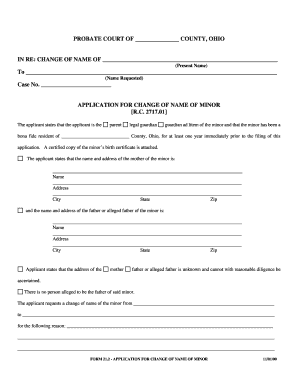
Get the free Vulnerability Summary for the Week of June 15, 2015
Show details
Vulnerability Summary for the Week of June 15, 2015,
Please Note:
The vulnerabilities are categorized by their level of severity which is either High, Medium or Low. The CVE identity number is the
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign vulnerability summary for form
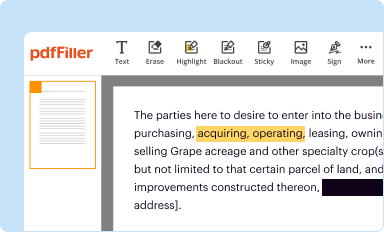
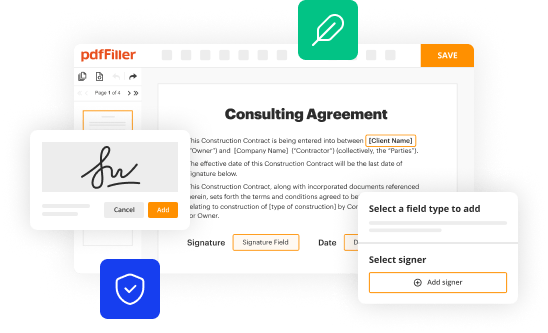
Edit your vulnerability summary for form form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
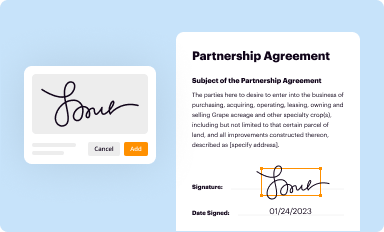
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
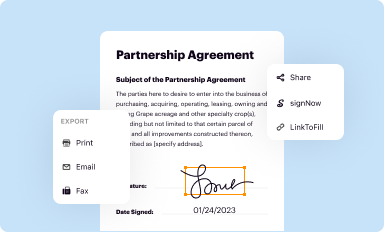
Share your form instantly
Email, fax, or share your vulnerability summary for form form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing vulnerability summary for form online
In order to make advantage of the professional PDF editor, follow these steps below:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit vulnerability summary for form. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
pdfFiller makes working with documents easier than you could ever imagine. Create an account to find out for yourself how it works!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out vulnerability summary for form
How to fill out vulnerability summary for form
01
To fill out a vulnerability summary for a form, follow these steps:
02
Start by identifying the form or application for which you are creating the vulnerability summary.
03
Gather all the necessary information about the form, such as its purpose, functionality, and potential vulnerabilities.
04
Begin by describing the form's overall structure and design. Include information about the different fields, buttons, and interaction methods.
05
Identify all possible vulnerabilities that may exist in the form. This can include things like input validation issues, cross-site scripting (XSS) vulnerabilities, SQL injection risks, or any other security weaknesses.
06
For each vulnerability, provide a detailed explanation of the issue, including the potential impact it can have and any necessary technical details.
07
Clearly specify the steps required to reproduce each vulnerability. This should include the specific inputs or actions needed to trigger the security flaw.
08
Prioritize the vulnerabilities based on their severity or potential impact. This can help stakeholders understand which issues should be addressed first.
09
Provide recommendations or suggestions for remediation or mitigation of each vulnerability. These can include code fixes, configuration changes, or security best practices.
10
Review the vulnerability summary for accuracy and clarity. Ensure that it is comprehensive and easy to understand for both technical and non-technical audiences.
11
If necessary, share the vulnerability summary with relevant stakeholders, such as developers, security analysts, or management, for further review and action.
12
Update the vulnerability summary as needed, especially if new vulnerabilities are discovered or changes are made to the form.
Who needs vulnerability summary for form?
01
Anyone involved in the development, testing, or maintenance of the form or application may need a vulnerability summary. This can include:
02
- Developers: They can use the vulnerability summary to understand and address any security weaknesses in the form's code.
03
- Security analysts: They can leverage the vulnerability summary to identify potential risks and prioritize remediation efforts.
04
- Quality assurance (QA) testers: The vulnerability summary can guide their testing approach, helping them identify and validate vulnerabilities.
05
- Project managers: They can use the vulnerability summary to assess the overall security posture of the form or application and allocate resources accordingly.
06
- Compliance officers: The vulnerability summary can help ensure that the form meets the required security standards and regulations.
07
- IT auditors: They can review the vulnerability summary to assess the effectiveness of the form's security controls.
08
Overall, anyone responsible for the security and integrity of the form or application can benefit from having a vulnerability summary.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I manage my vulnerability summary for form directly from Gmail?
It's easy to use pdfFiller's Gmail add-on to make and edit your vulnerability summary for form and any other documents you get right in your email. You can also eSign them. Take a look at the Google Workspace Marketplace and get pdfFiller for Gmail. Get rid of the time-consuming steps and easily manage your documents and eSignatures with the help of an app.
How do I edit vulnerability summary for form in Chrome?
Get and add pdfFiller Google Chrome Extension to your browser to edit, fill out and eSign your vulnerability summary for form, which you can open in the editor directly from a Google search page in just one click. Execute your fillable documents from any internet-connected device without leaving Chrome.
Can I edit vulnerability summary for form on an iOS device?
No, you can't. With the pdfFiller app for iOS, you can edit, share, and sign vulnerability summary for form right away. At the Apple Store, you can buy and install it in a matter of seconds. The app is free, but you will need to set up an account if you want to buy a subscription or start a free trial.
What is vulnerability summary for form?
The vulnerability summary form is a document that outlines the potential vulnerabilities and weaknesses in a system or process.
Who is required to file vulnerability summary for form?
Any organization or individual who is responsible for the security of a system or process may be required to file a vulnerability summary form.
How to fill out vulnerability summary for form?
The vulnerability summary form typically requires information about the vulnerabilities identified, the potential impact of those vulnerabilities, and any mitigation strategies that have been implemented or are planned.
What is the purpose of vulnerability summary for form?
The purpose of the vulnerability summary form is to help organizations identify and address potential security risks in their systems or processes.
What information must be reported on vulnerability summary for form?
Information that must be reported on the vulnerability summary form includes details about the vulnerabilities identified, their impact, and any steps taken to address them.
Fill out your vulnerability summary for form online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Vulnerability Summary For Form is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.