Get the free HACKING FOR
Show details
HACKING FOR
SUSTAINABILITY
JORGE LUIS ZAPICODoctoral Thesis in
Media Technology and Graphic Production
Stockholm, Sweden, 2014HACKING FOR SUSTAINABILITYTitle: Hacking for Sustainability
Author: Jorge
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign hacking for
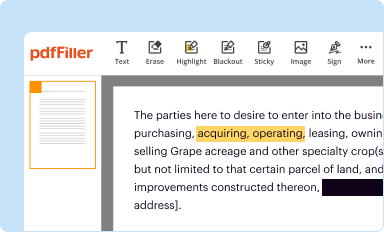
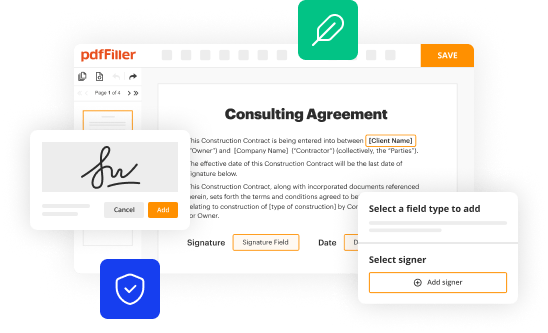
Edit your hacking for form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
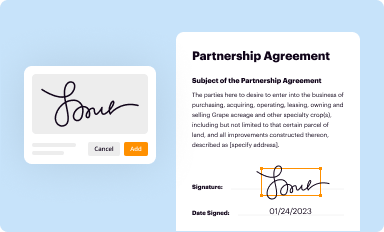
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
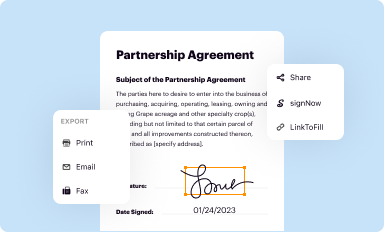
Share your form instantly
Email, fax, or share your hacking for form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit hacking for online
Follow the guidelines below to benefit from the PDF editor's expertise:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit hacking for. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
With pdfFiller, it's always easy to work with documents. Try it!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out hacking for
How to fill out hacking for
01
Step 1: Start by gathering all the necessary information and tools for hacking.
02
Step 2: Familiarize yourself with the target system or network that you intend to hack.
03
Step 3: Identify any vulnerabilities or weaknesses in the target system that can be exploited.
04
Step 4: Plan your attack strategy and determine your objectives.
05
Step 5: Use appropriate hacking techniques and tools to exploit the identified vulnerabilities.
06
Step 6: Gain unauthorized access to the target system or network.
07
Step 7: Maintain persistence and avoid detection while extracting or manipulating data.
08
Step 8: Cover your tracks to leave minimal evidence of your hacking activities.
09
Step 9: Use the extracted information for your intended purpose, such as exposing security flaws or gaining unauthorized benefits.
10
Step 10: Always remember to act within legal boundaries and obtain proper authorization before conducting any hacking activities.
Who needs hacking for?
01
Ethical hackers: Individuals or organizations who want to evaluate the security of their own systems or networks.
02
Penetration testers: Professionals hired to assess the vulnerabilities of systems or networks for clients.
03
Law enforcement agencies: Authorities who investigate cybercrimes and need to understand hacking techniques.
04
Cybersecurity researchers: Experts who study hacking methods to develop preventive measures and enhance security.
05
Government agencies: Organizations responsible for protecting national security and securing critical infrastructure.
06
Security professionals: Individuals involved in securing systems and networks from unauthorized access or data breaches.
07
White hat hackers: Good-intentioned hackers who use their skills to help identify and fix security flaws.
08
Red teamers: Professionals tasked with simulating real-world attacks to test the effectiveness of defensive measures.
09
Individuals seeking knowledge: Anyone interested in learning about hacking techniques, either for personal development or understanding potential threats.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I fill out the hacking for form on my smartphone?
Use the pdfFiller mobile app to complete and sign hacking for on your mobile device. Visit our web page (https://edit-pdf-ios-android.pdffiller.com/) to learn more about our mobile applications, the capabilities you’ll have access to, and the steps to take to get up and running.
How do I edit hacking for on an Android device?
Yes, you can. With the pdfFiller mobile app for Android, you can edit, sign, and share hacking for on your mobile device from any location; only an internet connection is needed. Get the app and start to streamline your document workflow from anywhere.
How do I complete hacking for on an Android device?
Use the pdfFiller mobile app to complete your hacking for on an Android device. The application makes it possible to perform all needed document management manipulations, like adding, editing, and removing text, signing, annotating, and more. All you need is your smartphone and an internet connection.
What is hacking for?
Hacking is typically done with the goal of gaining unauthorized access to computer systems or networks.
Who is required to file hacking for?
Individuals or organizations who have been victims of hacking are required to file a report.
How to fill out hacking for?
When filling out a hacking report, include details such as the date and time of the hacking incident, the type of attack, potential impact, and any known vulnerabilities exploited.
What is the purpose of hacking for?
The purpose of filing a hacking report is to document and report security breaches, help prevent future attacks, and potentially investigate and prosecute the perpetrators.
What information must be reported on hacking for?
Information such as the date and time of the incident, the type of attack, potential impact, and any known vulnerabilities exploited must be reported on a hacking report.
Fill out your hacking for online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Hacking For is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.