Get the free Data Security Checklist to Increase Victim Safety & Privacy
Show details
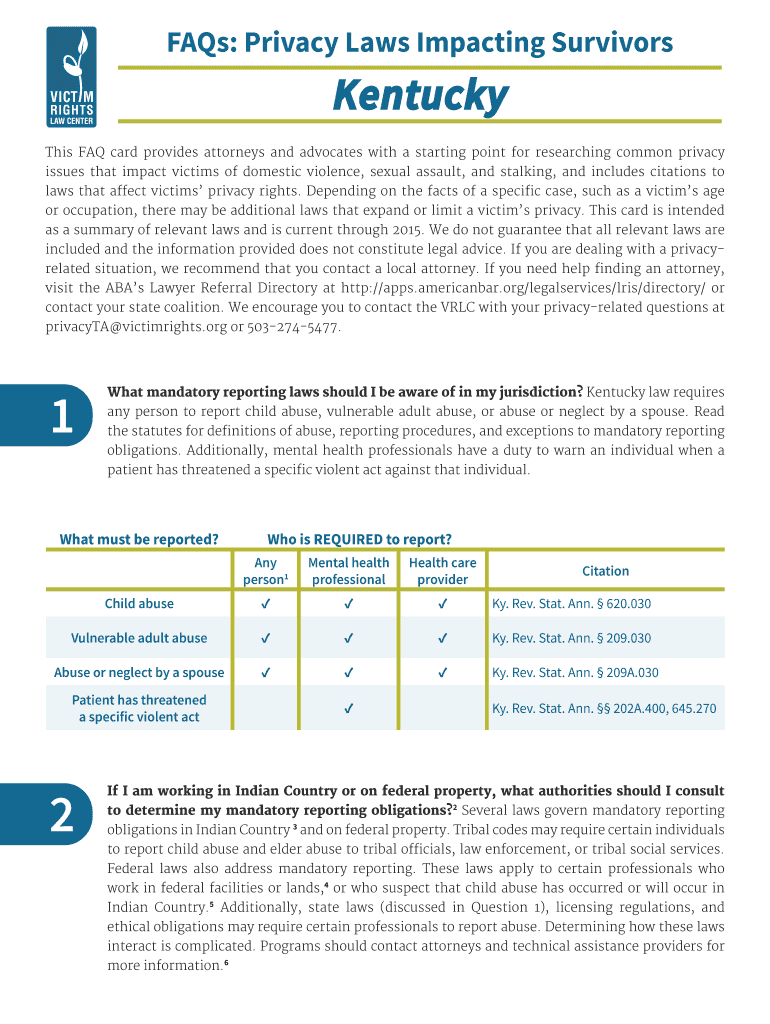
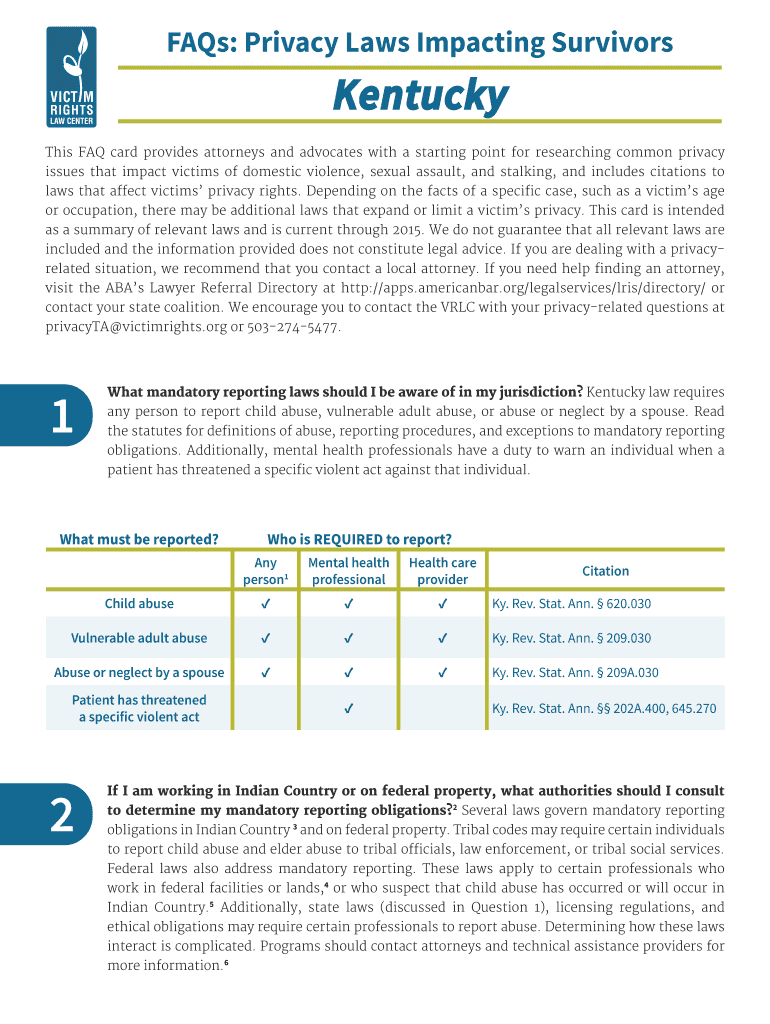
FAQs: Privacy Laws Impacting Survivors Kentucky
This FAQ card provides attorneys and advocates with a starting point for researching common privacy
issues that impact victims of domestic violence,
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign data security checklist to

Edit your data security checklist to form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your data security checklist to form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit data security checklist to online
Follow the steps down below to benefit from the PDF editor's expertise:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit data security checklist to. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
With pdfFiller, it's always easy to work with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out data security checklist to

How to fill out data security checklist to
01
Start by reviewing the data security checklist thoroughly.
02
Make sure you understand each item on the checklist and its importance.
03
Gather all the necessary information and documentation required to fill out the checklist.
04
Begin filling out the checklist systematically, addressing each item one by one.
05
Provide accurate and up-to-date information for each item.
06
If any item is not applicable to your organization, clearly indicate it on the checklist.
07
If you are unsure about any item, seek guidance from a data security expert.
08
Double-check your entries and ensure the checklist is completed in its entirety.
09
Sign and date the checklist to confirm its completeness and accuracy.
10
Keep a copy of the filled-out checklist for future reference and audit purposes.
Who needs data security checklist to?
01
Anyone handling sensitive data, such as businesses, organizations, and individuals, needs a data security checklist.
02
It is particularly important for companies that deal with customer information, financial data, or any confidential information.
03
Government agencies, healthcare providers, and educational institutions also require a data security checklist to ensure compliance with regulations and protect sensitive information.
04
