Get the free Analyzing Targeted Attacks
Show details
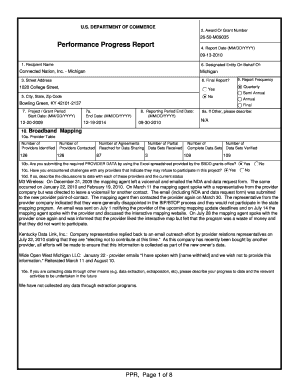
Analyzing Targeted Attacks through Hired An IOC Management and Visualization Tool Hiroshi Soda Incident Response Group, CERT/Coordination CenterAgenda 1. Advanced attacks specifically targeting Japanese
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign analyzing targeted attacks

Edit your analyzing targeted attacks form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your analyzing targeted attacks form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit analyzing targeted attacks online
Follow the steps below to benefit from a competent PDF editor:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit analyzing targeted attacks. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
It's easier to work with documents with pdfFiller than you could have believed. Sign up for a free account to view.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out analyzing targeted attacks

How to fill out analyzing targeted attacks
01
Step 1: Start by gathering information about the targeted attack, such as the nature of the attack, the affected systems, and any available evidence.
02
Step 2: Analyze the attack vectors used, such as email phishing, social engineering, or malware injection.
03
Step 3: Examine the malware or malicious files involved in the attack using an appropriate sandboxing or virtual machine environment.
04
Step 4: Investigate the command and control infrastructure used by the attackers to communicate with the compromised systems.
05
Step 5: Analyze the network traffic generated during the attack to identify any patterns or anomalies.
06
Step 6: Look for indicators of compromise (IOCs) that can help identify similar attacks or related threat actors.
07
Step 7: Combine the gathered information and analysis results to create a comprehensive report detailing the targeted attack.
Who needs analyzing targeted attacks?
01
Organizations that have experienced a targeted attack and want to understand the scope and impact of the breach.
02
Security professionals who are responsible for incident response and need to analyze and mitigate targeted attacks.
03
Cybersecurity researchers who are interested in studying the techniques and tactics used by threat actors in targeted attacks.
04
Government agencies or law enforcement organizations investigating cybercrimes and need to analyze the details of targeted attacks.
05
Security vendors who develop and provide solutions for detecting and preventing targeted attacks.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Can I create an electronic signature for the analyzing targeted attacks in Chrome?
Yes. By adding the solution to your Chrome browser, you can use pdfFiller to eSign documents and enjoy all of the features of the PDF editor in one place. Use the extension to create a legally-binding eSignature by drawing it, typing it, or uploading a picture of your handwritten signature. Whatever you choose, you will be able to eSign your analyzing targeted attacks in seconds.
Can I create an eSignature for the analyzing targeted attacks in Gmail?
Upload, type, or draw a signature in Gmail with the help of pdfFiller’s add-on. pdfFiller enables you to eSign your analyzing targeted attacks and other documents right in your inbox. Register your account in order to save signed documents and your personal signatures.
How do I fill out analyzing targeted attacks using my mobile device?
Use the pdfFiller mobile app to complete and sign analyzing targeted attacks on your mobile device. Visit our web page (https://edit-pdf-ios-android.pdffiller.com/) to learn more about our mobile applications, the capabilities you’ll have access to, and the steps to take to get up and running.
What is analyzing targeted attacks?
Analyzing targeted attacks is the process of examining, investigating, and understanding cyberattacks that specifically target an individual, organization, or system.
Who is required to file analyzing targeted attacks?
Organizations and individuals who are victims of targeted attacks are required to file analyzing targeted attacks reports.
How to fill out analyzing targeted attacks?
Analyzing targeted attacks reports can be filled out by providing details about the attack, methods used, impact on the system, and any relevant information.
What is the purpose of analyzing targeted attacks?
The purpose of analyzing targeted attacks is to understand the tactics, techniques, and motives of cyber attackers in order to enhance cybersecurity measures.
What information must be reported on analyzing targeted attacks?
Information such as the type of attack, attack vector, date and time of the attack, affected systems, and any indicators of compromise must be reported on analyzing targeted attacks.
Fill out your analyzing targeted attacks online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Analyzing Targeted Attacks is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.