Get the free Title 25 INTERNAL SECURITY AND PUBLIC SAFETY
Show details
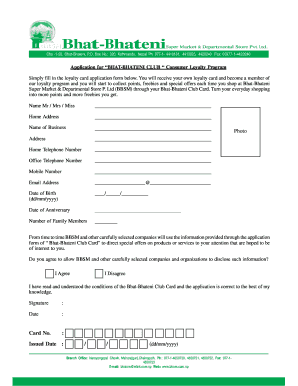
TOWN OF UNIFIL Oversize/OVER WEIGHT PERMIT APPLICATION FORM In Accordance with Section 110 of the Highway Traffic Act (HTA) APPLICANT NAME: CVR #: ADDRESS: PHONE: FAX NUMBER: APPLICANT IS REQUESTING
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign title 25 internal security

Edit your title 25 internal security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your title 25 internal security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit title 25 internal security online
Follow the steps below to benefit from a competent PDF editor:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit title 25 internal security. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out title 25 internal security

How to Fill Out Title 25 Internal Security:
01
Familiarize yourself with the requirements of Title 25 Internal Security. Read through the guidelines and instructions provided to ensure you understand the purpose and objectives of this internal security measure.
02
Obtain the necessary forms and documents related to Title 25 Internal Security. These may include application forms, questionnaires, or checklists. Ensure you have all the required paperwork to complete the process accurately.
03
Review the specific criteria outlined in Title 25 for internal security compliance. Understand the standards, procedures, and regulations that need to be adhered to in order to meet the requirements.
04
Gather all relevant information and data pertaining to your organization's internal security practices. This may include details on security protocols, personnel background checks, access control measures, incident reporting procedures, and any other information that is directly related to internal security.
05
Fill out the required forms and documents accurately and completely. Pay close attention to every field and ensure that all information provided is correct and up to date. Double-check for any errors or omissions before submitting your forms.
06
Attach any supporting documentation that may be necessary to complete the application process. This may include policies, procedures, training records, or any other evidence that demonstrates your organization's commitment to internal security.
07
Once you have completed the forms and attached the supporting documents, submit your application according to the provided instructions. Ensure that you meet any required deadlines and send your application to the designated recipient or authority responsible for processing Title 25 Internal Security.
Who Needs Title 25 Internal Security?
01
Organizations or businesses that handle sensitive or classified information may need to comply with Title 25 Internal Security. This can include government agencies, defense contractors, financial institutions, healthcare facilities, or any other entity that deals with confidential data.
02
Companies that value the security of their internal operations and want to ensure the safety of their employees, clients, and assets can also benefit from implementing Title 25 Internal Security measures. Even if not required by law, prioritizing internal security can help maintain a secure environment and instill trust in stakeholders.
03
Individuals responsible for overseeing and managing internal security within an organization, such as security officers, risk managers, or compliance officers, may also need to be familiar with and adhere to Title 25 regulations. Being knowledgeable about these guidelines can help facilitate the proper implementation and maintenance of internal security protocols.
Remember, compliance with Title 25 Internal Security is important for organizations that handle sensitive information or prioritize their internal security. By understanding and following the guidelines, you can take the necessary steps to ensure that your organization is meeting the required standards and protecting its internal affairs.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
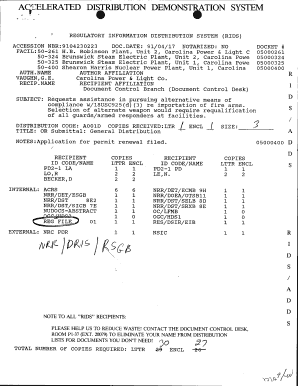
What is title 25 internal security?
Title 25 internal security refers to the regulations and requirements set forth by the federal government to ensure the protection of internal security within organizations.
Who is required to file title 25 internal security?
Certain organizations, particularly those that handle sensitive information or are considered critical infrastructure, are required to file title 25 internal security.
How to fill out title 25 internal security?
Title 25 internal security can be filled out by following the specific guidelines and instructions provided by the federal government. This may include providing information on security measures, risk assessments, and compliance with regulations.
What is the purpose of title 25 internal security?
The purpose of title 25 internal security is to safeguard organizations and critical infrastructure from threats to internal security, such as cyber attacks, espionage, and sabotage.
What information must be reported on title 25 internal security?
Information that may need to be reported on title 25 internal security includes security protocols, risk assessments, incident response plans, and compliance documents.
Where do I find title 25 internal security?
The premium version of pdfFiller gives you access to a huge library of fillable forms (more than 25 million fillable templates). You can download, fill out, print, and sign them all. State-specific title 25 internal security and other forms will be easy to find in the library. Find the template you need and use advanced editing tools to make it your own.
Can I sign the title 25 internal security electronically in Chrome?
You certainly can. You get not just a feature-rich PDF editor and fillable form builder with pdfFiller, but also a robust e-signature solution that you can add right to your Chrome browser. You may use our addon to produce a legally enforceable eSignature by typing, sketching, or photographing your signature with your webcam. Choose your preferred method and eSign your title 25 internal security in minutes.
How do I fill out the title 25 internal security form on my smartphone?
You can easily create and fill out legal forms with the help of the pdfFiller mobile app. Complete and sign title 25 internal security and other documents on your mobile device using the application. Visit pdfFiller’s webpage to learn more about the functionalities of the PDF editor.
Fill out your title 25 internal security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Title 25 Internal Security is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.