Get the free Banner Security System Guidelines - Elizabeth City State... - cfweb cc ysu
Show details
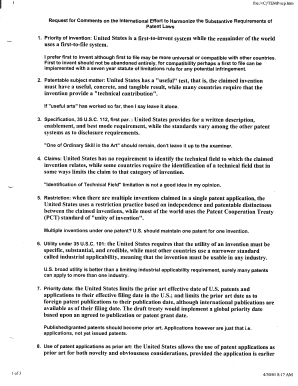
Welcome to Sugar SET Banner Selective Admissions.sungardsct.introductions Name Organization Title/function Job responsibilities SET Banner experience Expectations.sungardsct.com2Course Goals The goal
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign banner security system guidelines

Edit your banner security system guidelines form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your banner security system guidelines form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit banner security system guidelines online
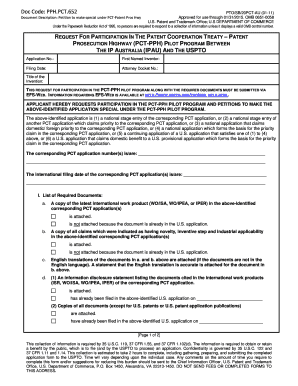
To use our professional PDF editor, follow these steps:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit banner security system guidelines. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out banner security system guidelines

How to fill out banner security system guidelines:
01
Familiarize yourself with the purpose of the guidelines: Before filling out the banner security system guidelines, it is important to understand why they exist and what they aim to achieve. This will give you a clear idea of what information needs to be included and what security measures are expected to be implemented.
02
Start with the basics: Begin by providing essential information such as the name of the organization or company, the date the guidelines are being filled out, and any other relevant identification details. This will help ensure that the guidelines are properly associated with the right entity and are up to date.
03
Define the scope and objectives: Clearly state the scope of the banner security system guidelines, outlining the areas or systems that they cover. Additionally, identify the specific objectives or goals that these guidelines aim to accomplish, such as ensuring the confidentiality, integrity, and availability of information.
04
Outline the roles and responsibilities: Identify the key stakeholders involved in the security of the banner system. This may include system administrators, network administrators, security personnel, and any other personnel responsible for managing and maintaining the security of the banner system. Clearly define the roles and responsibilities of each party to ensure accountability and effective coordination.
05
Assess potential threats and risks: List the potential threats and risks that the banner security system may face. This can include unauthorized access, data breaches, malware attacks, physical theft or damage, and other security vulnerabilities. Analyze the likelihood and potential impact of each threat to determine the appropriate security measures to be implemented.
06
Define security controls: Specify the security controls and measures that need to be implemented to mitigate the identified threats and risks. This can include access control mechanisms, encryption protocols, intrusion detection systems, firewalls, physical security measures, and employee training programs. Clearly outline the requirements and specifications for each security control to ensure consistency and effectiveness.
07
Establish incident response procedures: Develop a comprehensive incident response plan that outlines the steps to be taken in the event of a security incident or breach. This should include procedures for detecting, containing, mitigating, and recovering from security incidents. Assign responsibilities to personnel involved in the incident response process and provide contact information for reporting incidents.
08
Regularly review and update the guidelines: Security threats evolve over time, and new vulnerabilities may emerge. It is important to periodically review and update the banner security system guidelines to ensure that they remain relevant and effective. This may involve conducting regular risk assessments, keeping up with industry best practices, and incorporating feedback from relevant stakeholders.
Who needs banner security system guidelines:
01
Organizations or companies that utilize a banner system for their operations.
02
IT departments or system administrators responsible for managing the security of the banner system.
03
Security personnel involved in monitoring and ensuring the integrity of the banner system.
04
Employees or users who have access to the banner system and need to adhere to security guidelines.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send banner security system guidelines for eSignature?
When your banner security system guidelines is finished, send it to recipients securely and gather eSignatures with pdfFiller. You may email, text, fax, mail, or notarize a PDF straight from your account. Create an account today to test it.
How can I fill out banner security system guidelines on an iOS device?
pdfFiller has an iOS app that lets you fill out documents on your phone. A subscription to the service means you can make an account or log in to one you already have. As soon as the registration process is done, upload your banner security system guidelines. You can now use pdfFiller's more advanced features, like adding fillable fields and eSigning documents, as well as accessing them from any device, no matter where you are in the world.
How do I complete banner security system guidelines on an Android device?
Use the pdfFiller mobile app and complete your banner security system guidelines and other documents on your Android device. The app provides you with all essential document management features, such as editing content, eSigning, annotating, sharing files, etc. You will have access to your documents at any time, as long as there is an internet connection.
What is banner security system guidelines?
Banner security system guidelines outline the policies and procedures for protecting sensitive information within a company's network.
Who is required to file banner security system guidelines?
All companies that handle sensitive information are required to file banner security system guidelines.
How to fill out banner security system guidelines?
Banner security system guidelines can be filled out by following the specific instructions provided by the company or regulatory body.
What is the purpose of banner security system guidelines?
The purpose of banner security system guidelines is to ensure that sensitive information is properly protected from unauthorized access or breaches.
What information must be reported on banner security system guidelines?
Banner security system guidelines typically include information on access control, data encryption, incident response procedures, and employee training.
Fill out your banner security system guidelines online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Banner Security System Guidelines is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.