Get the free DATE OF SUSPICIOUS ACTIVITY* - sos mt
Show details
Montana Secretary of State
Potential Election Law Violation Report
Fields marked with an asterisk (*) are required fields. LAST NAME×FIRST NAME×ADDRESS×MIDDLE AMENITY×COUNTY×PHONE×MANDATE OF
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign date of suspicious activity
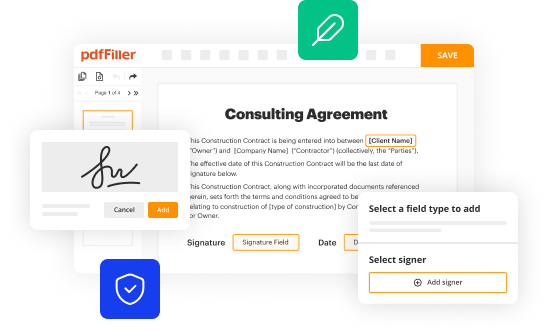
Edit your date of suspicious activity form online
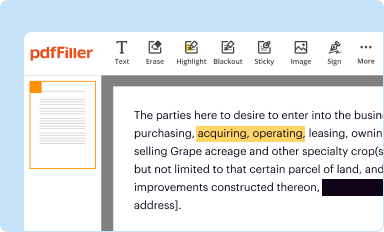
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
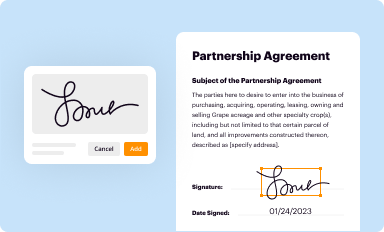
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
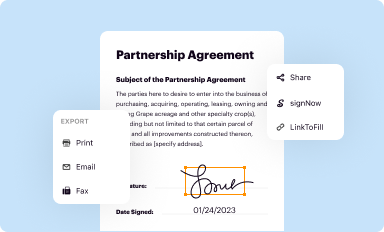
Share your form instantly
Email, fax, or share your date of suspicious activity form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit date of suspicious activity online
In order to make advantage of the professional PDF editor, follow these steps below:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit date of suspicious activity. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
It's easier to work with documents with pdfFiller than you can have ever thought. You can sign up for an account to see for yourself.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out date of suspicious activity
How to fill out date of suspicious activity
01
Start by gathering all the necessary information related to the suspicious activity, such as the date, time, and location.
02
Make sure you have access to any relevant documents or records that can help you accurately fill out the date.
03
Begin by entering the day of the suspicious activity in the appropriate format, such as DD/MM/YYYY.
04
Follow by selecting the month from the available options or entering it manually if required.
05
Lastly, input the year of the suspicious activity, ensuring it is entered correctly.
06
Double-check all the information entered to ensure accuracy and completeness.
07
Save or submit the filled-out date of suspicious activity as per the specific requirements or procedures provided.
Who needs date of suspicious activity?
01
Various entities may require the date of suspicious activity, including but not limited to:
02
- Law enforcement agencies investigating the suspicious activity
03
- Financial institutions or banks conducting fraud or anti-money laundering investigations
04
- Compliance departments of organizations monitoring suspicious activities
05
- Legal authorities or regulatory bodies overseeing compliance and investigations
06
- Internal audit teams assessing potential irregularities
07
- Insurance companies processing claims for suspicious events
08
- Individuals or businesses reporting suspicious activities to the appropriate authorities
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I edit date of suspicious activity from Google Drive?
Simplify your document workflows and create fillable forms right in Google Drive by integrating pdfFiller with Google Docs. The integration will allow you to create, modify, and eSign documents, including date of suspicious activity, without leaving Google Drive. Add pdfFiller’s functionalities to Google Drive and manage your paperwork more efficiently on any internet-connected device.
How do I edit date of suspicious activity in Chrome?
Add pdfFiller Google Chrome Extension to your web browser to start editing date of suspicious activity and other documents directly from a Google search page. The service allows you to make changes in your documents when viewing them in Chrome. Create fillable documents and edit existing PDFs from any internet-connected device with pdfFiller.
How do I fill out date of suspicious activity using my mobile device?
You can easily create and fill out legal forms with the help of the pdfFiller mobile app. Complete and sign date of suspicious activity and other documents on your mobile device using the application. Visit pdfFiller’s webpage to learn more about the functionalities of the PDF editor.
What is date of suspicious activity?
The date of suspicious activity is the specific date on which suspicious activity was observed or detected.
Who is required to file date of suspicious activity?
Financial institutions and certain other businesses are required to file date of suspicious activity reports.
How to fill out date of suspicious activity?
Date of suspicious activity should be filled out by providing the specific date on which suspicious activity occurred.
What is the purpose of date of suspicious activity?
The purpose of providing the date of suspicious activity is to accurately track and report when suspicious activities took place.
What information must be reported on date of suspicious activity?
The date and details of the suspicious activity must be reported on the date of suspicious activity.
Fill out your date of suspicious activity online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Date Of Suspicious Activity is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.