Get the free Secure Software Configuration Standard - UC IT security
Show details
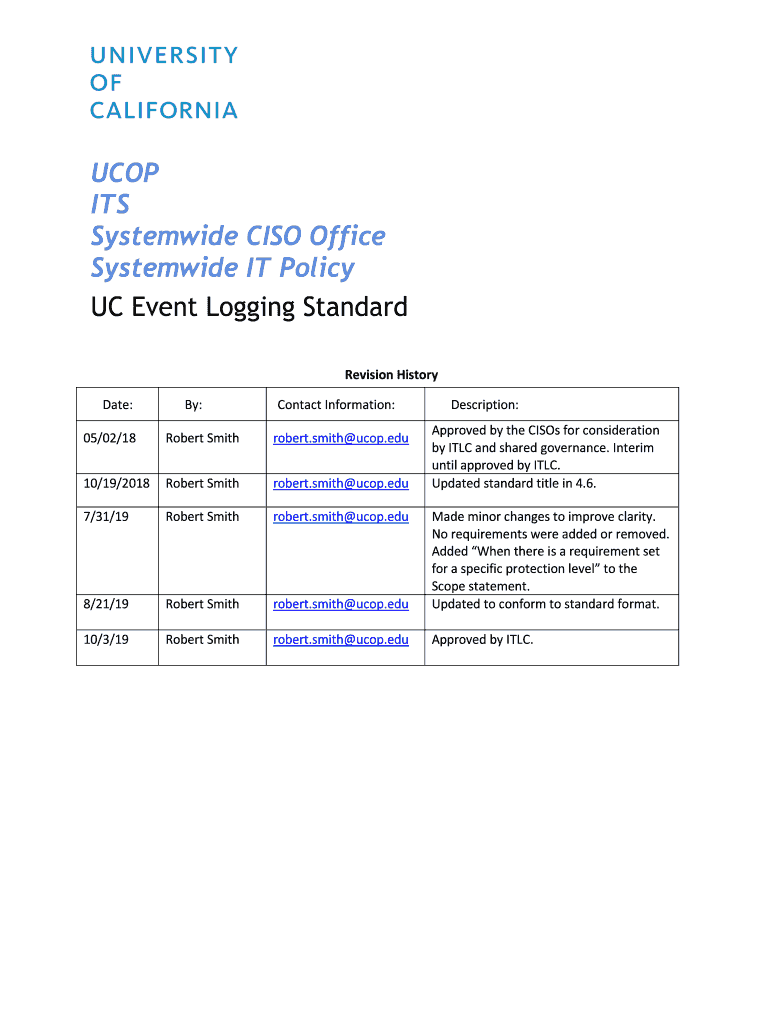
COP
ITS
System wide CIO Office
System wide IT Policy
UC Event Logging Standard
Revision History
Date:By:Contact Information:Description:
Approved by the Ciaos for consideration
by TLC and shared governance.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign secure software configuration standard

Edit your secure software configuration standard form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your secure software configuration standard form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing secure software configuration standard online
Follow the steps below to benefit from a competent PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit secure software configuration standard. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
pdfFiller makes working with documents easier than you could ever imagine. Try it for yourself by creating an account!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out secure software configuration standard

How to fill out secure software configuration standard
01
To fill out the secure software configuration standard, follow these steps:
02
Start by gathering information about the software being configured. This includes details such as the version, vendor, and specific configuration requirements.
03
Understand the security requirements for the software. This may involve consulting relevant security standards or guidelines.
04
Identify the secure configuration settings that need to be implemented. This can include options related to authentication, access controls, encryption, logging, etc.
05
Document the recommended secure configuration settings in a standard format, such as a configuration checklist or a configuration guide.
06
Prioritize the configuration settings based on their importance and potential impact on security.
07
Provide clear instructions on how to apply each configuration setting. This can involve providing step-by-step instructions, command-line examples, or configuration file modifications.
08
Include any necessary references or resources that can help implement the secure configuration settings. This may include links to relevant documentation, tools, or additional guidance.
09
Test the configured software to ensure that the secure settings have been applied correctly and are functioning as intended.
10
Continuously monitor and update the secure software configuration as new vulnerabilities or security best practices emerge.
11
Regularly review and reassess the secure software configuration to ensure it remains up-to-date and aligned with the latest security requirements and industry standards.
Who needs secure software configuration standard?
01
Secure software configuration standards are beneficial for various entities including:
02
- Organizations that develop and deploy software applications to ensure their products and systems are securely configured.
03
- System administrators and IT professionals who are responsible for configuring and managing software in an organization's infrastructure.
04
- Security professionals who provide guidance and recommendations for secure software configuration practices.
05
- Auditors and compliance officers who assess and verify that secure software configuration standards are being followed.
06
- Regulatory bodies and government agencies that enforce security standards and regulations for software systems.
07
- Any individual or organization concerned about the security of their software and the potential risks associated with misconfiguration.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I edit secure software configuration standard from Google Drive?
People who need to keep track of documents and fill out forms quickly can connect PDF Filler to their Google Docs account. This means that they can make, edit, and sign documents right from their Google Drive. Make your secure software configuration standard into a fillable form that you can manage and sign from any internet-connected device with this add-on.
How do I complete secure software configuration standard online?
pdfFiller makes it easy to finish and sign secure software configuration standard online. It lets you make changes to original PDF content, highlight, black out, erase, and write text anywhere on a page, legally eSign your form, and more, all from one place. Create a free account and use the web to keep track of professional documents.
How can I fill out secure software configuration standard on an iOS device?
Download and install the pdfFiller iOS app. Then, launch the app and log in or create an account to have access to all of the editing tools of the solution. Upload your secure software configuration standard from your device or cloud storage to open it, or input the document URL. After filling out all of the essential areas in the document and eSigning it (if necessary), you may save it or share it with others.
What is secure software configuration standard?
Secure software configuration standard is a set of guidelines and best practices that are designed to ensure that software systems are configured securely to minimize security vulnerabilities.
Who is required to file secure software configuration standard?
Organizations that handle sensitive data or operate critical infrastructure are usually required to file secure software configuration standard.
How to fill out secure software configuration standard?
To fill out secure software configuration standard, organizations need to review their software configuration settings, identify any potential security gaps, and implement the necessary changes to address those gaps.
What is the purpose of secure software configuration standard?
The purpose of secure software configuration standard is to help organizations protect their systems and data from security threats by ensuring that software is properly configured and secured.
What information must be reported on secure software configuration standard?
Secure software configuration standard typically requires organizations to document their software configuration settings, identify any security vulnerabilities, and outline their plans for remediation.
Fill out your secure software configuration standard online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Secure Software Configuration Standard is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.