
Get the free Automated Method for Identifying and Prioritizing Project - csse usc
Show details
References Boehm B. W. 1989. Software Risk Management. IEEE Computer Society Press Washington D.C. Charette R.N. 1989. 1 3 - Cooyright d 1993 by Cr gorv A. Toth. All lie has ReserVed. x l t l l s k Advisor Recalculate llsksl Off - n A u t o - R e c a I c a l a t l Risks ProJeclc SIze 1 Ve - a. e. 2. Expert COCOMO Madachy 1994 has extended Mitre s work on ESCOMO Day 1987 by developing a addition to computing intermediate COCOMO results from user inputs Madachy s tool schedule and a highly...
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign automated method for identifying
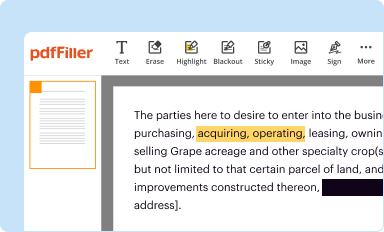
Edit your automated method for identifying form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
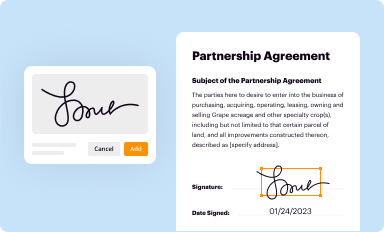
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
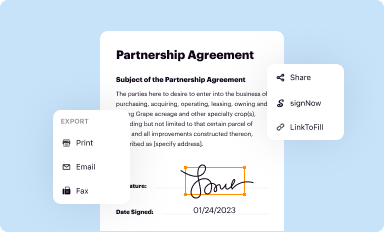
Share your form instantly
Email, fax, or share your automated method for identifying form via URL. You can also download, print, or export forms to your preferred cloud storage service.
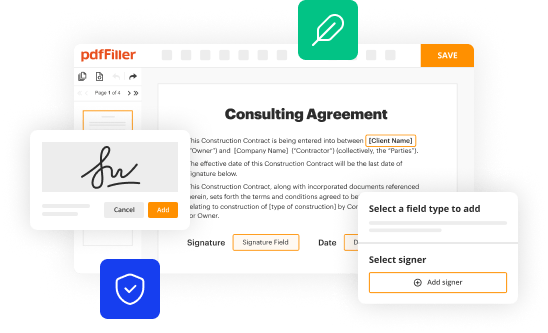
Editing automated method for identifying online
Follow the guidelines below to benefit from a competent PDF editor:
1
Check your account. In case you're new, it's time to start your free trial.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit automated method for identifying. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
With pdfFiller, it's always easy to deal with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out automated method for identifying
How to fill out automated method for identifying
01
Start by understanding the purpose of the automated method for identifying. What are the specific goals it should achieve?
02
Gather all the necessary information and data that will be used in the identification process.
03
Determine the criteria or characteristics that will be used to identify the desired information or individuals.
04
Choose an appropriate automated method or tool that is capable of efficiently analyzing the data and applying the identification criteria.
05
Configure the automated method by inputting the necessary parameters and settings.
06
Test the automated method using a small subset of the data to ensure it produces accurate results.
07
If needed, refine the identification criteria or adjust the parameters of the automated method to improve its performance.
08
Once satisfied with the results, apply the automated method to the complete dataset or ongoing identification tasks.
09
Regularly monitor the performance of the automated method and make necessary adjustments as new data becomes available.
10
Document the entire process of using the automated method for identifying, including the steps taken and the results obtained.
Who needs automated method for identifying?
01
Organizations dealing with large volumes of data and requiring efficient identification processes.
02
Law enforcement agencies aiming to identify potential suspects or individuals of interest from vast databases.
03
Government agencies involved in intelligence gathering and threat identification.
04
Companies seeking to automate their customer identification and verification processes for various purposes.
05
Researchers working with extensive datasets and needing to identify specific patterns or individuals.
06
Medical institutions looking to automate the identification of diseases or medical conditions based on patient data.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I manage my automated method for identifying directly from Gmail?
The pdfFiller Gmail add-on lets you create, modify, fill out, and sign automated method for identifying and other documents directly in your email. Click here to get pdfFiller for Gmail. Eliminate tedious procedures and handle papers and eSignatures easily.
How do I execute automated method for identifying online?
pdfFiller makes it easy to finish and sign automated method for identifying online. It lets you make changes to original PDF content, highlight, black out, erase, and write text anywhere on a page, legally eSign your form, and more, all from one place. Create a free account and use the web to keep track of professional documents.
How can I fill out automated method for identifying on an iOS device?
Download and install the pdfFiller iOS app. Then, launch the app and log in or create an account to have access to all of the editing tools of the solution. Upload your automated method for identifying from your device or cloud storage to open it, or input the document URL. After filling out all of the essential areas in the document and eSigning it (if necessary), you may save it or share it with others.
Fill out your automated method for identifying online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Automated Method For Identifying is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















