Get the free Question: Effectiveness of Attack roll attacks/spells vs Saving ...
Show details
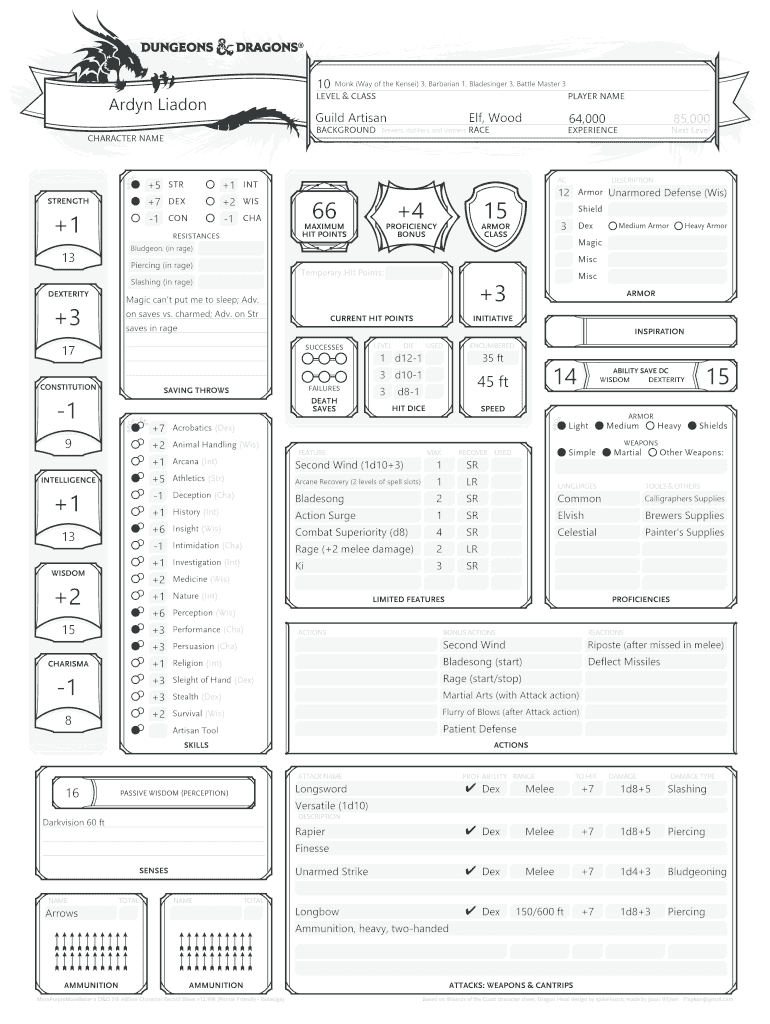
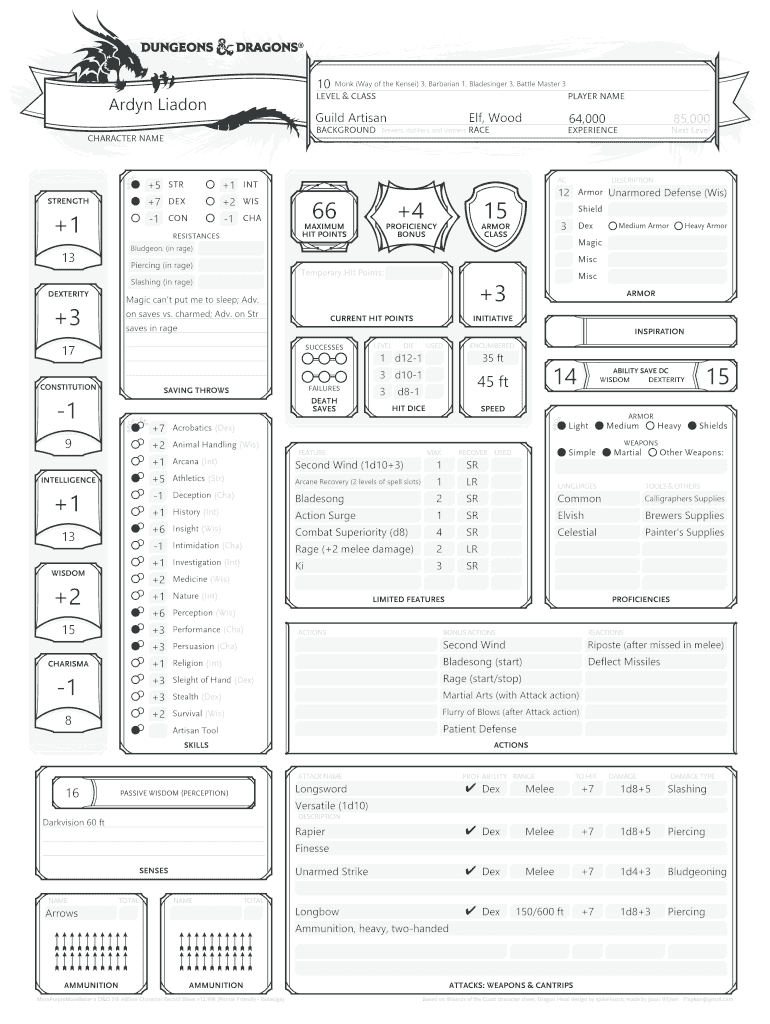
Show extra features10Ardyn LiadonCLICK HERE TO CHANGE THIS ICONBACKGROUNDF +5 STR +7 DEX1 MAXIMUM HIT POINTSRESISTANCESDEXTERITYDESCRIPTIONShield3ARMOR CLASSTemporary Hit Points:Demon saves vs. charmed;
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign question effectiveness of attack
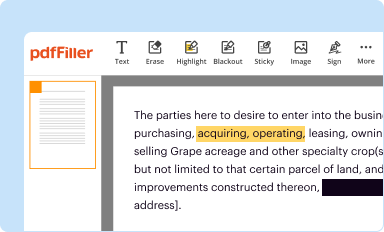
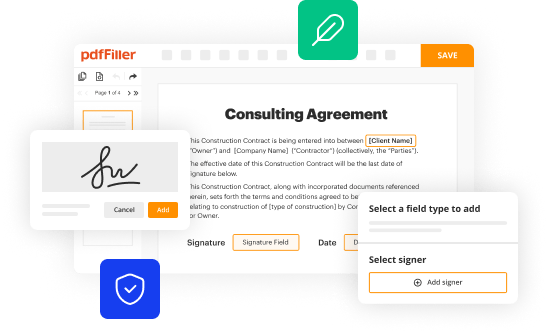
Edit your question effectiveness of attack form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
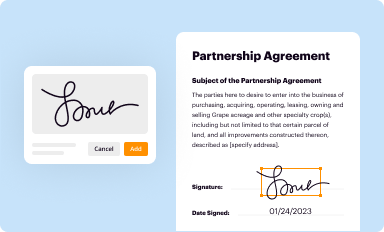
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
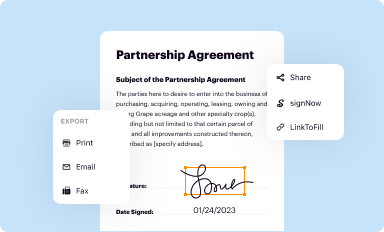
Share your form instantly
Email, fax, or share your question effectiveness of attack form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit question effectiveness of attack online
Follow the steps down below to benefit from the PDF editor's expertise:
1
Check your account. If you don't have a profile yet, click Start Free Trial and sign up for one.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit question effectiveness of attack. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
pdfFiller makes working with documents easier than you could ever imagine. Register for an account and see for yourself!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out question effectiveness of attack
How to fill out question effectiveness of attack
01
To fill out the question effectiveness of attack, follow these steps:
1. Start by gathering data on the attack, including details such as the type of attack, the time and location it occurred, and any known targets or casualties.
02
Analyze the impact and consequences of the attack, considering factors such as the number of casualties, the level of damage inflicted, and the extent of disruption caused.
03
Assess the success of countermeasures or defensive measures taken against the attack, evaluating the effectiveness of security protocols and response strategies.
04
Examine the broader implications of the attack, such as its impact on public perception, economic stability, or national security.
05
Consider the long-term effects of the attack, including its potential to influence future security strategies and policies.
06
Summarize your findings and conclusions regarding the effectiveness of the attack, providing a comprehensive assessment of its overall impact and success.
Who needs question effectiveness of attack?
01
Various entities and individuals can benefit from assessing the effectiveness of an attack, including:
02
- Government agencies and intelligence organizations, who seek to evaluate security measures and identify vulnerabilities.
03
