on malicious control system cyber.
Fill out your malicious control system cyber online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Malicious Control System Cyber is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















