Get the free List of attacks related to secondary schools - Wikipedia
Show details
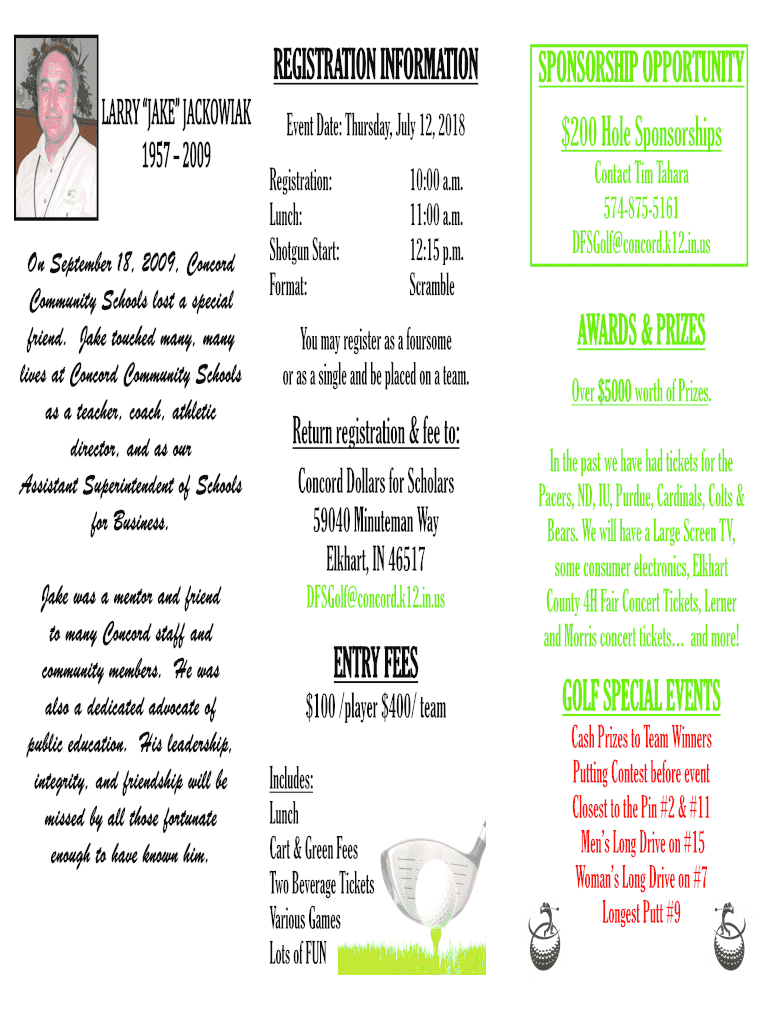
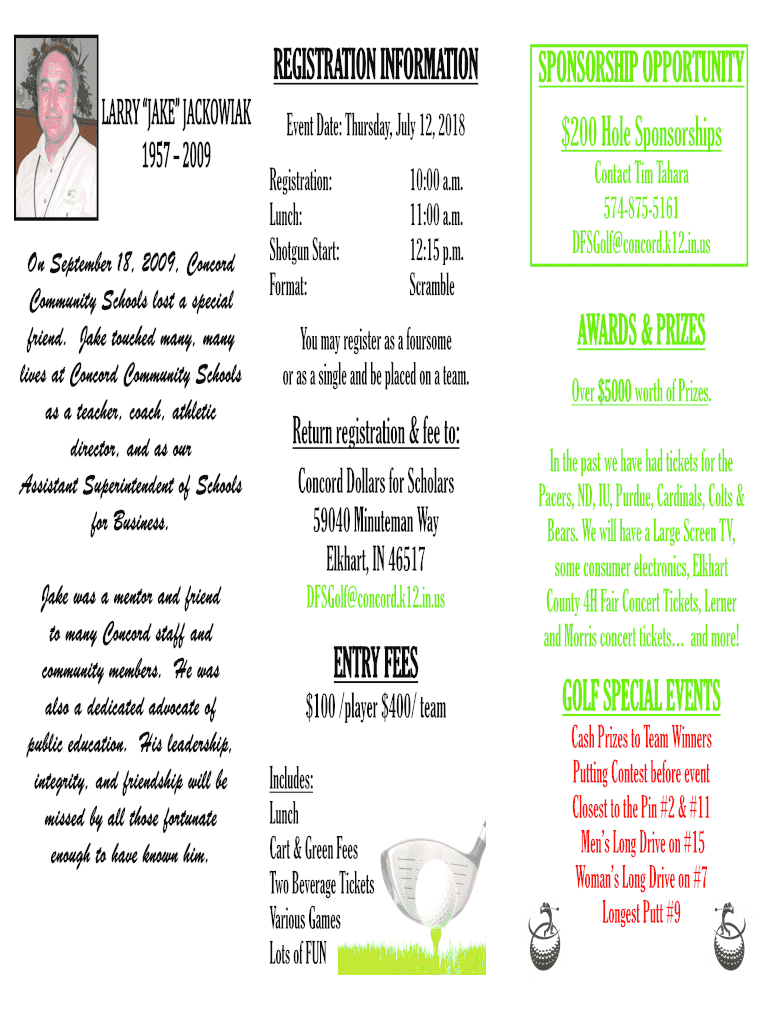
On September 18, 2009, Concord
Community Schools lost a special
friend. Jake touched many, many
lives at Concord Community Schools
as a teacher, coach, athletic
director, and as our
Assistant Superintendent
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign list of attacks related

Edit your list of attacks related form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your list of attacks related form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit list of attacks related online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit list of attacks related. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out list of attacks related

How to fill out list of attacks related
01
Begin by researching and gathering information about various attacks related to the topic you are focusing on.
02
Create a list of the different types of attacks that have occurred in the past or are currently happening.
03
For each attack, include relevant details such as the date of occurrence, the target, the method used, and the impact it had.
04
Organize the list in a logical manner, such as grouping attacks by their nature or the industry they targeted.
05
Use reliable sources and provide proper citations for each attack included in the list.
06
Regularly update the list to include new attacks or remove outdated information.
07
Consider adding additional information, such as preventive measures or lessons learned from each attack.
08
Format the list in a clear and concise manner to make it easily understandable for readers.
09
Proofread the list to ensure it is free from grammatical or spelling errors.
10
Share the list with relevant stakeholders, such as cybersecurity professionals, researchers, or individuals interested in learning about attacks related to the topic.
Who needs list of attacks related?
01
Cybersecurity professionals who want to stay updated on various attacks and their characteristics.
02
Researchers studying attack patterns and trends.
03
Organizations and businesses looking to enhance their security measures by understanding the types of attacks that can occur.
04
Individuals interested in learning about the latest cyber threats and how to protect themselves online.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I manage my list of attacks related directly from Gmail?
