Get the free Searching and Seizing Computers and Obtaining ... - First Circuit
Show details
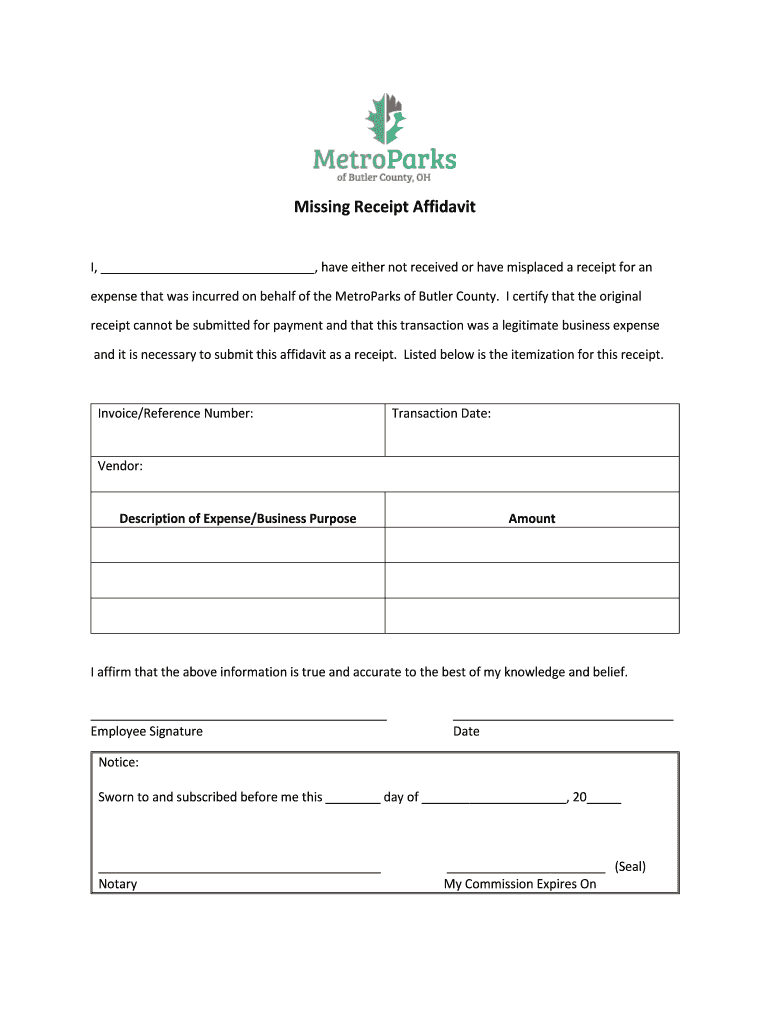
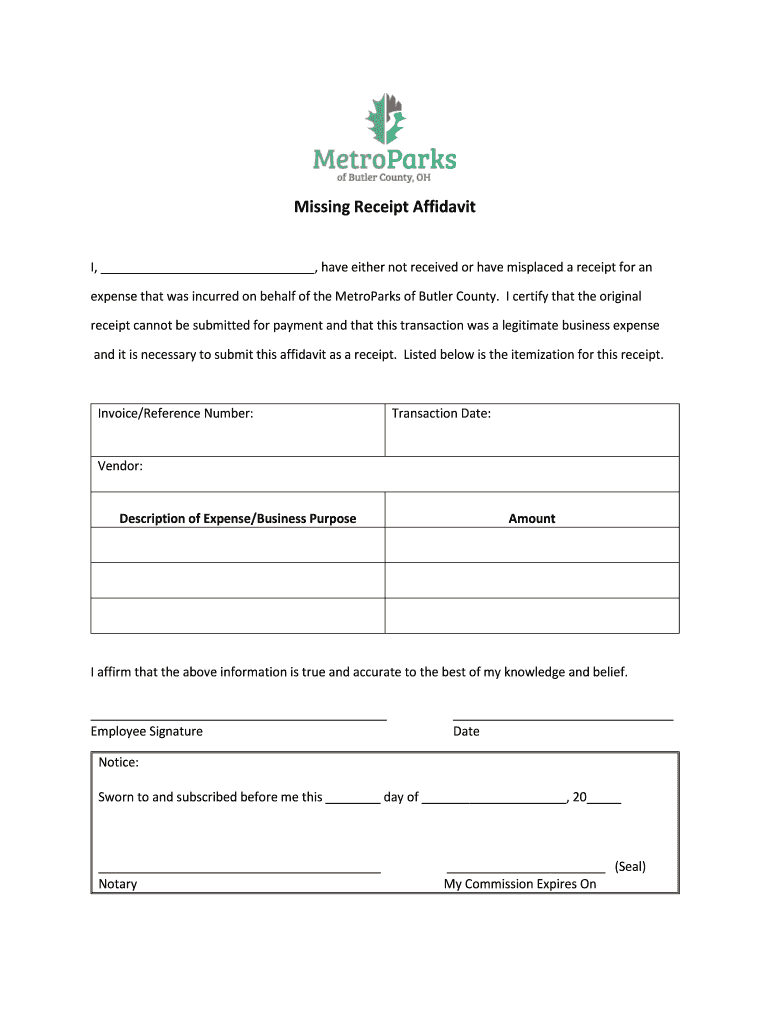
Missing Receipt Affidavit I, have either not received or have misplaced a receipt for an expense that was incurred on behalf of the Metro Parks of Butler County. I certify that the original receipt
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign searching and seizing computers

Edit your searching and seizing computers form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your searching and seizing computers form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing searching and seizing computers online
Follow the guidelines below to use a professional PDF editor:
1
Check your account. It's time to start your free trial.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit searching and seizing computers. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Select it in the list of your records. Then, move the cursor to the right toolbar and choose one of the available exporting methods: save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out searching and seizing computers

How to fill out searching and seizing computers
01
To fill out searching and seizing computers, follow these steps:
02
Start by obtaining a search warrant from a court or an authorized judicial officer.
03
Gather all necessary equipment such as gloves, evidence bags, and forensic tools.
04
Ensure that the computers to be searched are powered off and disconnected from any network.
05
Take photographs of the computers and their surrounding environment for documentation purposes.
06
Use specialized software or hardware tools to make a bit-by-bit copy of the computer's hard drive.
07
Preserve the integrity of the evidence by using write-blockers to prevent any modifications to the original data.
08
Collect any other relevant physical or digital evidence found during the search.
09
Document the entire process, including the date, time, and individuals present during the search.
10
Securely package and label all seized items, ensuring proper chain of custody.
11
Finally, submit the seized computers and evidence to the appropriate legal authority for further analysis and use in legal proceedings.
Who needs searching and seizing computers?
01
Searching and seizing computers may be required by law enforcement agencies during criminal investigations.
02
Government agencies, such as cybercrime units, may also need to search and seize computers to gather evidence of illegal activities.
