
Get the free Access Audit Checklist
Show details
Access Audit Checklist
Date
Address
Yes
1. Type of building, e.g. shop, bank, restaurant, office etc.2. Is it a single or 2storey building3. Is the building listed4. Is the building in a conservation
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign access audit checklist
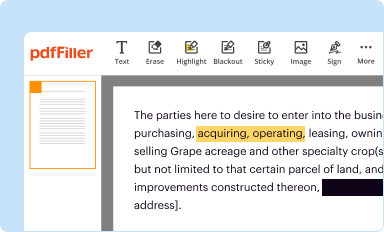
Edit your access audit checklist form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
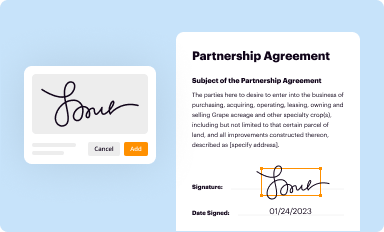
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
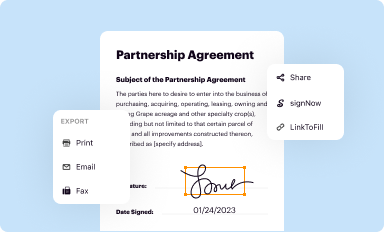
Share your form instantly
Email, fax, or share your access audit checklist form via URL. You can also download, print, or export forms to your preferred cloud storage service.
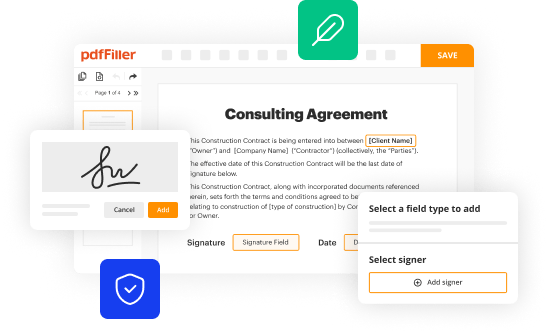
Editing access audit checklist online
In order to make advantage of the professional PDF editor, follow these steps:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit access audit checklist. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out access audit checklist
How to fill out access audit checklist
01
To fill out the access audit checklist, follow these steps:
02
Begin by reviewing the checklist and familiarizing yourself with the required information.
03
Collect all necessary documentation and records related to access control in the audited area.
04
Start with the first section of the checklist and carefully fill in the requested details.
05
Provide accurate information about the existing access control systems, such as the type of technology used, access points, and user roles.
06
Evaluate the effectiveness of the current access control measures and document any identified weaknesses or areas for improvement.
07
Proceed to the next section and repeat the process until you have completed all the sections of the checklist.
08
Double-check all entered information for accuracy and completeness.
09
Once finished, review the completed checklist to ensure its thoroughness and clarity.
10
Submit the checklist to the designated authority or keep it for future reference, as required.
Who needs access audit checklist?
01
Access audit checklists are needed by organizations and individuals responsible for assessing and ensuring the security and efficiency of access control systems.
02
This can include security managers, system administrators, auditors, or any personnel concerned with maintaining access control measures and compliance.
03
Additionally, companies or businesses that operate in regulated industries, such as healthcare, finance, or government sectors, may have specific requirements for regular access auditing, making the checklist essential for their compliance efforts.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Can I create an electronic signature for the access audit checklist in Chrome?
Yes. By adding the solution to your Chrome browser, you may use pdfFiller to eSign documents while also enjoying all of the PDF editor's capabilities in one spot. Create a legally enforceable eSignature by sketching, typing, or uploading a photo of your handwritten signature using the extension. Whatever option you select, you'll be able to eSign your access audit checklist in seconds.
How do I edit access audit checklist on an iOS device?
Yes, you can. With the pdfFiller mobile app, you can instantly edit, share, and sign access audit checklist on your iOS device. Get it at the Apple Store and install it in seconds. The application is free, but you will have to create an account to purchase a subscription or activate a free trial.
How do I complete access audit checklist on an Android device?
On Android, use the pdfFiller mobile app to finish your access audit checklist. Adding, editing, deleting text, signing, annotating, and more are all available with the app. All you need is a smartphone and internet.
What is access audit checklist?
The access audit checklist is a tool used to assess and evaluate the accessibility of a facility or environment for individuals with disabilities.
Who is required to file access audit checklist?
Business owners, property managers, or organizations responsible for maintaining and ensuring accessibility of a facility are required to file the access audit checklist.
How to fill out access audit checklist?
The access audit checklist can be filled out by conducting on-site inspections, evaluations, and assessments of a facility's accessibility features and barriers.
What is the purpose of access audit checklist?
The purpose of the access audit checklist is to identify areas of noncompliance with accessibility standards, regulations, and laws, and to develop a plan for addressing and improving accessibility.
What information must be reported on access audit checklist?
The access audit checklist must include details on accessibility features, barriers, compliance with regulations, and recommended improvements.
Fill out your access audit checklist online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Access Audit Checklist is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.

