- Military and defense institutions, who aim to understand the success of offensive or defensive operations and improve future strategies.
04
- Risk management professionals and security consultants, who need to assess threats and recommend appropriate mitigation measures.
05
- Researchers and academics in the field of security and political science, who study the dynamics of attacks and their consequences.
06
- Law enforcement agencies and criminal investigators, who investigate attacks and try to determine their effectiveness in identifying culprits or preventing further incidents.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send question effectiveness of attack to be eSigned by others?
Once your question effectiveness of attack is complete, you can securely share it with recipients and gather eSignatures with pdfFiller in just a few clicks. You may transmit a PDF by email, text message, fax, USPS mail, or online notarization directly from your account. Make an account right now and give it a go.
Can I create an electronic signature for signing my question effectiveness of attack in Gmail?
It's easy to make your eSignature with pdfFiller, and then you can sign your question effectiveness of attack right from your Gmail inbox with the help of pdfFiller's add-on for Gmail. This is a very important point: You must sign up for an account so that you can save your signatures and signed documents.
Can I edit question effectiveness of attack on an iOS device?
Create, modify, and share question effectiveness of attack using the pdfFiller iOS app. Easy to install from the Apple Store. You may sign up for a free trial and then purchase a membership.
What is question effectiveness of attack?
The question effectiveness of attack is a report that assesses the success and impact of an attack on a target.
Who is required to file question effectiveness of attack?
The question effectiveness of attack report is typically filed by security analysts or incident response teams.
How to fill out question effectiveness of attack?
The question effectiveness of attack report can be filled out by documenting the details of the attack, including the methods used, impact on target, and mitigation strategies.
What is the purpose of question effectiveness of attack?
The purpose of the question effectiveness of attack report is to analyze the effectiveness of security measures in place and identify areas for improvement.
What information must be reported on question effectiveness of attack?
The information reported on the question effectiveness of attack may include the date and time of the attack, the target system, attack vectors, and any vulnerabilities exploited.
Fill out your question effectiveness of attack online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Question Effectiveness Of Attack is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.