03
In certain cases, private organizations or individuals authorized by law may need to search and seize computers for legal or security reasons.
04
It is important to note that the process of searching and seizing computers should always be done in compliance with applicable laws and regulations.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send searching and seizing computers to be eSigned by others?
When your searching and seizing computers is finished, send it to recipients securely and gather eSignatures with pdfFiller. You may email, text, fax, mail, or notarize a PDF straight from your account. Create an account today to test it.
Can I create an electronic signature for signing my searching and seizing computers in Gmail?
Create your eSignature using pdfFiller and then eSign your searching and seizing computers immediately from your email with pdfFiller's Gmail add-on. To keep your signatures and signed papers, you must create an account.
How do I fill out searching and seizing computers using my mobile device?
Use the pdfFiller mobile app to fill out and sign searching and seizing computers on your phone or tablet. Visit our website to learn more about our mobile apps, how they work, and how to get started.
What is searching and seizing computers?
Searching and seizing computers refers to the process of obtaining and collecting electronic devices such as computers, laptops, and servers as part of an investigation or legal procedure.
Who is required to file searching and seizing computers?
Law enforcement agencies or authorized personnel are required to file searching and seizing computers.
How to fill out searching and seizing computers?
To fill out searching and seizing computers, detailed information about the electronic devices seized, reason for seizure, date, time, location, and individuals involved must be documented.
What is the purpose of searching and seizing computers?
The purpose of searching and seizing computers is to gather digital evidence that may be relevant to an investigation or legal case.
What information must be reported on searching and seizing computers?
Information such as the make and model of the seized devices, serial numbers, data storage capacity, and any files or documents found on the devices must be reported.
Fill out your searching and seizing computers online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Searching And Seizing Computers is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.