Get the free BI Security Instructions and Forms
Show details
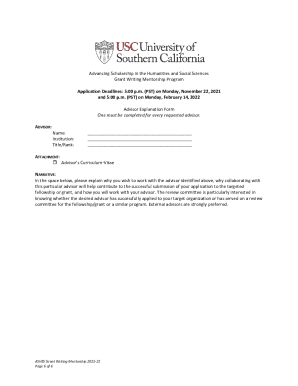
Lexington Supplemental Nursing Attachment 7 BI Security Instructions and Forms Background Investigation Submission Instructions Each contract employee must submit to and pass a background investigation.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign bi security instructions and

Edit your bi security instructions and form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your bi security instructions and form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing bi security instructions and online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit bi security instructions and. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out bi security instructions and

How to fill out bi security instructions and
01
Step 1: Start by reading the bi security instructions carefully.
02
Step 2: Make sure you understand the purpose and importance of bi security.
03
Step 3: Follow the instructions step by step, ensuring compliance with security protocols.
04
Step 4: Pay attention to any specific requirements or guidelines mentioned in the instructions.
05
Step 5: If you have any doubts or questions, seek clarification from the relevant authorities.
06
Step 6: Fill out the bi security instructions accurately and honestly, providing all the requested information.
07
Step 7: Double-check your filled-out form for any errors or omissions before submitting it.
08
Step 8: Submit the completed bi security instructions to the designated person or department.
09
Step 9: Follow up, if necessary, to ensure that the instructions have been received and reviewed.
10
Step 10: Keep a copy of the filled-out bi security instructions for your records.
Who needs bi security instructions and?
01
Anyone involved in activities or processes that require adherence to bi security measures.
02
Individuals working in sensitive areas, such as defense, intelligence, or cybersecurity.
03
Organizations or institutions handling confidential or classified information.
04
Employees or contractors responsible for the protection of biometric data.
05
Security professionals or consultants working on biometric-related projects.
06
Researchers or developers involved in biometric technology.
07
Government agencies or regulatory bodies overseeing biometric systems.
08
Law enforcement personnel utilizing biometric identification tools.
09
Companies implementing biometric access control systems.
10
Individuals interested in understanding and implementing best practices for biometric security.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I modify my bi security instructions and in Gmail?
In your inbox, you may use pdfFiller's add-on for Gmail to generate, modify, fill out, and eSign your bi security instructions and and any other papers you receive, all without leaving the program. Install pdfFiller for Gmail from the Google Workspace Marketplace by visiting this link. Take away the need for time-consuming procedures and handle your papers and eSignatures with ease.
How do I fill out the bi security instructions and form on my smartphone?
The pdfFiller mobile app makes it simple to design and fill out legal paperwork. Complete and sign bi security instructions and and other papers using the app. Visit pdfFiller's website to learn more about the PDF editor's features.
Can I edit bi security instructions and on an iOS device?
You certainly can. You can quickly edit, distribute, and sign bi security instructions and on your iOS device with the pdfFiller mobile app. Purchase it from the Apple Store and install it in seconds. The program is free, but in order to purchase a subscription or activate a free trial, you must first establish an account.
What is bi security instructions and?
Bi security instructions is a set of guidelines and protocols that help ensure the security of sensitive information and resources within a business or organization.
Who is required to file bi security instructions and?
All employees and individuals who have access to confidential or classified information are required to adhere to bi security instructions.
How to fill out bi security instructions and?
Bi Security instructions can be filled out by following the guidelines and procedures provided by the organization's security team. It may include steps such as setting up secure passwords, encrypting data, and restricting access to sensitive information.
What is the purpose of bi security instructions and?
The purpose of bi security instructions is to protect sensitive information from unauthorized access, leaks, or breaches, ensuring the confidentiality, integrity, and availability of the data.
What information must be reported on bi security instructions and?
The information that must be reported on bi security instructions may include personal identification details, access levels, security measures followed, and any incidents or breaches encountered.
Fill out your bi security instructions and online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Bi Security Instructions And is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.