Get the free STUDENT SECURITY BREACH PROCEDURES
Show details
STUDENT SECURITY BREACH PROCEDURES
The following Student Security Breach Procedures have been developed to assist schools
when dealing with security breaches of DENSE laptops. The new procedures,
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign student security breach procedures
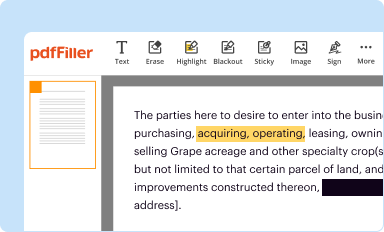
Edit your student security breach procedures form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
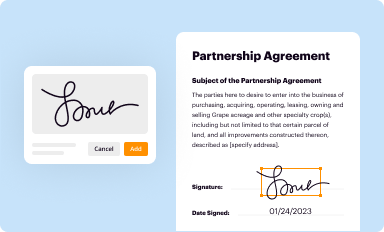
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
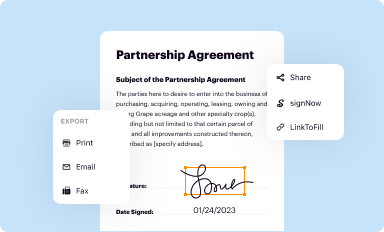
Share your form instantly
Email, fax, or share your student security breach procedures form via URL. You can also download, print, or export forms to your preferred cloud storage service.
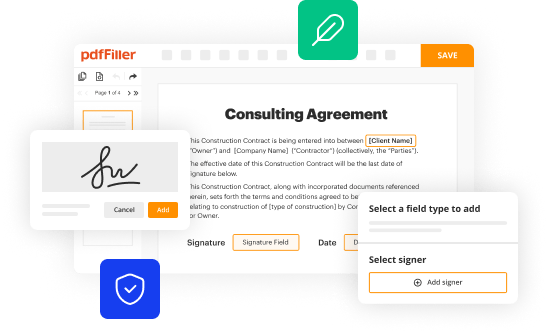
How to edit student security breach procedures online
To use the services of a skilled PDF editor, follow these steps:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit student security breach procedures. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out student security breach procedures
How to fill out student security breach procedures
01
Step 1: Gather all necessary information about the student security breach, including the date, time, and location of the incident.
02
Step 2: Determine the extent of the breach and evaluate the potential impact on the affected students.
03
Step 3: Notify the appropriate authorities, such as the school administration, IT department, or data protection officer.
04
Step 4: Follow any specific procedures or protocols established by your educational institution for reporting and documenting security breaches.
05
Step 5: Provide support to the affected students, such as offering counseling services or resources to address any potential emotional or psychological impacts.
06
Step 6: Take immediate action to mitigate the breach, such as implementing additional security measures, updating passwords, or securing affected systems.
07
Step 7: Conduct a thorough investigation to identify the cause of the breach and prevent similar incidents in the future.
08
Step 8: Evaluate and review existing student security policies and procedures to identify areas for improvement and make necessary updates.
09
Step 9: Communicate the breach and subsequent actions taken to parents, guardians, and relevant stakeholders to maintain transparency and trust.
10
Step 10: Continuously monitor and assess the effectiveness of the implemented security measures to ensure student data remains secure.
Who needs student security breach procedures?
01
Educational institutions, such as schools, colleges, and universities, need student security breach procedures to protect the personal and sensitive information of their students.
02
School administrators and staff responsible for student data management and privacy must adhere to these procedures to prevent, detect, and respond to security breaches.
03
Data protection officers or IT professionals employed by educational institutions are tasked with developing and implementing student security breach procedures.
04
Parents and guardians of students have a vested interest in ensuring that their children's personal information is handled securely and that procedures are in place to address any breaches.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I modify my student security breach procedures in Gmail?
It's easy to use pdfFiller's Gmail add-on to make and edit your student security breach procedures and any other documents you get right in your email. You can also eSign them. Take a look at the Google Workspace Marketplace and get pdfFiller for Gmail. Get rid of the time-consuming steps and easily manage your documents and eSignatures with the help of an app.
How can I get student security breach procedures?
It's simple with pdfFiller, a full online document management tool. Access our huge online form collection (over 25M fillable forms are accessible) and find the student security breach procedures in seconds. Open it immediately and begin modifying it with powerful editing options.
How do I execute student security breach procedures online?
Filling out and eSigning student security breach procedures is now simple. The solution allows you to change and reorganize PDF text, add fillable fields, and eSign the document. Start a free trial of pdfFiller, the best document editing solution.
What is student security breach procedures?
Student security breach procedures are protocols put in place to address and mitigate security breaches involving student data.
Who is required to file student security breach procedures?
School administrators and data protection officers are usually responsible for filing student security breach procedures.
How to fill out student security breach procedures?
Student security breach procedures should be filled out with detailed information about the breach, the actions taken to address it, and steps to prevent future breaches.
What is the purpose of student security breach procedures?
The purpose of student security breach procedures is to protect student data, comply with data protection laws, and maintain trust with students and their families.
What information must be reported on student security breach procedures?
Student security breach procedures typically require reporting the nature of the breach, the data compromised, the individuals affected, and any remedial actions taken.
Fill out your student security breach procedures online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Student Security Breach Procedures is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.