Get the free Remote Mobile Access Deployment Guide - Cisco
Show details
SBA SOLUTIONS BYOD Remote Mobile Access Deployment GUI
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign remote mobile access deployment

Edit your remote mobile access deployment form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your remote mobile access deployment form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing remote mobile access deployment online
In order to make advantage of the professional PDF editor, follow these steps below:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit remote mobile access deployment. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
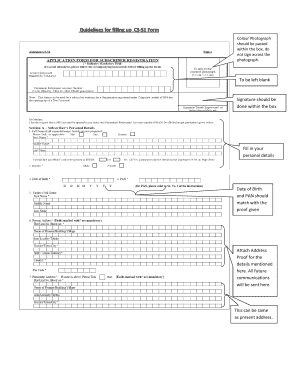
How to fill out remote mobile access deployment

How to fill out remote mobile access deployment:
01
Identify the specific needs of your organization: Before filling out the deployment plan, it is important to understand the purpose of remote mobile access and how it aligns with your organization's goals and objectives.
02
Assess the existing infrastructure: Evaluate your current network infrastructure and determine if it can support remote mobile access. This includes reviewing your network security measures, bandwidth availability, and network stability.
03
Select the appropriate remote mobile access solution: Research and choose a remote mobile access solution that best fits your organization's requirements. Consider factors such as ease of use, security features, compatibility with your existing systems, and scalability.
04
Develop a deployment plan: Create a detailed plan outlining the steps, timeline, and resources required for implementing remote mobile access. This includes identifying the key stakeholders, assigning responsibilities, and setting milestones for each phase of the deployment.
05
Train your staff: Provide training and support to your employees to ensure they understand how to use remote mobile access securely and efficiently. This may include educating them on best practices, conducting workshops or webinars, and offering ongoing technical support.
06
Test and optimize the system: Before full deployment, conduct thorough testing to ensure that the remote mobile access solution functions properly and meets your organization's needs. Address any issues or vulnerabilities identified during the testing phase and optimize the system for optimal performance.
07
Monitor and evaluate the implementation: Once the remote mobile access deployment is complete, regularly monitor and evaluate its effectiveness. Collect feedback from users, assess system performance, and make any necessary adjustments to enhance its functionality and security.
Who needs remote mobile access deployment:
01
Organizations with a mobile workforce: Companies with employees who work remotely or frequently travel often require remote mobile access to enable them to access company resources and collaborate with colleagues from anywhere.
02
Businesses with multiple locations: Companies with multiple offices or branches may need remote mobile access to ensure seamless connectivity and access to shared resources across all locations.
03
Industries with strict security requirements: Sectors such as healthcare, finance, and legal services often handle sensitive data and therefore require secure remote mobile access solutions to protect confidential information while allowing authorized users to access it remotely.
04
Remote IT support teams: IT support teams that provide assistance and troubleshoot technical issues for remote users need remote mobile access to remotely connect to users' devices and resolve any issues without physical proximity.
05
Organizations promoting work-life balance: Companies that prioritize work-life balance and offer flexible work arrangements often provide remote mobile access to allow employees to access work-related resources outside the office, enabling them to work remotely when needed.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is remote mobile access deployment?
Remote mobile access deployment refers to the process of setting up and enabling access to a company's systems and data from mobile devices outside of the office network.
Who is required to file remote mobile access deployment?
Companies and organizations that provide remote access to their systems and data via mobile devices are required to file remote mobile access deployment.
How to fill out remote mobile access deployment?
To fill out remote mobile access deployment, companies need to document the details of their mobile access policies, procedures, and systems used for remote access.
What is the purpose of remote mobile access deployment?
The purpose of remote mobile access deployment is to ensure secure and efficient access to company systems and data from mobile devices outside of the office environment.
What information must be reported on remote mobile access deployment?
Information that must be reported on remote mobile access deployment includes details of the mobile devices used, security measures in place, access policies, and user authentication methods.
How do I edit remote mobile access deployment in Chrome?
Get and add pdfFiller Google Chrome Extension to your browser to edit, fill out and eSign your remote mobile access deployment, which you can open in the editor directly from a Google search page in just one click. Execute your fillable documents from any internet-connected device without leaving Chrome.
Can I create an electronic signature for signing my remote mobile access deployment in Gmail?
Upload, type, or draw a signature in Gmail with the help of pdfFiller’s add-on. pdfFiller enables you to eSign your remote mobile access deployment and other documents right in your inbox. Register your account in order to save signed documents and your personal signatures.
How do I complete remote mobile access deployment on an iOS device?
Make sure you get and install the pdfFiller iOS app. Next, open the app and log in or set up an account to use all of the solution's editing tools. If you want to open your remote mobile access deployment, you can upload it from your device or cloud storage, or you can type the document's URL into the box on the right. After you fill in all of the required fields in the document and eSign it, if that is required, you can save or share it with other people.
Fill out your remote mobile access deployment online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Remote Mobile Access Deployment is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.