Get the free Using SSH Secure Shell Client for FTP
Show details
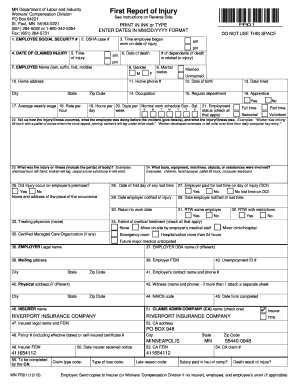
Using SSH Secure Shell Client for FTP
The SSH Secure Shell for Workstations Windows client application features a secure and easy file transfer protocol.
Access the SSH Secure FTP by double-clicking
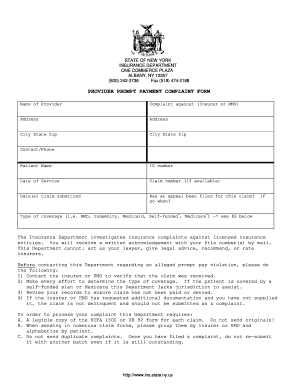
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign using ssh secure shell

Edit your using ssh secure shell form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your using ssh secure shell form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit using ssh secure shell online
Follow the guidelines below to benefit from the PDF editor's expertise:
1
Sign into your account. If you don't have a profile yet, click Start Free Trial and sign up for one.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit using ssh secure shell. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
With pdfFiller, it's always easy to work with documents. Check it out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out using ssh secure shell

How to fill out using ssh secure shell
01
Open your SSH client (such as PuTTY or Terminal on Mac/Linux).
02
Enter the IP address or domain name of the remote server you want to connect to.
03
Specify the port number if it's different from the default (port 22).
04
Choose the SSH protocol version (typically SSH2).
05
Click or press Enter to initiate the connection.
06
Enter your username and password when prompted.
07
Once connected, you can use various SSH commands to interact with the remote server.
08
To fill out using SSH secure shell, navigate to the desired directory or file location where you want to make changes.
09
Use the appropriate command-line text editor (such as vi or nano) to open the file you wish to fill out.
10
Make the necessary edits to the file using the text editor.
11
Save the changes and exit the text editor.
12
Close the SSH session when you're done filling out the file.
Who needs using ssh secure shell?
01
Developers and programmers who need secure remote access to servers for managing and maintaining software applications.
02
System administrators who need to perform administrative tasks on remote servers securely.
03
IT professionals who need to transfer files securely between systems using the SFTP (SSH File Transfer Protocol).
04
Anyone who wants to securely access and manage a remote server without exposing sensitive information over insecure networks.
05
Individuals and organizations who value data privacy and security in their remote server interactions.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Where do I find using ssh secure shell?
It's simple using pdfFiller, an online document management tool. Use our huge online form collection (over 25M fillable forms) to quickly discover the using ssh secure shell. Open it immediately and start altering it with sophisticated capabilities.
How do I edit using ssh secure shell in Chrome?
Download and install the pdfFiller Google Chrome Extension to your browser to edit, fill out, and eSign your using ssh secure shell, which you can open in the editor with a single click from a Google search page. Fillable documents may be executed from any internet-connected device without leaving Chrome.
How do I fill out the using ssh secure shell form on my smartphone?
You can easily create and fill out legal forms with the help of the pdfFiller mobile app. Complete and sign using ssh secure shell and other documents on your mobile device using the application. Visit pdfFiller’s webpage to learn more about the functionalities of the PDF editor.
What is using ssh secure shell?
Using SSH Secure Shell is a network protocol that allows secure communication between two devices over an insecure network.
Who is required to file using ssh secure shell?
Anyone who needs to securely communicate and transfer data between devices over a network may be required to use SSH Secure Shell.
How to fill out using ssh secure shell?
To use SSH Secure Shell, users need to have SSH client software installed on their device and access to a device with SSH server software running.
What is the purpose of using ssh secure shell?
The purpose of using SSH Secure Shell is to encrypt data and provide a secure way to communicate and transfer files over a network.
What information must be reported on using ssh secure shell?
When using SSH Secure Shell, users must report login credentials, encryption keys, and any other information necessary for secure communication.
Fill out your using ssh secure shell online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Using Ssh Secure Shell is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.