Get the free MADE: Security Analytics for Enterprise Threat Detection
Show details
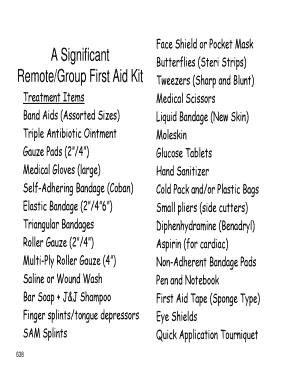
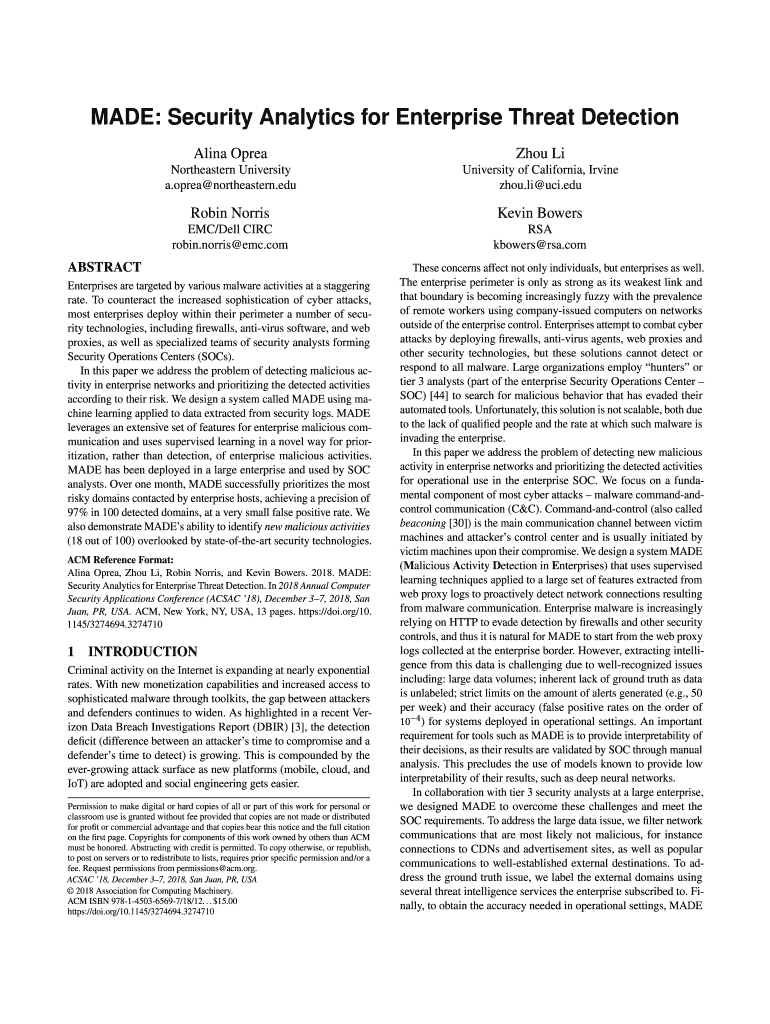
MADE: Security Analytics for Enterprise Threat Detection
Alina OpreaZhou Northeastern University
a.opera×northeastern. University of California, Irvine
Zhou. Li×UCI. Durbin Norris Kevin Bowers EMC/Dell
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign made security analytics for

Edit your made security analytics for form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your made security analytics for form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit made security analytics for online
Follow the guidelines below to benefit from a competent PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit made security analytics for. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
With pdfFiller, it's always easy to work with documents. Check it out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out made security analytics for

How to fill out made security analytics for
01
Start by gathering all the necessary data and information related to security incidents, threats, and vulnerabilities.
02
Analyze the gathered data and identify patterns, trends, and potential risks.
03
Use specialized security analytics tools or software to process and analyze the data effectively.
04
Create visualizations or reports to present the findings and insights obtained from the analysis.
05
Interpret the results and make appropriate recommendations or take necessary actions to enhance security measures.
06
Regularly update and review the security analytics process to adapt to changing threats and ensure its effectiveness.
Who needs made security analytics for?
01
Organizations or businesses that want to proactively identify and mitigate security risks.
02
Security teams or professionals responsible for ensuring the security of an organization's assets and data.
03
Companies in highly regulated industries that need to comply with security standards and regulations.
04
IT departments or administrators looking to enhance their incident detection and response capabilities.
05
Any individual or organization concerned about safeguarding sensitive information and preventing potential breaches.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I edit made security analytics for from Google Drive?
It is possible to significantly enhance your document management and form preparation by combining pdfFiller with Google Docs. This will allow you to generate papers, amend them, and sign them straight from your Google Drive. Use the add-on to convert your made security analytics for into a dynamic fillable form that can be managed and signed using any internet-connected device.
Can I sign the made security analytics for electronically in Chrome?
You certainly can. You get not just a feature-rich PDF editor and fillable form builder with pdfFiller, but also a robust e-signature solution that you can add right to your Chrome browser. You may use our addon to produce a legally enforceable eSignature by typing, sketching, or photographing your signature with your webcam. Choose your preferred method and eSign your made security analytics for in minutes.
How do I edit made security analytics for straight from my smartphone?
You can easily do so with pdfFiller's apps for iOS and Android devices, which can be found at the Apple Store and the Google Play Store, respectively. You can use them to fill out PDFs. We have a website where you can get the app, but you can also get it there. When you install the app, log in, and start editing made security analytics for, you can start right away.
What is made security analytics for?
Made security analytics is used to analyze and identify potential security threats and vulnerabilities in an organization's network or systems.
Who is required to file made security analytics for?
Organizations that handle sensitive data or have critical infrastructure are required to file made security analytics.
How to fill out made security analytics for?
Made security analytics can be filled out by collecting data on network traffic, system logs, and security events, and then analyzing this data for any anomalies or suspicious activities.
What is the purpose of made security analytics for?
The purpose of made security analytics is to enhance the overall security posture of an organization by proactively identifying and mitigating security risks.
What information must be reported on made security analytics for?
Information such as IP addresses, user activity, device information, and security incidents must be reported on made security analytics.
Fill out your made security analytics for online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Made Security Analytics For is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.