
Get the free Detecting Attacks on Web Applications from Log - sans
Show details
Interested in learning more about security?SANS Institute InfoSec Reading Room This paper is from the SANS Institute Reading Room site. Reposting is not permitted without express written permission.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign detecting attacks on web
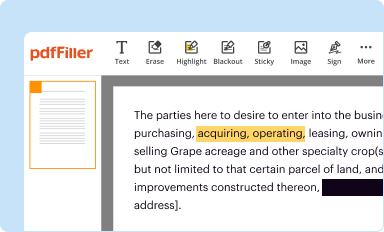
Edit your detecting attacks on web form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
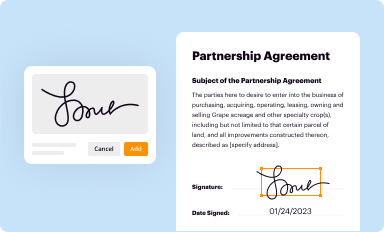
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
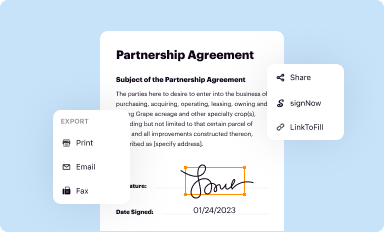
Share your form instantly
Email, fax, or share your detecting attacks on web form via URL. You can also download, print, or export forms to your preferred cloud storage service.
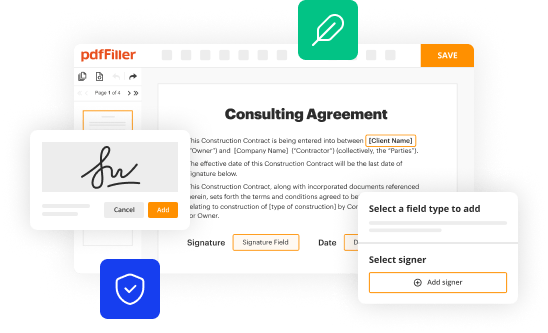
How to edit detecting attacks on web online
Use the instructions below to start using our professional PDF editor:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit detecting attacks on web. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Save your file. Select it in the list of your records. Then, move the cursor to the right toolbar and choose one of the available exporting methods: save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud.
It's easier to work with documents with pdfFiller than you could have ever thought. You can sign up for an account to see for yourself.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out detecting attacks on web
How to Fill Out Detecting Attacks on Web:
01
Begin by gathering information about the web application or website that you want to protect. Document its purpose, functionalities, and the potential vulnerabilities that may exist.
02
Conduct a thorough risk assessment to identify the possible attack vectors that hackers may exploit. This step involves examining the application's architecture, coding practices, and any potential weaknesses in its security infrastructure.
03
Determine the appropriate security measures and tools that should be implemented to detect attacks on the web. This may include setting up firewalls, intrusion detection systems, log monitoring, and security incident response protocols.
04
Define clear detection rules and alerts based on the identified attack vectors. This involves creating specific criteria or patterns that trigger an alert when malicious activities are detected. The rules can be based on known attack patterns or abnormal behavior.
05
Configure and deploy the necessary security tools and systems according to your detection rules and requirements. Ensure that they are properly integrated into your web application or website, and regularly update them with the latest security patches and threat intelligence.
06
Train your team on how to effectively monitor and respond to alerts generated by the security tools. This includes establishing a process for investigating and triaging alerts, as well as coordinating with relevant stakeholders to mitigate the impact of detected attacks.
Who Needs Detecting Attacks on Web:
01
Businesses and organizations with an online presence, such as e-commerce websites, online banking platforms, and educational institutions, need to detect attacks on the web. These entities are attractive targets for hackers due to the potential financial gains or valuable data they possess.
02
Web developers and administrators responsible for maintaining the security of a website or web application should be adept at detecting attacks. They play a crucial role in safeguarding the system from vulnerabilities and ensuring its continuous operation.
03
Security professionals and cybersecurity teams tasked with protecting web-based assets must have a strong understanding of how to detect attacks on the web. Their expertise is essential in preventing and mitigating potential security breaches.
In summary, filling out the process of detecting attacks on the web involves gathering information, conducting risk assessments, implementing security measures, defining detection rules, configuring security tools, and training personnel. Various entities, including businesses, web developers, and security professionals, need to be proficient in detecting attacks to safeguard their web assets.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send detecting attacks on web for eSignature?
To distribute your detecting attacks on web, simply send it to others and receive the eSigned document back instantly. Post or email a PDF that you've notarized online. Doing so requires never leaving your account.
How do I make changes in detecting attacks on web?
With pdfFiller, the editing process is straightforward. Open your detecting attacks on web in the editor, which is highly intuitive and easy to use. There, you’ll be able to blackout, redact, type, and erase text, add images, draw arrows and lines, place sticky notes and text boxes, and much more.
Can I edit detecting attacks on web on an Android device?
Yes, you can. With the pdfFiller mobile app for Android, you can edit, sign, and share detecting attacks on web on your mobile device from any location; only an internet connection is needed. Get the app and start to streamline your document workflow from anywhere.
Fill out your detecting attacks on web online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Detecting Attacks On Web is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















