Get the free Computer Fraud and Abuse Act - Department of Justice
Show details
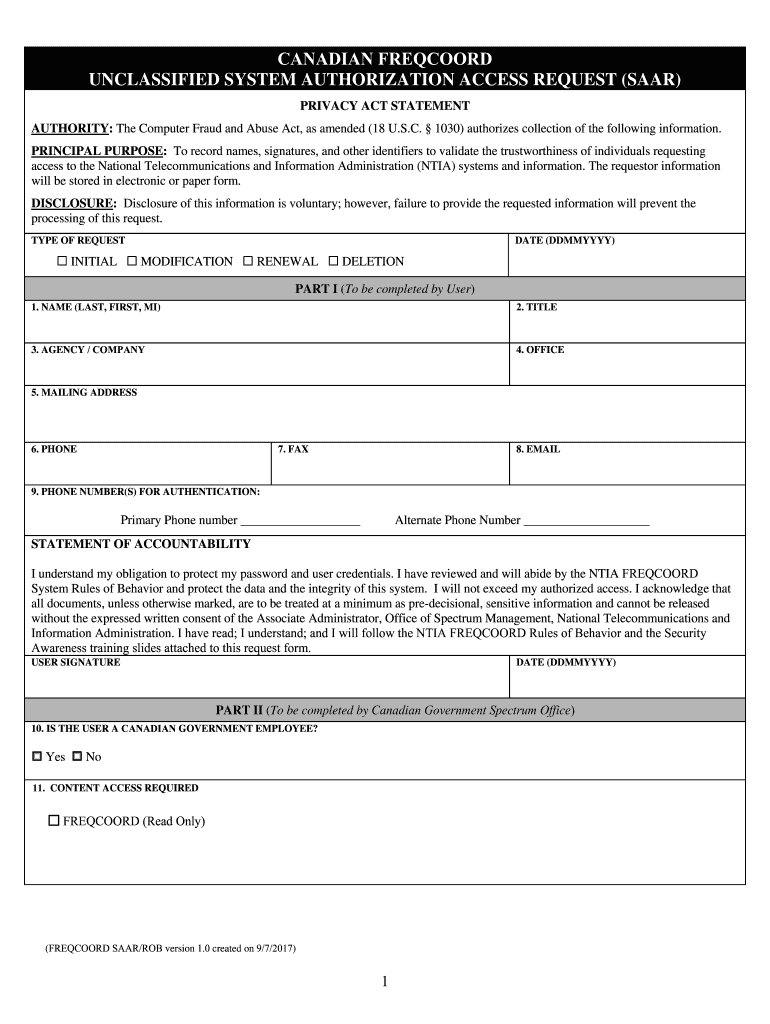
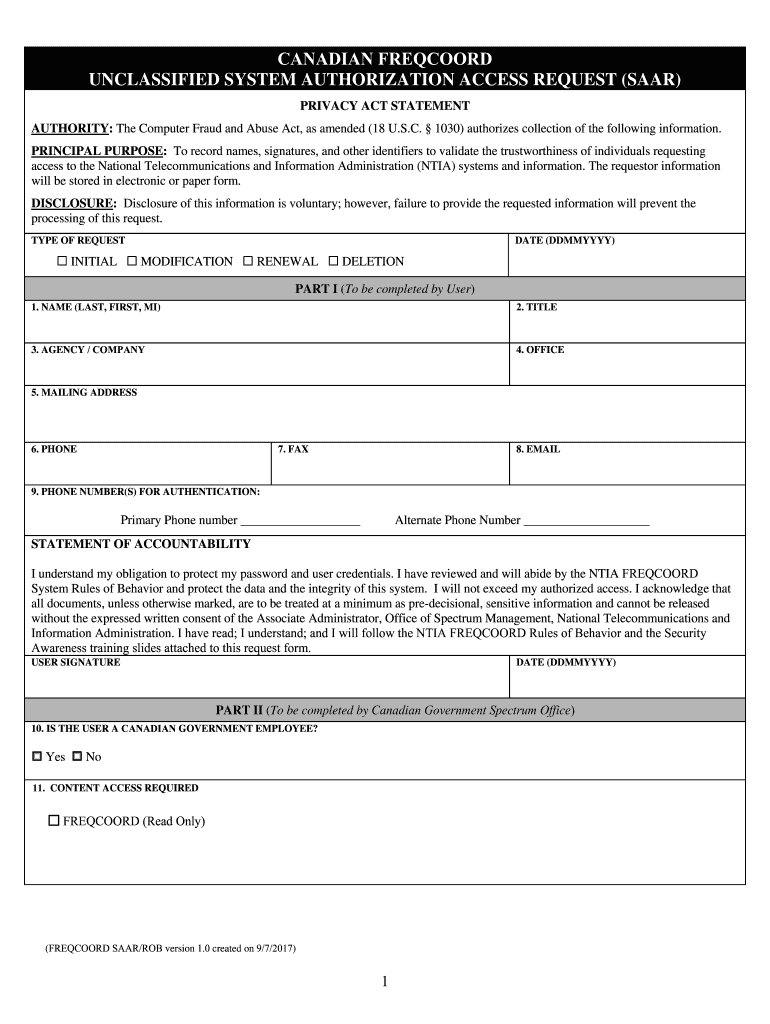
CANADIAN RECORD UNCLASSIFIED SYSTEM AUTHORIZATION ACCESS REQUEST (SAAR) PRIVACY ACT STATEMENT AUTHORITY: The Computer Fraud and Abuse Act, as amended (18 U.S.C. 1030) authorizes collection of the
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign computer fraud and abuse

Edit your computer fraud and abuse form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your computer fraud and abuse form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit computer fraud and abuse online
To use our professional PDF editor, follow these steps:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit computer fraud and abuse. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
With pdfFiller, it's always easy to deal with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
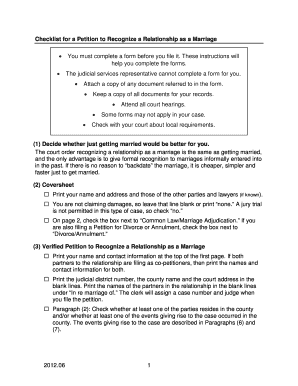
How to fill out computer fraud and abuse

How to fill out computer fraud and abuse
01
To fill out computer fraud and abuse, follow these steps:
02
Gather all the necessary information and documentation related to the incident.
03
Start by providing your personal details like name, address, and contact information.
04
Clearly describe the nature of the computer fraud and abuse you experienced.
05
Include any supporting evidence such as emails, screenshots, or log files.
06
Provide details about the perpetrator if known, including their name, contact information, and any additional relevant details.
07
Explain the impact or damages caused by the computer fraud and abuse.
08
If applicable, provide any steps you have taken to mitigate the situation or recover from the incident.
09
Review and double-check all the information you have provided for accuracy and completeness.
10
Sign and date the document to attest that the information provided is true and accurate.
11
Follow any additional instructions or requirements specified by the relevant authorities or organization.
12
Remember to keep copies of all documents submitted for your records.
Who needs computer fraud and abuse?
01
Computer fraud and abuse can affect anyone who uses computers or computer networks.
02
Specific individuals, organizations, and entities that may need to address computer fraud and abuse include:
03
- Individuals who have been victims of online scams, phishing attacks, or identity theft.
