Get the free Incident Response Computer Forensics Third Edition Ebook. Incident Response Computer...
Show details
Get Free Register Download or Read Online Files File Name : Incident Response Computer Forensics Third Edition E-Book INCIDENT RESPONSE COMPUTER FORENSICS THIRD EDITION BOOK Download : Incident Response
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign incident response computer forensics
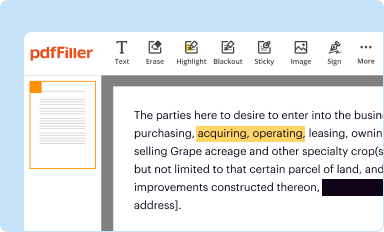
Edit your incident response computer forensics form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
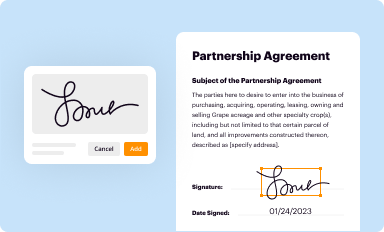
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
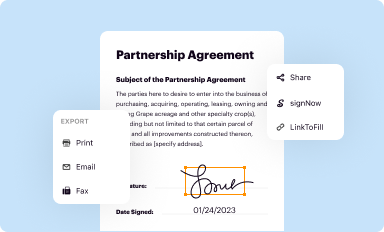
Share your form instantly
Email, fax, or share your incident response computer forensics form via URL. You can also download, print, or export forms to your preferred cloud storage service.
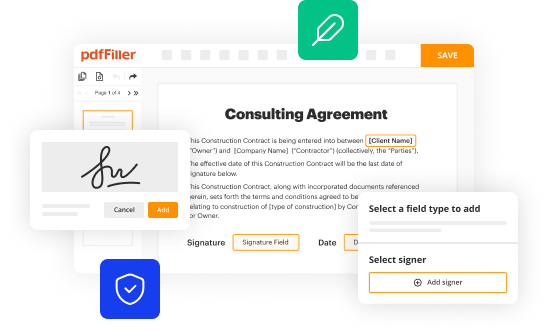
Editing incident response computer forensics online
To use our professional PDF editor, follow these steps:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit incident response computer forensics. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Save your file. Select it in the list of your records. Then, move the cursor to the right toolbar and choose one of the available exporting methods: save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud.
It's easier to work with documents with pdfFiller than you could have believed. Sign up for a free account to view.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out incident response computer forensics
How to fill out incident response computer forensics
01
To fill out an incident response computer forensics, follow these steps:
02
Start by documenting the incident details, including the date, time, and location of the incident.
03
Identify the affected systems and gather relevant information such as IP addresses, log files, and error messages.
04
Preserve the evidence by creating a forensic image of the affected systems. This ensures that the original data remains intact and can be analyzed later.
05
Conduct a thorough analysis of the forensic image, looking for any signs of unauthorized access, malware presence, or other malicious activities.
06
Document the findings and any actions taken during the investigation.
07
Prepare a detailed report that includes the incident timeline, analysis results, and recommended actions to prevent future incidents.
08
Share the report with relevant stakeholders, such as IT teams, management, and legal authorities, if necessary.
09
Implement the recommended actions and monitor the systems for any further incidents.
10
Remember to follow best practices and adhere to legal and regulatory requirements while conducting incident response computer forensics.
Who needs incident response computer forensics?
01
Any organization or individual that wants to effectively respond to and investigate computer security incidents can benefit from incident response computer forensics.
02
Some specific entities that often need incident response computer forensics include:
03
- Enterprises and businesses of all sizes to protect their sensitive data and intellectual property.
04
- Government agencies and law enforcement organizations to investigate cybercrimes and gather evidence for legal proceedings.
05
- Cybersecurity and IT consulting firms that offer incident response services to their clients.
06
- Non-profit organizations and educational institutions to ensure the security of their systems and protect sensitive information.
07
In summary, incident response computer forensics is valuable for anyone who wants to identify, analyze, and respond effectively to computer security incidents.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I edit incident response computer forensics from Google Drive?
People who need to keep track of documents and fill out forms quickly can connect PDF Filler to their Google Docs account. This means that they can make, edit, and sign documents right from their Google Drive. Make your incident response computer forensics into a fillable form that you can manage and sign from any internet-connected device with this add-on.
How do I make changes in incident response computer forensics?
pdfFiller allows you to edit not only the content of your files, but also the quantity and sequence of the pages. Upload your incident response computer forensics to the editor and make adjustments in a matter of seconds. Text in PDFs may be blacked out, typed in, and erased using the editor. You may also include photos, sticky notes, and text boxes, among other things.
How do I edit incident response computer forensics in Chrome?
Add pdfFiller Google Chrome Extension to your web browser to start editing incident response computer forensics and other documents directly from a Google search page. The service allows you to make changes in your documents when viewing them in Chrome. Create fillable documents and edit existing PDFs from any internet-connected device with pdfFiller.
What is incident response computer forensics?
Incident response computer forensics is a process of identifying, preserving, analyzing, and presenting digital evidence in response to a cybersecurity incident.
Who is required to file incident response computer forensics?
Organizations or individuals that experience a cybersecurity incident are required to file incident response computer forensics.
How to fill out incident response computer forensics?
To fill out incident response computer forensics, one must document the details of the cybersecurity incident, including the timeline of events, evidence collected, and actions taken to mitigate the incident.
What is the purpose of incident response computer forensics?
The purpose of incident response computer forensics is to investigate and analyze cybersecurity incidents, identify the root cause of the incident, and prevent future incidents.
What information must be reported on incident response computer forensics?
Incident response computer forensics must include details such as the nature of the incident, impact on the organization, evidence collected, and remediation steps taken.
Fill out your incident response computer forensics online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Incident Response Computer Forensics is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.