Get the free Common Key Service Implementation Guide - NJII
Show details
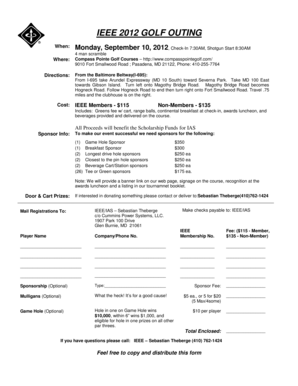
New Jersey Health Information NetworkCommon Key Service
Implementation GuideVersion 1
December 19, 2016For information visit www.njii.com/NJHIN
Proprietary Information New Jersey Health Information
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign common key service implementation

Edit your common key service implementation form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your common key service implementation form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit common key service implementation online
To use our professional PDF editor, follow these steps:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit common key service implementation. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
It's easier to work with documents with pdfFiller than you can have ever thought. You can sign up for an account to see for yourself.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out common key service implementation

How to fill out common key service implementation
01
First, identify the common key service implementation that you need to fill out.
02
Gather all the necessary information and documentation required to complete the form.
03
Ensure that you have access to the relevant systems or platforms where the common key service implementation needs to be implemented.
04
Follow the guidelines or instructions provided by the service provider or organization offering the common key service implementation.
05
Carefully fill out each point in the form, ensuring accuracy and completeness.
06
Double-check all the information provided before submitting the form.
07
If there are any specific requirements or additional details needed, make sure to include them.
08
Submit the completed common key service implementation form through the designated channel or platform.
09
Wait for confirmation or feedback from the service provider or organization regarding the status of your implementation.
10
Follow up or make any necessary adjustments based on the response received.
Who needs common key service implementation?
01
Organizations or businesses that require a standardized approach to implement common keys across different systems or platforms.
02
Software developers or IT professionals who need to ensure seamless integration between different services or applications.
03
Any individual or entity looking to establish a consistent and secure method of identifying and accessing shared resources or data.
04
Companies or institutions that collaborate with multiple external partners and need a unified method of sharing keys or credentials.
05
Government agencies or departments that handle sensitive information and require a standardized approach to access control and authentication.
06
Industries or sectors that prioritize data privacy and security, such as finance, healthcare, or technology.
07
Any individual or organization seeking to streamline processes and enhance efficiency through a common key service implementation.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Can I create an electronic signature for signing my common key service implementation in Gmail?
You can easily create your eSignature with pdfFiller and then eSign your common key service implementation directly from your inbox with the help of pdfFiller’s add-on for Gmail. Please note that you must register for an account in order to save your signatures and signed documents.
Can I edit common key service implementation on an iOS device?
Create, edit, and share common key service implementation from your iOS smartphone with the pdfFiller mobile app. Installing it from the Apple Store takes only a few seconds. You may take advantage of a free trial and select a subscription that meets your needs.
How can I fill out common key service implementation on an iOS device?
Install the pdfFiller iOS app. Log in or create an account to access the solution's editing features. Open your common key service implementation by uploading it from your device or online storage. After filling in all relevant fields and eSigning if required, you may save or distribute the document.
What is common key service implementation?
Common key service implementation is the process of establishing a standard key management system for encryption and decryption of data within an organization.
Who is required to file common key service implementation?
Typically, IT security managers or data protection officers are responsible for filing common key service implementation.
How to fill out common key service implementation?
Common key service implementation can be filled out by documenting the encryption and decryption processes used, key management procedures, and any security measures in place.
What is the purpose of common key service implementation?
The purpose of common key service implementation is to ensure secure and efficient encryption and decryption of sensitive data.
What information must be reported on common key service implementation?
Information such as encryption algorithms used, key management practices, access control measures, and audit trails must be reported on common key service implementation.
Fill out your common key service implementation online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Common Key Service Implementation is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.