Get the free Networking Technology Networking Security (Diploma) - forsythtech
Show details
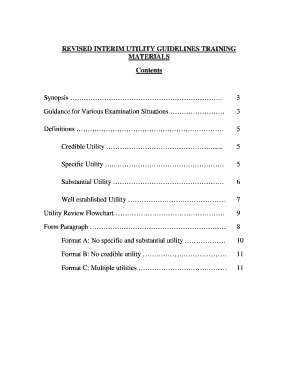
Career and Technical Education Pathway Program of Study College Name Curriculum Code: D25340NSP1 Contact Person: Cheri Silverman Effective Term: Forsyth Technical Community College (834) Curriculum
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign networking technology networking security

Edit your networking technology networking security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your networking technology networking security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing networking technology networking security online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit networking technology networking security. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
Dealing with documents is always simple with pdfFiller.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out networking technology networking security

How to fill out networking technology networking security?
01
Identify the specific networking technology you are using. This could be local area networks (LANs), wide area networks (WANs), or virtual private networks (VPNs), among others.
02
Assess your current network security infrastructure. Determine the existing security measures in place and identify any potential vulnerabilities or weaknesses.
03
Update your network security protocols. Make sure you are using the latest encryption standards and security protocols to protect your network from unauthorized access and data breaches.
04
Implement firewall and intrusion detection systems. These tools can help monitor and block any suspicious activity on your network, ensuring that only authorized users can access your network resources.
05
Train your employees on network security best practices. Educate your staff on how to create strong passwords, recognize phishing attempts, and securely use wireless networks to minimize the risk of security breaches.
06
Regularly update and patch your network devices. Stay up to date with the latest security updates and patches released by networking technology vendors to ensure that potential vulnerabilities are addressed promptly.
07
Perform regular network security audits. Conduct periodic assessments of your network security infrastructure to identify any weaknesses or areas that need improvement.
Who needs networking technology networking security?
01
Businesses of all sizes, from small startups to large corporations, need networking technology networking security to protect their sensitive data and prevent unauthorized access.
02
Government agencies and organizations that deal with classified information or handle sensitive data related to national security also require robust network security measures.
03
Educational institutions, healthcare facilities, and financial organizations are examples of industries that handle large amounts of sensitive data and need to prioritize network security to prevent data breaches.
04
Individuals who use networking technology for personal or professional purposes also benefit from networking security measures to protect their online privacy and prevent identity theft.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I complete networking technology networking security online?
With pdfFiller, you may easily complete and sign networking technology networking security online. It lets you modify original PDF material, highlight, blackout, erase, and write text anywhere on a page, legally eSign your document, and do a lot more. Create a free account to handle professional papers online.
How do I make edits in networking technology networking security without leaving Chrome?
Install the pdfFiller Google Chrome Extension to edit networking technology networking security and other documents straight from Google search results. When reading documents in Chrome, you may edit them. Create fillable PDFs and update existing PDFs using pdfFiller.
Can I create an electronic signature for signing my networking technology networking security in Gmail?
It's easy to make your eSignature with pdfFiller, and then you can sign your networking technology networking security right from your Gmail inbox with the help of pdfFiller's add-on for Gmail. This is a very important point: You must sign up for an account so that you can save your signatures and signed documents.
What is networking technology networking security?
Networking technology networking security refers to the measures put in place to protect a network from unauthorized access and cyber attacks.
Who is required to file networking technology networking security?
Any organization or individual with a network that handles sensitive information or confidential data is required to file networking technology networking security.
How to fill out networking technology networking security?
To fill out networking technology networking security, one must assess the security risks, implement appropriate security measures, and document these measures in a security plan.
What is the purpose of networking technology networking security?
The purpose of networking technology networking security is to safeguard the confidentiality, integrity, and availability of network resources and data.
What information must be reported on networking technology networking security?
Information that must be reported on networking technology networking security includes network configurations, security protocols, access control measures, and incident response procedures.
Fill out your networking technology networking security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Networking Technology Networking Security is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.