Get the free Security Systems Engineering Approach in
Show details
Interested in learning
more about security?SANS Institute
InfoSec Reading Room
This paper is from the SANS Institute Reading Room site. Reposting is not permitted without express written permission.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign security systems engineering approach
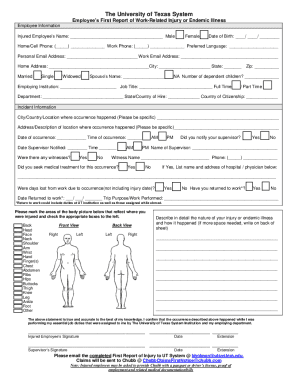
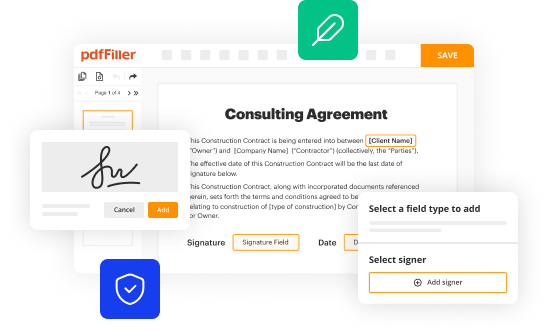
Edit your security systems engineering approach form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
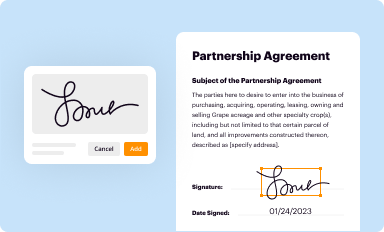
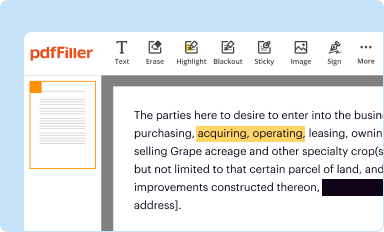
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
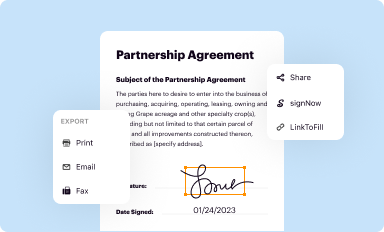
Share your form instantly
Email, fax, or share your security systems engineering approach form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit security systems engineering approach online
To use our professional PDF editor, follow these steps:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit security systems engineering approach. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
It's easier to work with documents with pdfFiller than you could have ever thought. You may try it out for yourself by signing up for an account.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out security systems engineering approach
How to fill out security systems engineering approach
01
Identify the objectives and requirements for the security system
02
Conduct a comprehensive assessment of the existing security infrastructure
03
Define the threat landscape and risk factors
04
Formulate an architectural design for the security system
05
Select appropriate security technologies and tools
06
Implement the security measures and controls
07
Regularly review and update the security system
08
Perform continuous monitoring and testing of the system
09
Establish incident response procedures
10
Document the entire process for future reference
Who needs security systems engineering approach?
01
Organizations that deal with sensitive data or valuable assets
02
Government agencies and defense organizations
03
Businesses operating in high-risk industries
04
Financial institutions and banks
05
Healthcare facilities and hospitals
06
Critical infrastructure providers
07
Large enterprises with a complex IT infrastructure
08
Any organization concerned about potential security threats
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I edit security systems engineering approach from Google Drive?
Using pdfFiller with Google Docs allows you to create, amend, and sign documents straight from your Google Drive. The add-on turns your security systems engineering approach into a dynamic fillable form that you can manage and eSign from anywhere.
How do I complete security systems engineering approach online?
Completing and signing security systems engineering approach online is easy with pdfFiller. It enables you to edit original PDF content, highlight, blackout, erase and type text anywhere on a page, legally eSign your form, and much more. Create your free account and manage professional documents on the web.
Can I sign the security systems engineering approach electronically in Chrome?
You certainly can. You get not just a feature-rich PDF editor and fillable form builder with pdfFiller, but also a robust e-signature solution that you can add right to your Chrome browser. You may use our addon to produce a legally enforceable eSignature by typing, sketching, or photographing your signature with your webcam. Choose your preferred method and eSign your security systems engineering approach in minutes.
What is security systems engineering approach?
The security systems engineering approach is a methodology used to design, implement, and maintain secure systems in order to protect valuable assets from unauthorized access or harm.
Who is required to file security systems engineering approach?
Organizations that handle sensitive information or operate critical infrastructure may be required to file a security systems engineering approach as part of their security measures.
How to fill out security systems engineering approach?
To fill out a security systems engineering approach, organizations must assess their security needs, identify potential threats, and implement appropriate security measures to mitigate risks.
What is the purpose of security systems engineering approach?
The purpose of a security systems engineering approach is to ensure that systems are designed and implemented in a way that protects against security threats and vulnerabilities.
What information must be reported on security systems engineering approach?
The information reported on a security systems engineering approach may include risk assessments, security controls, incident response plans, and security architecture diagrams.
Fill out your security systems engineering approach online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Security Systems Engineering Approach is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.