Ultimately, anyone concerned about safeguarding data and maintaining a secure environment should prioritize using a data security checklist.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send data security checklist to for eSignature?
Once your data security checklist to is complete, you can securely share it with recipients and gather eSignatures with pdfFiller in just a few clicks. You may transmit a PDF by email, text message, fax, USPS mail, or online notarization directly from your account. Make an account right now and give it a go.
How do I edit data security checklist to in Chrome?
Adding the pdfFiller Google Chrome Extension to your web browser will allow you to start editing data security checklist to and other documents right away when you search for them on a Google page. People who use Chrome can use the service to make changes to their files while they are on the Chrome browser. pdfFiller lets you make fillable documents and make changes to existing PDFs from any internet-connected device.
Can I edit data security checklist to on an iOS device?
No, you can't. With the pdfFiller app for iOS, you can edit, share, and sign data security checklist to right away. At the Apple Store, you can buy and install it in a matter of seconds. The app is free, but you will need to set up an account if you want to buy a subscription or start a free trial.
What is data security checklist to?
The data security checklist is a list of security measures and procedures that help ensure the protection of sensitive data.
Who is required to file data security checklist to?
Certain companies and organizations, especially those handling sensitive data, are required to file a data security checklist.
How to fill out data security checklist to?
The data security checklist can be filled out by detailing the security measures in place, including encryption protocols, access controls, and employee training.
What is the purpose of data security checklist to?
The purpose of the data security checklist is to assess and improve the security measures in place to protect sensitive data from breaches or unauthorized access.
What information must be reported on data security checklist to?
The data security checklist must include details on encryption methods, access controls, employee training, incident response procedures, and data backup systems.
Fill out your data security checklist to online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Data Security Checklist To is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.