Last updated on Apr 10, 2026
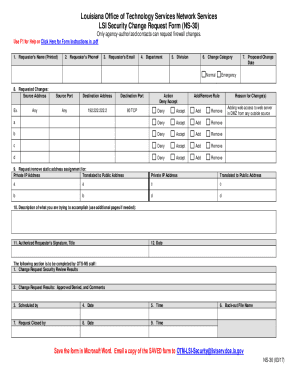
LA NS-30 formerly OTM-30 free printable template
pdfFiller is not affiliated with any government organization
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.
What is LA NS-30 formerly OTM-30
The LSI Security Change Request Form is a government document used by authorized agency contacts in Louisiana to request firewall modifications.
pdfFiller scores top ratings on review platforms




Who needs LA NS-30 formerly OTM-30?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to LA NS-30 formerly OTM-30
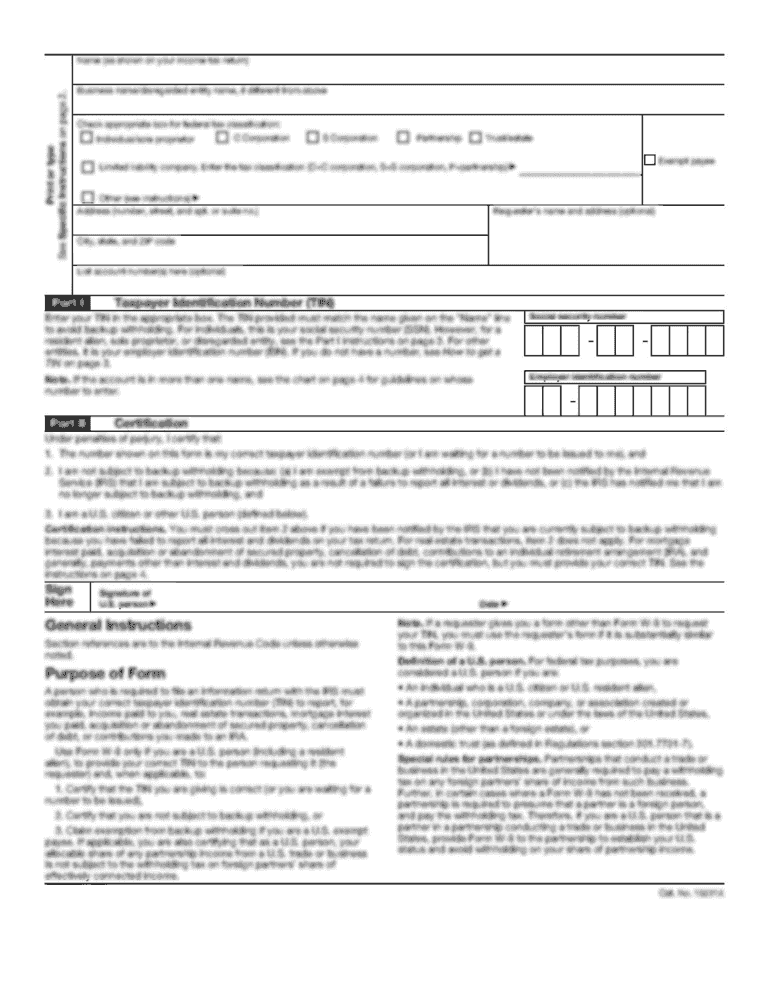
What is the LSI Security Change Request Form?
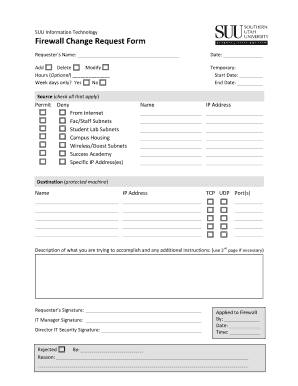
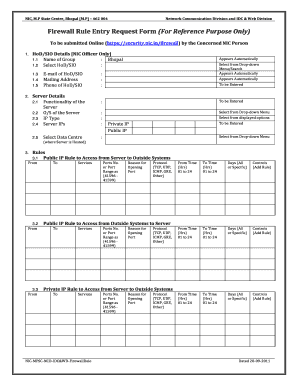
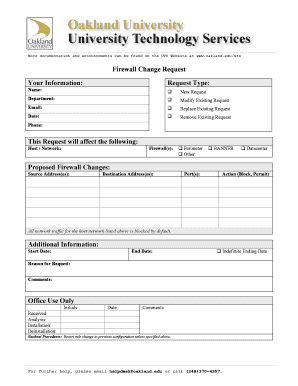
The LSI Security Change Request Form, commonly referred to as the OTM 30 form, serves a crucial function for Louisiana state agencies. This form is designed for agency-authorized contacts who need to request changes related to security protocols, particularly firewall configurations.
By filling out this essential document, users ensure that their requests are documented and processed correctly, safeguarding the interests of their respective agencies. The accuracy and completeness of this form can significantly impact its approval, making it indispensable in maintaining robust security measures.
Purpose and Benefits of the LSI Security Change Request Form
The primary purpose of submitting the LSI Security Change Request Form is to formalize requests for firewall changes necessary for maintaining security. Users must submit this form to mitigate risks and align with compliance requirements.
Properly filling out and submitting the form brings various benefits, including:
-
Enhanced security through timely updates to firewall settings.
-
Compliance with state regulations and internal policies.
