Get the free How Cybercriminals Can Use Your Cell Phone Number to ...
Show details
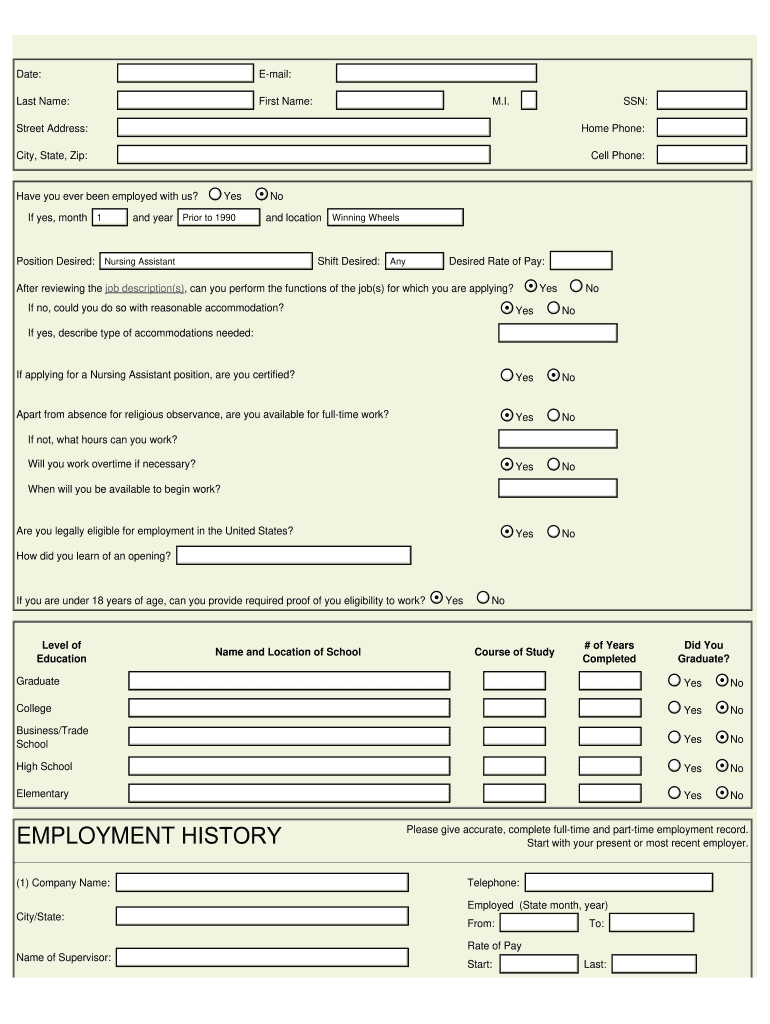
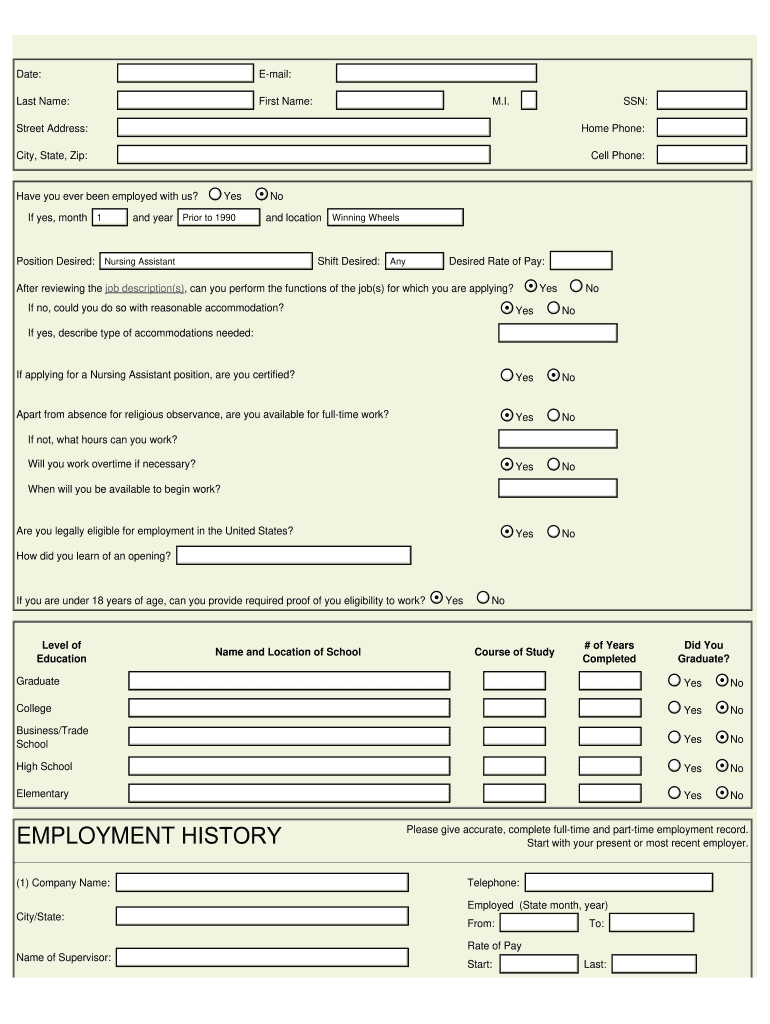
Date:Email:Last Name:First Name:M.I.SSN:Street Address:Home Phone:City, State, Zip:Cell Phone:Have you ever been employed with us?
