Get the free CWE-327 - Common Weakness Enumeration - The MITRE ...
Show details
Autumn 2018In this issue
Annual Meeting and Pension
Surgery 2018
Fund accounts summary 2017/2018
Changes to The Earliest Payment of
Deferred Benefits' newsletter for deferred members of the Local
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign cwe-327 - common weakness

Edit your cwe-327 - common weakness form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your cwe-327 - common weakness form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit cwe-327 - common weakness online
Follow the steps down below to benefit from the PDF editor's expertise:
1
Log into your account. If you don't have a profile yet, click Start Free Trial and sign up for one.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit cwe-327 - common weakness. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
pdfFiller makes working with documents easier than you could ever imagine. Create an account to find out for yourself how it works!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out cwe-327 - common weakness

How to fill out cwe-327 - common weakness
01
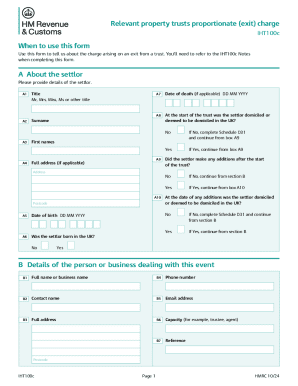
To fill out CWE-327 - common weakness, you need to follow these steps:
02
Start by gathering all relevant information about the common weakness.
03
Understand the specific details and characteristics of the common weakness.
04
Identify any existing solutions or countermeasures for the weakness.
05
Document any known impacts or consequences of the weakness.
06
Determine any dependencies or relationships with other weaknesses or vulnerabilities.
07
Provide clear and concise explanations of the weakness using appropriate technical language.
08
Include any examples or code snippets that illustrate the weakness.
09
Verify the accuracy and completeness of the information provided.
10
Submit the filled-out CWE-327 - common weakness form to the relevant authority or organization.
Who needs cwe-327 - common weakness?
01
Various entities and individuals may need to understand or utilize CWE-327 - common weakness. This includes:
02
- Software developers and engineers who want to identify and address weaknesses in their code.
03
- Security professionals and researchers who study vulnerabilities and weaknesses in software systems.
04
- Organizations and companies that want to enhance their software development practices by addressing common weaknesses.
05
- Regulators and compliance auditors who assess the security of software systems and require adherence to best practices.
06
- Educators and trainers who teach secure coding practices and want to emphasize the importance of common weaknesses.
07
- Developers, researchers, or organizations involved in vulnerability analysis, threat modeling, or security testing.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I execute cwe-327 - common weakness online?
Filling out and eSigning cwe-327 - common weakness is now simple. The solution allows you to change and reorganize PDF text, add fillable fields, and eSign the document. Start a free trial of pdfFiller, the best document editing solution.
Can I create an electronic signature for signing my cwe-327 - common weakness in Gmail?
Create your eSignature using pdfFiller and then eSign your cwe-327 - common weakness immediately from your email with pdfFiller's Gmail add-on. To keep your signatures and signed papers, you must create an account.
Can I edit cwe-327 - common weakness on an Android device?
You can. With the pdfFiller Android app, you can edit, sign, and distribute cwe-327 - common weakness from anywhere with an internet connection. Take use of the app's mobile capabilities.
What is cwe-327 - common weakness?
CWE-327 is a category in the Common Weakness Enumeration (CWE) list that identifies weaknesses related to the use of an incorrect API.
Who is required to file cwe-327 - common weakness?
Organizations or individuals who discover or are aware of vulnerabilities related to CWE-327 are required to file a report.
How to fill out cwe-327 - common weakness?
CWE-327 reports should include detailed information about the vulnerability, its impact, steps to reproduce, and any available fixes or workarounds.
What is the purpose of cwe-327 - common weakness?
The purpose of CWE-327 is to help organizations understand and address vulnerabilities related to the use of an incorrect API.
What information must be reported on cwe-327 - common weakness?
Information such as description of vulnerability, impact of vulnerability, steps to reproduce, and any available fixes or workarounds must be reported.
Fill out your cwe-327 - common weakness online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Cwe-327 - Common Weakness is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.