Get the free Sophos Phish Threat. Simulation and Training for Your Users.
Show details
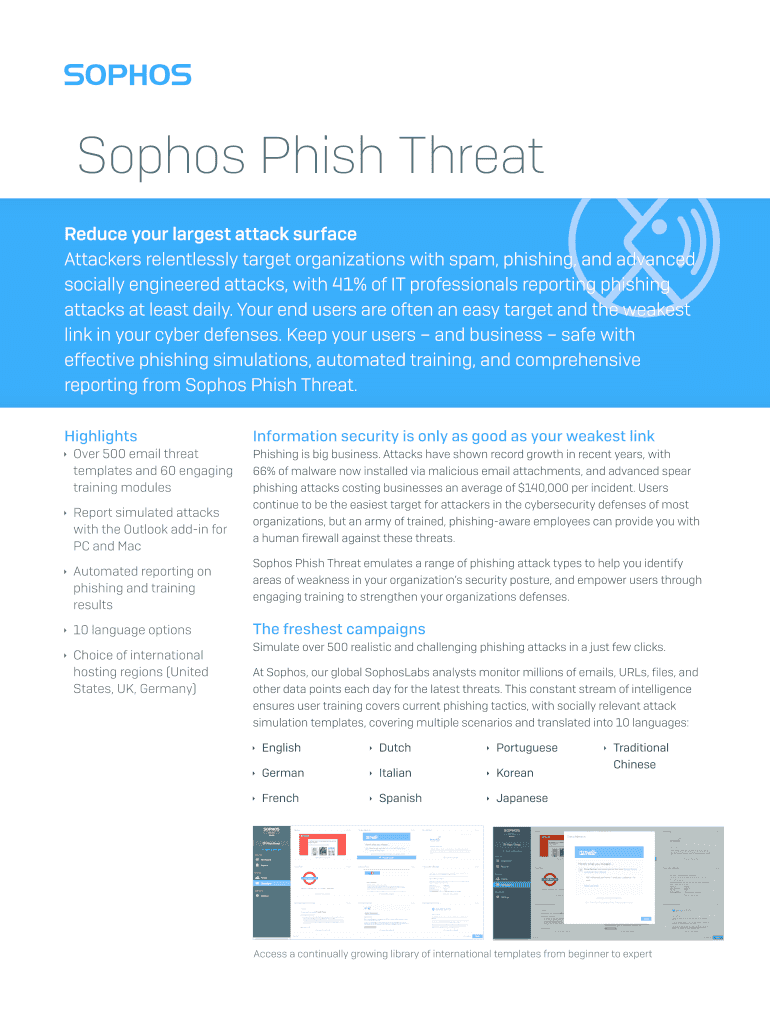
Sophos Phish Threat Reduce your largest attack surface Attackers relentlessly target organizations with spam, phishing, and advanced socially engineered attacks, with 41% of IT professionals reporting
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign sophos phish threat simulation

Edit your sophos phish threat simulation form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your sophos phish threat simulation form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit sophos phish threat simulation online
Use the instructions below to start using our professional PDF editor:
1
Log in to your account. Click on Start Free Trial and sign up a profile if you don't have one.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit sophos phish threat simulation. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out sophos phish threat simulation

How to fill out sophos phish threat simulation
01
To fill out the Sophos Phish Threat Simulation, follow these steps:
1. Log in to the Sophos Phish Threat console using your credentials.
2. Click on the 'Campaigns' tab to access the Campaigns dashboard.
3. Click on the 'New Campaign' button to create a new simulation campaign.
4. Fill in the details for the campaign, such as name, description, and target audience.
5. Select the type of phishing templates you want to use for the simulation.
6. Specify the duration and schedule of the campaign.
7. Choose the desired reporting settings and recipient(s) for the campaign results.
8. Click on the 'Save' or 'Next' button to proceed.
9. Customize the email templates, landing pages, and other settings as per your requirements.
10. Review and finalize the campaign settings.
11. Click on the 'Launch' button to start the phish threat simulation campaign.
12. Monitor the progress and results of the campaign through the Sophos Phish Threat console.
02
Who needs sophos phish threat simulation?
01
Sophos Phish Threat Simulation is useful for organizations and businesses of all sizes that want to educate and train their employees on identifying and responding to phishing attacks. It is particularly beneficial for:
1. IT security teams and administrators who want to assess and improve their organization's resilience against phishing attacks.
2. Employees who need training and awareness on the tactics used by cybercriminals through simulated phishing campaigns.
3. Organizations that handle sensitive data or have compliance requirements, such as healthcare, finance, government, or legal sectors.
4. Businesses looking to reduce the risk of successful phishing attacks and protect their sensitive information.
5. Companies that prioritize cybersecurity and want to create a security-conscious culture among their employees.
02
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I get sophos phish threat simulation?
The premium subscription for pdfFiller provides you with access to an extensive library of fillable forms (over 25M fillable templates) that you can download, fill out, print, and sign. You won’t have any trouble finding state-specific sophos phish threat simulation and other forms in the library. Find the template you need and customize it using advanced editing functionalities.
How do I make changes in sophos phish threat simulation?
With pdfFiller, the editing process is straightforward. Open your sophos phish threat simulation in the editor, which is highly intuitive and easy to use. There, you’ll be able to blackout, redact, type, and erase text, add images, draw arrows and lines, place sticky notes and text boxes, and much more.
Can I create an eSignature for the sophos phish threat simulation in Gmail?
It's easy to make your eSignature with pdfFiller, and then you can sign your sophos phish threat simulation right from your Gmail inbox with the help of pdfFiller's add-on for Gmail. This is a very important point: You must sign up for an account so that you can save your signatures and signed documents.
What is sophos phish threat simulation?
Sophos Phish Threat Simulation is a security tool designed to help organizations identify and mitigate phishing attacks by simulating real-world phishing scenarios.
Who is required to file sophos phish threat simulation?
Organizations that want to assess their employees' susceptibility to phishing attacks and improve their security awareness are required to use Sophos Phish Threat Simulation.
How to fill out sophos phish threat simulation?
To fill out Sophos Phish Threat Simulation, organizations need to set up phishing simulation campaigns, monitor employee responses, and analyze the results to identify areas for improvement in security awareness.
What is the purpose of sophos phish threat simulation?
The purpose of Sophos Phish Threat Simulation is to help organizations train their employees to recognize and respond to phishing attacks, ultimately reducing the risk of falling victim to such attacks.
What information must be reported on sophos phish threat simulation?
On Sophos Phish Threat Simulation, organizations must report the results of phishing simulation campaigns, including the number of employees who fell for the simulated attacks and any trends or patterns observed in their responses.
Fill out your sophos phish threat simulation online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Sophos Phish Threat Simulation is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.