04
- Businesses or companies that experience unauthorized access or misuse of their computer systems.
05
- Government agencies or law enforcement bodies investigating cybercrimes.
06
- Internet service providers or network administrators dealing with network security breaches.
07
- Legal professionals handling cases related to computer fraud and abuse.
08
- Cybersecurity experts or consultants assisting in prevention and detection of computer fraud and abuse.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Where do I find computer fraud and abuse?
With pdfFiller, an all-in-one online tool for professional document management, it's easy to fill out documents. Over 25 million fillable forms are available on our website, and you can find the computer fraud and abuse in a matter of seconds. Open it right away and start making it your own with help from advanced editing tools.
How do I complete computer fraud and abuse online?
Easy online computer fraud and abuse completion using pdfFiller. Also, it allows you to legally eSign your form and change original PDF material. Create a free account and manage documents online.
How do I edit computer fraud and abuse in Chrome?
Install the pdfFiller Chrome Extension to modify, fill out, and eSign your computer fraud and abuse, which you can access right from a Google search page. Fillable documents without leaving Chrome on any internet-connected device.
What is computer fraud and abuse?
Computer fraud and abuse involves unauthorized access to computer systems or networks for fraudulent purposes.
Who is required to file computer fraud and abuse?
Individuals or organizations that have experienced computer fraud and abuse are required to file a report.
How to fill out computer fraud and abuse?
To fill out a report on computer fraud and abuse, one must provide detailed information about the incident, including date, time, and type of fraud.
What is the purpose of computer fraud and abuse?
The purpose of computer fraud and abuse is to inform authorities about criminal activities involving unauthorized access to computer systems.
What information must be reported on computer fraud and abuse?
Information such as the type of fraud, impact on the victim, and any evidence related to the incident must be reported.
Fill out your computer fraud and abuse online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Computer Fraud And Abuse is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.