Get the free Internet (In)Security Exposed - thomas duebendorfer
Show details
Internet (In)Security Exposed
Zweitageskurs EU Internetsicherheit in Theories UND Praxis
Her Kurt word aground her Anchorage berates sum written MAL durchgefhrt.
Security Experten von Google UND ETH
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign internet insecurity exposed
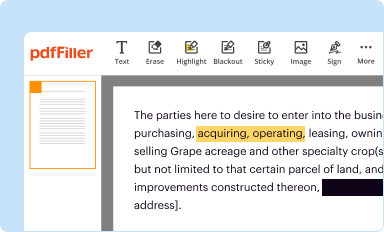
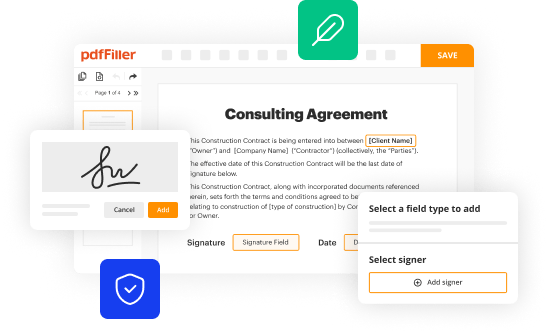
Edit your internet insecurity exposed form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
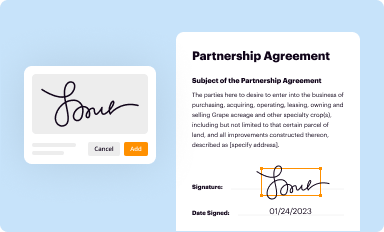
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
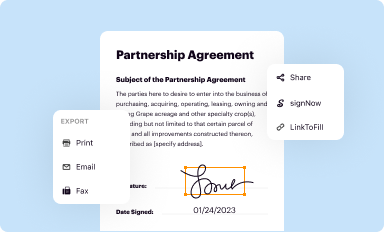
Share your form instantly
Email, fax, or share your internet insecurity exposed form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit internet insecurity exposed online
To use our professional PDF editor, follow these steps:
1
Check your account. If you don't have a profile yet, click Start Free Trial and sign up for one.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit internet insecurity exposed. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
Dealing with documents is simple using pdfFiller. Try it right now!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out internet insecurity exposed
How to fill out internet insecurity exposed
01
Start by researching different sources of information on internet insecurity.
02
Familiarize yourself with common types of online threats such as malware, phishing, and data breaches.
03
Take steps to secure your devices by using strong and unique passwords, keeping your software up to date, and avoiding suspicious websites.
04
Educate yourself on safe browsing habits and recognize the signs of a secure website.
05
Be cautious when sharing personal information online and avoid clicking on suspicious links or downloading unknown files.
06
Consider using a reliable antivirus program and a virtual private network (VPN) to protect your online activities.
07
Regularly backup your important data and enable two-factor authentication for your accounts.
08
Stay informed about the latest internet security trends and best practices to stay one step ahead of potential threats.
Who needs internet insecurity exposed?
01
Individuals who use the internet for various purposes, including personal, professional, and financial activities.
02
Businesses that rely on online platforms to conduct their operations and manage sensitive data.
03
Organizations and institutions that handle confidential and private information, such as government agencies, healthcare providers, and financial institutions.
04
Internet users who want to protect their privacy and safeguard their personal information from cybercriminals.
05
Individuals or groups who are concerned about the increasing prevalence of cyber attacks and want to stay informed about internet security.
06
Students and educators who need to understand internet security to prevent cyberbullying and ensure a safe online learning environment.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I edit internet insecurity exposed from Google Drive?
Simplify your document workflows and create fillable forms right in Google Drive by integrating pdfFiller with Google Docs. The integration will allow you to create, modify, and eSign documents, including internet insecurity exposed, without leaving Google Drive. Add pdfFiller’s functionalities to Google Drive and manage your paperwork more efficiently on any internet-connected device.
How do I edit internet insecurity exposed online?
The editing procedure is simple with pdfFiller. Open your internet insecurity exposed in the editor, which is quite user-friendly. You may use it to blackout, redact, write, and erase text, add photos, draw arrows and lines, set sticky notes and text boxes, and much more.
How can I edit internet insecurity exposed on a smartphone?
You can easily do so with pdfFiller's apps for iOS and Android devices, which can be found at the Apple Store and the Google Play Store, respectively. You can use them to fill out PDFs. We have a website where you can get the app, but you can also get it there. When you install the app, log in, and start editing internet insecurity exposed, you can start right away.
What is internet insecurity exposed?
Internet insecurity exposed refers to the vulnerabilities and risks associated with using the internet, such as data breaches, cyber attacks, and privacy concerns.
Who is required to file internet insecurity exposed?
Businesses, organizations, and individuals who have experienced internet insecurity incidents are required to file internet insecurity exposed reports.
How to fill out internet insecurity exposed?
To fill out an internet insecurity exposed report, one must provide details of the incident, including when it occurred, how it was discovered, and what steps were taken to mitigate the damage.
What is the purpose of internet insecurity exposed?
The purpose of internet insecurity exposed reports is to increase transparency and awareness of cyber threats, and to help prevent future incidents.
What information must be reported on internet insecurity exposed?
Information that must be reported on internet insecurity exposed includes the type of incident, the impact on affected parties, and any security measures in place at the time of the incident.
Fill out your internet insecurity exposed online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Internet Insecurity Exposed is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.