What is pdffiller Form?
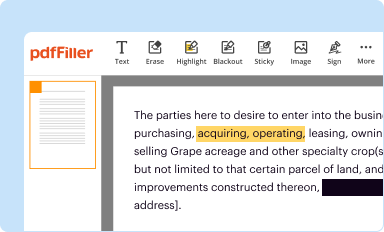
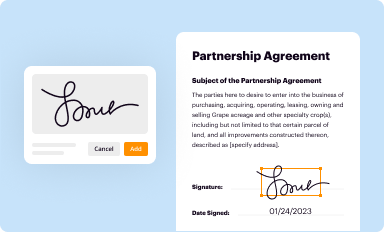
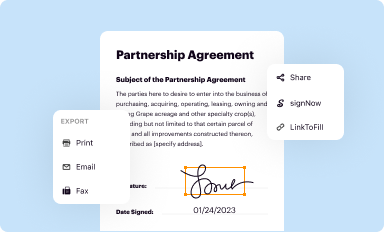
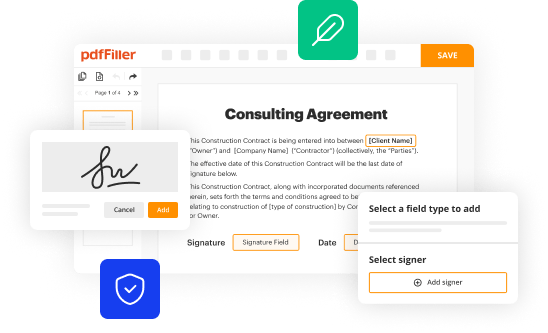
The pdffiller is a document that has to be completed and signed for certain needs. Next, it is provided to the exact addressee to provide certain details of any kinds. The completion and signing is able manually or with an appropriate tool like PDFfiller. These services help to complete any PDF or Word file without printing them out. It also lets you edit its appearance according to your needs and put an official legal digital signature. Upon finishing, you send the pdffiller to the recipient or several of them by email or fax. PDFfiller provides a feature and options that make your blank printable. It includes a number of settings when printing out. No matter, how you'll distribute a form after filling it out - in hard copy or electronically - it will always look neat and clear. To not to create a new editable template from the beginning over and over, make the original form as a template. Later, you will have a rewritable sample.
Template pdffiller instructions
Before to fill out pdffiller Word form, make sure that you prepared enough of necessary information. That's a mandatory part, because typos may trigger unpleasant consequences from re-submission of the whole entire word template and finishing with missing deadlines and even penalties. You should be pretty observative when writing down figures. At first glimpse, it might seem to be uncomplicated. Nevertheless, you can easily make a mistake. Some use some sort of a lifehack saving everything in another file or a record book and then attach it into document's template. In either case, try to make all efforts and present accurate and correct data with your pdffiller word form, and doublecheck it during the process of filling out all necessary fields. If it appears that some mistakes still persist, you can easily make amends when you use PDFfiller application and avoid missing deadlines.
pdffiller word template: frequently asked questions
1. Is it legal to file forms electronically?
According to ESIGN Act 2000, Word forms filled out and authorized by using an e-sign solution are considered legally binding, equally to their physical analogs. As a result you are free to rightfully fill and submit pdffiller word form to the individual or organization needed using digital solution that meets all requirements depending on its legal purposes, like PDFfiller.
2. Is it risk-free to fill in sensitive information online?
Of course, it is totally risk-free if you use reliable app for your work-flow for these purposes. As an example, PDFfiller offers the benefits like:
- All data is stored in the cloud that is facilitated with multi-layer file encryption. Every document is secured from rewriting or copying its content this way. It is user only who has got access to personal files.
- Each and every word file signed has its own unique ID, so it can’t be faked.
- You can set additional security like user authentication via picture or password. There is an way to protect the entire folder with encryption. Place your pdffiller fillable template and set a password.
3. Can I upload required data to the fillable form from another file?
Yes, but you need a specific feature to do that. In PDFfiller, it is called Fill in Bulk. Using this feature, you can actually take data from the Excel sheet and place it into the generated document.