If yes, month11YesPrior toad warrior
to1990
1990No
Winning Wheel
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign how cybercriminals can use

Edit your how cybercriminals can use form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your how cybercriminals can use form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing how cybercriminals can use online
In order to make advantage of the professional PDF editor, follow these steps:
1
Sign into your account. In case you're new, it's time to start your free trial.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit how cybercriminals can use. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Save your file. Select it in the list of your records. Then, move the cursor to the right toolbar and choose one of the available exporting methods: save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out how cybercriminals can use

How to fill out how cybercriminals can use
01
To fill out how cybercriminals can use, follow these steps:
02
Identify the vulnerabilities in your system or network that cybercriminals can exploit. This includes outdated software, weak passwords, unsecured wireless networks, and lack of firewalls or antivirus software.
03
Educate yourself and your team about common cyber threats and techniques used by cybercriminals, such as phishing, malware, ransomware, and social engineering.
04
Implement strong security measures, including regular software updates, complex passwords, encryption, and strong firewalls.
05
Train employees to recognize and avoid potential security risks, such as suspicious emails or links, and encourage them to report any incidents or concerns.
06
Monitor and analyze network traffic and logs to detect any unusual or suspicious activities. Use intrusion detection systems and other security tools to identify potential threats.
07
Regularly backup important data and store it in multiple secure locations. This will help in case of data breaches or ransomware attacks.
08
Stay updated with the latest security trends and news to adapt your security practices accordingly.
09
Conduct regular security audits and penetration testing to identify and patch any vulnerabilities before cybercriminals can exploit them.
Who needs how cybercriminals can use?
01
Anyone who wants to protect their personal or sensitive information from falling into the hands of cybercriminals needs to understand how cybercriminals can use various techniques and exploit vulnerabilities. This includes individuals, businesses, organizations, government agencies, and even educational institutions. By understanding how cybercriminals operate, people and entities can implement effective security measures and minimize the risk of cyber attacks.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I edit how cybercriminals can use from Google Drive?
pdfFiller and Google Docs can be used together to make your documents easier to work with and to make fillable forms right in your Google Drive. The integration will let you make, change, and sign documents, like how cybercriminals can use, without leaving Google Drive. Add pdfFiller's features to Google Drive, and you'll be able to do more with your paperwork on any internet-connected device.
How can I send how cybercriminals can use to be eSigned by others?
how cybercriminals can use is ready when you're ready to send it out. With pdfFiller, you can send it out securely and get signatures in just a few clicks. PDFs can be sent to you by email, text message, fax, USPS mail, or notarized on your account. You can do this right from your account. Become a member right now and try it out for yourself!
How do I edit how cybercriminals can use on an Android device?
You can make any changes to PDF files, like how cybercriminals can use, with the help of the pdfFiller Android app. Edit, sign, and send documents right from your phone or tablet. You can use the app to make document management easier wherever you are.
What is how cybercriminals can use?
Cybercriminals can use various tactics such as phishing, malware, ransomware, social engineering, and insider threats to exploit vulnerabilities in computer systems and networks.
Who is required to file how cybercriminals can use?
Anyone who handles sensitive information or has access to computer systems should be aware of how cybercriminals can use different techniques to compromise data.
How to fill out how cybercriminals can use?
It is important to educate employees on cybersecurity best practices, implement strong password policies, regularly update software, and conduct security trainings to protect against how cybercriminals can use.
What is the purpose of how cybercriminals can use?
The purpose of understanding how cybercriminals can use different tactics is to strengthen cybersecurity defenses and mitigate the risk of data breaches and cyber attacks.
What information must be reported on how cybercriminals can use?
Information such as recent cyber threats, common attack vectors, best practices for securing data, and incident response strategies should be reported on how cybercriminals can use.
Fill out your how cybercriminals can use online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
How Cybercriminals Can Use is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.




