In your inbox, you may use pdfFiller's add-on for Gmail to generate, modify, fill out, and eSign your list of attacks related and any other papers you receive, all without leaving the program. Install pdfFiller for Gmail from the Google Workspace Marketplace by visiting this link. Take away the need for time-consuming procedures and handle your papers and eSignatures with ease.
How can I get list of attacks related?
The pdfFiller premium subscription gives you access to a large library of fillable forms (over 25 million fillable templates) that you can download, fill out, print, and sign. In the library, you'll have no problem discovering state-specific list of attacks related and other forms. Find the template you want and tweak it with powerful editing tools.
How do I fill out list of attacks related using my mobile device?
Use the pdfFiller mobile app to complete and sign list of attacks related on your mobile device. Visit our web page (https://edit-pdf-ios-android.pdffiller.com/) to learn more about our mobile applications, the capabilities you’ll have access to, and the steps to take to get up and running.
What is list of attacks related?
List of attacks related is a document that lists all the attacks or security breaches related to a certain incident.
Who is required to file list of attacks related?
The organization or entity that experienced the attacks or security breaches is required to file the list of attacks related.
How to fill out list of attacks related?
The list of attacks related should be filled out with detailed information about each attack, including the date, time, nature of the attack, and any impact on the organization.
What is the purpose of list of attacks related?
The purpose of the list of attacks related is to provide a comprehensive record of all attacks or security breaches related to a specific incident for documentation and analysis purposes.
What information must be reported on list of attacks related?
The list of attacks related must include information such as the date and time of each attack, the nature of the attack, any impact on the organization, and any response actions taken.
Fill out your list of attacks related online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
List Of Attacks Related is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.