Get the free SECURITY CHECK LIST
Show details
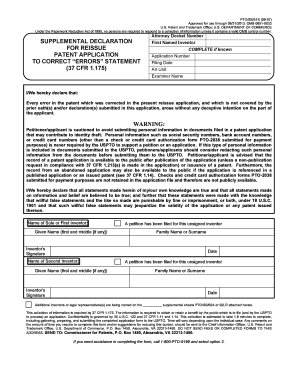
SECURITY CHECK LIST DRIVERS NAME (please print): VISITOR PASS: RENUMBER×PHOTO COPY OF BILL OF LADING: YESNOCARRIER NAME: TRUCK #:TRAILER #:TIME OF ENTRY:TIME OF DEPARTURE:ITEMS NOTED OUT OF THE ORDINARY
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign security check list

Edit your security check list form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your security check list form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit security check list online
Use the instructions below to start using our professional PDF editor:
1
Log in to your account. Click on Start Free Trial and sign up a profile if you don't have one yet.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit security check list. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out security check list

How to fill out security check list
01
To fill out a security check list, follow these steps:
02
Begin by gathering all necessary information such as the name of the person or entity being checked, any identification numbers, and relevant contact details.
03
Review the checklist to understand the specific requirements and items to be checked.
04
Start by going through each item on the checklist one by one and provide the necessary information or select the appropriate response.
05
If any item on the checklist requires supporting documentation or evidence, ensure that it is attached or provided as required.
06
Double-check each entry and ensure that all information provided is accurate and complete.
07
Once you have filled out all the necessary items on the checklist, review it again to make sure nothing has been missed.
08
Sign and date the checklist to confirm its completion.
09
Submit the filled-out checklist to the designated person or department as instructed.
10
Remember to follow any additional instructions or guidelines provided in relation to the security check list.
11
If you encounter any difficulties or have questions while filling out the checklist, seek assistance from the appropriate authorities or personnel responsible for the checklist.
Who needs security check list?
01
Various individuals and entities may require a security check list, including:
02
- Employers or human resources departments conducting background checks on potential employees.
03
- Organizations verifying the security and trustworthiness of their contractors or partners before entering into agreements.
04
- Government agencies ensuring the safety and security of their personnel, facilities, or information.
05
- Individuals applying for security clearance or specific permits requiring a thorough evaluation.
06
- Event organizers implementing security measures to protect attendees and participants.
07
- Any entity or individual concerned about maintaining security and mitigating risks in their operations or environments.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I complete security check list online?
With pdfFiller, you may easily complete and sign security check list online. It lets you modify original PDF material, highlight, blackout, erase, and write text anywhere on a page, legally eSign your document, and do a lot more. Create a free account to handle professional papers online.
Can I create an electronic signature for the security check list in Chrome?
You certainly can. You get not just a feature-rich PDF editor and fillable form builder with pdfFiller, but also a robust e-signature solution that you can add right to your Chrome browser. You may use our addon to produce a legally enforceable eSignature by typing, sketching, or photographing your signature with your webcam. Choose your preferred method and eSign your security check list in minutes.
How do I edit security check list on an iOS device?
Yes, you can. With the pdfFiller mobile app, you can instantly edit, share, and sign security check list on your iOS device. Get it at the Apple Store and install it in seconds. The application is free, but you will have to create an account to purchase a subscription or activate a free trial.
What is security check list?
The security check list is a list of items or procedures that need to be completed in order to ensure the security and safety of a certain area or event.
Who is required to file security check list?
Security personnel or event organizers are usually required to file a security check list to ensure all security measures are in place.
How to fill out security check list?
The security check list can be filled out by providing information about the security measures in place, such as security personnel, access control, surveillance systems, emergency procedures, etc.
What is the purpose of security check list?
The purpose of the security check list is to ensure that all necessary security measures are in place and to help identify any potential security risks.
What information must be reported on security check list?
Information such as security personnel details, access control procedures, surveillance system details, emergency contact information, etc. must be reported on the security check list.
Fill out your security check list online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Security Check List is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.