-
Streamlined communication with OTM staff, reducing the chances of misunderstandings.
Who Needs the LSI Security Change Request Form?
The LSI Security Change Request Form is primarily utilized by agency-authorized contacts who have specific roles within the security change process. These roles include the Requester, who completes and signs the form, and the OTM Staff, who reviews the submission.
Understanding the responsibilities of each participant ensures that the form is handled appropriately and efficiently. For instance, the Requester must be knowledgeable about their agency's needs, while OTM Staff must be equipped to assess the implications of the requested changes.
How to Fill Out the LSI Security Change Request Form Online (Step-by-Step)
Filling out the LSI Security Change Request Form online is a straightforward process, particularly when using pdfFiller. Follow these steps to ensure accuracy:
-
Access the LSI Security Change Request Form through the pdfFiller platform.
-
Complete the personal information fields, including the requester's name and contact information.
-
Detail the requested changes in the designated section of the form.
-
Review all entries for correctness before signing.
-
Submit the form electronically to the appropriate OTM staff for processing.
Field-by-Field Instructions for the LSI Security Change Request Form
The LSI Security Change Request Form contains several specific fields that need careful attention. Key fields include:
-
Requester's Name: Enter your name clearly, printed for clarity.
-
Authorized Requester's Signature: Ensure you sign the form as required.
-
Title: Include your position to validate your authorization.
Providing accurate information in these fields is vital for the approval process, as it demonstrates the legitimacy of the request and the authority of the requester.
Review and Validation Checklist for Your Submission
Before submitting the LSI Security Change Request Form, conducting a comprehensive review is crucial. Here are essential checks users should perform:
-
Ensure all fields are completed accurately, including the requester's information and proposed changes.
-
Double-check for spelling errors and ensure clarity in your requests.
-
Verify that the form is signed by the authorized requester.
A thorough validation process can increase the chances of approval and reduce the likelihood of delays due to errors.
Submission Methods for the LSI Security Change Request Form
The LSI Security Change Request Form can be submitted through various methods, depending on the agency's preferences and policies. Available submission channels include:
-
Online submission via pdfFiller, ensuring quick processing.
-
Physical submission through the designated agency channels for those preferring paper forms.
Make sure to follow the instructions carefully for each method to guarantee that your submission is delivered successfully.
What Happens After You Submit the LSI Security Change Request Form?
After submitting the LSI Security Change Request Form, users can expect to navigate the approval process. Typically, the OTM staff will evaluate the request and notify the requester of the outcome.
Be aware of the following steps after submission:
-
If approved, expect a confirmation and further instructions regarding the implementation of the requested changes.
-
If denied, review the feedback provided to understand the reasons and potentially amend the submission before resending.
Security and Compliance for the LSI Security Change Request Form
Submitting sensitive documents like the LSI Security Change Request Form requires robust security measures. pdfFiller utilizes 256-bit encryption and complies with standards like HIPAA and GDPR to ensure document safety.
When submitting the form, users can be assured that their information is protected throughout the entire process, aligning with necessary compliance regulations.
Experience Seamless Submission with pdfFiller
Utilizing pdfFiller for the LSI Security Change Request Form streamlines the entire form-filling process. The platform offers a user-friendly interface, making it easy to edit, fill, and submit critical forms securely.
By leveraging the platform’s capabilities, users can enjoy a reliable and efficient experience, ensuring that critical security requests are submitted with confidence and ease.
How to fill out the LA NS-30 formerly OTM-30
-
1.Access pdfFiller and search for 'LSI Security Change Request Form' in the document library to find the form easily.
-
2.Click on the form title to open it in the pdfFiller workspace, allowing for interactive editing.
-
3.Begin by filling in the requester's information, such as name, title, and contact details in the designated fields.
-
4.Next, provide a detailed description of the proposed changes in the appropriate text box to explain the modifications clearly.
-
5.Ensure you indicate the necessary changes using checkboxes or fillable fields provided within the document.
-
6.After completing all required fields, review your entries carefully for accuracy and completeness.
-
7.Once satisfied, navigate to the signature fields to either receive an electronic signature or print the form for manual signing.
-
8.Finalize the form by clicking the 'Submit' button, following any prompts to save your work.
-
9.You can save it directly to your device, download it as a PDF, or submit it securely through pdfFiller.

Who is eligible to submit the LSI Security Change Request Form?
Eligibility to submit the LSI Security Change Request Form is limited to agency-authorized contacts in Louisiana who are responsible for IT security and firewall management.
What is the deadline for submitting this form?
While specific deadlines can vary, it is advisable to submit the LSI Security Change Request Form as soon as changes are identified to ensure timely processing and implementation.
How should I submit the filled-out form?
After completing the LSI Security Change Request Form, you can submit it electronically through pdfFiller, or download it and send via email or physical mail as required.
What supporting documents are necessary with this form?
Generally, you may need to include authorization from your supervisor or any documentation that supports the requested changes in the security system.
What are common mistakes to avoid when filling out this form?
Common mistakes include forgetting to sign the form, leaving mandatory fields blank, or not providing enough detail in the description of requested changes.
How long will it take to process the LSI Security Change Request Form?
Processing times may vary based on the complexity of the changes requested and the current workload of the OTM staff, but you should generally expect a response within 10-15 business days.
What happens if my request is denied?
If your request is denied, you will typically receive feedback highlighting the reasons for the denial, and you can submit a revised request addressing those issues.
Related Catalogs
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.