Get the free Cisco.s LEAP vulnerability and the .asleap.exploit - pen-testing sans
Show details
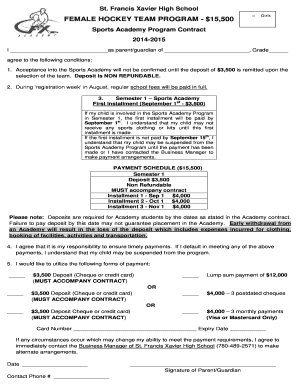
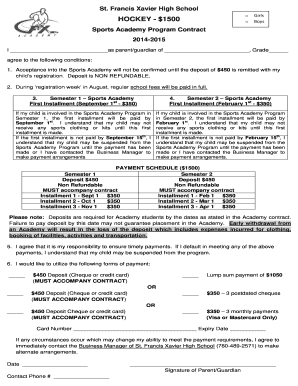
Use offense to inform defense. Find flaws before the bad guys do. Copyright SANS Institute Author Retains Full Rights This paper is from the SANS Penetration Testing site. Reposting is not permitted
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign ciscos leap vulnerability and

Edit your ciscos leap vulnerability and form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your ciscos leap vulnerability and form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit ciscos leap vulnerability and online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit ciscos leap vulnerability and. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out ciscos leap vulnerability and

How to fill out ciscos leap vulnerability and
01
To fill out Cisco's LEAP vulnerability, follow these steps:
02
Identify the affected devices or systems that are using Cisco's LEAP authentication protocol.
03
Download and install the latest firmware or software patch provided by Cisco to address the vulnerability.
04
Prioritize the vulnerable devices or systems based on their criticality and impact on your network infrastructure.
05
Develop a deployment plan for applying the patch, ensuring minimal disruption to ongoing operations.
06
Test the patch in a controlled environment to verify its effectiveness and compatibility with your existing infrastructure.
07
Schedule a maintenance window to apply the patch on the production devices or systems.
08
Communicate the planned downtime to the relevant stakeholders and users to manage expectations.
09
Apply the patch to the identified devices or systems according to the deployment plan.
10
Validate the successful application of the patch by conducting post-patching tests and monitoring.
11
Maintain ongoing vulnerability management practices by regularly checking for any new patches or updates released by Cisco, and promptly applying them to mitigate any future vulnerabilities.
Who needs ciscos leap vulnerability and?
01
Organizations or individuals who are using Cisco's LEAP authentication protocol on their network infrastructure may need to address the LEAP vulnerability.
02
LEAP (Lightweight Extensible Authentication Protocol) was a commonly used authentication protocol for Wi-Fi networks in the past, but it is now considered insecure due to multiple vulnerabilities.
03
Anyone who relies on the security and integrity of their network, especially those who have devices or systems that utilize LEAP, should be concerned about the vulnerability and take appropriate measures to address it.
04
By addressing the LEAP vulnerability, organizations can protect their network infrastructure from potential unauthorized access and data breaches.
05
It is recommended for both small and large organizations, as well as individuals, to secure their network by replacing LEAP with more secure authentication protocols, such as WPA2-Enterprise or WPA3, which provide stronger security measures.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I edit ciscos leap vulnerability and from Google Drive?
People who need to keep track of documents and fill out forms quickly can connect PDF Filler to their Google Docs account. This means that they can make, edit, and sign documents right from their Google Drive. Make your ciscos leap vulnerability and into a fillable form that you can manage and sign from any internet-connected device with this add-on.
How do I edit ciscos leap vulnerability and online?
With pdfFiller, you may not only alter the content but also rearrange the pages. Upload your ciscos leap vulnerability and and modify it with a few clicks. The editor lets you add photos, sticky notes, text boxes, and more to PDFs.
How do I fill out ciscos leap vulnerability and on an Android device?
Use the pdfFiller app for Android to finish your ciscos leap vulnerability and. The application lets you do all the things you need to do with documents, like add, edit, and remove text, sign, annotate, and more. There is nothing else you need except your smartphone and an internet connection to do this.
What is ciscos leap vulnerability and?
Cisco's LEAP vulnerability is a security flaw in the Lightweight Extensible Authentication Protocol.
Who is required to file ciscos leap vulnerability and?
Network administrators and IT security professionals.
How to fill out ciscos leap vulnerability and?
You can fill out Cisco's LEAP vulnerability report by documenting the details of the security flaw and its impact.
What is the purpose of ciscos leap vulnerability and?
The purpose of Cisco's LEAP vulnerability report is to identify and address security risks within network systems.
What information must be reported on ciscos leap vulnerability and?
Details of the security flaw, potential impact, affected systems, and mitigation steps.
Fill out your ciscos leap vulnerability and online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Ciscos Leap Vulnerability And is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.