Get the free breach was and that the warrant of removal can then be executed upon, as permitted b...
Show details
SavePrintClearConsent to Enter Judgment (Tenant Vacates)
Superior Court of New Jersey
Law Division, Special Civil Part
County
LandlordTenant Division
Docket Number Consent to Enter JudgmentPlaintiff
v.
Defendant(Tenant
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign breach was and that
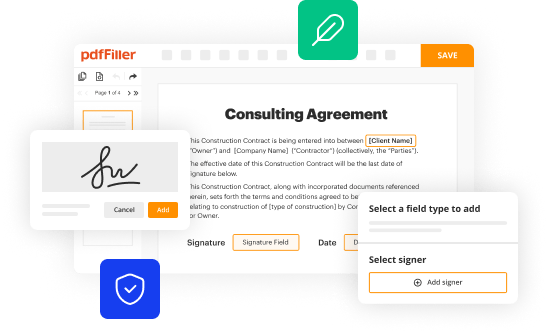
Edit your breach was and that form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your breach was and that form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit breach was and that online
Follow the guidelines below to use a professional PDF editor:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit breach was and that. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
pdfFiller makes working with documents easier than you could ever imagine. Register for an account and see for yourself!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out breach was and that
How to fill out breach was and that
01
To fill out breach was and that, follow these steps:
02
Start by gathering all the necessary information related to the breach, such as the date and time of the breach, the affected parties, the nature of the breach, and any supporting evidence.
03
Clearly explain the details of the breach in a factual and unbiased manner, avoiding any personal opinions or subjective language.
04
Provide any relevant background information regarding the system or process that was breached, including its purpose, security measures in place, and any prior incidents.
05
Use a structured format to present the breach information, such as bullet points or numbered lists, to ensure clarity and easy comprehension.
06
Include any actions taken in response to the breach, such as notifying the affected parties, contacting legal authorities, or implementing new security measures.
07
Conclude the breach was and that with a summary of the overall impact and implications of the breach, considering both immediate and long-term consequences.
08
Proofread the document to ensure accuracy, coherence, and adherence to any legal or regulatory requirements.
09
If necessary, seek legal advice or consult with internal stakeholders before finalizing and distributing the breach was and that.
10
Store a copy of the breach was and that securely for future reference and compliance purposes.
Who needs breach was and that?
01
Breach was and that is needed by:
02
- Organizations that have experienced a security breach, whether it involves data breaches, cyber attacks, or any other unauthorized access to sensitive information.
03
- Legal and compliance departments within organizations that are responsible for documenting and reporting security breaches to relevant parties or governing bodies.
04
- Data protection and IT security professionals who need to assess and investigate security incidents, analyze breach patterns, and implement preventive measures.
05
- Business executives and board members who require a comprehensive understanding of security breaches to make informed decisions regarding risk management, resource allocation, and organizational strategies.
06
- External stakeholders, such as customers, partners, or investors, who have a vested interest in knowing about security breaches that may affect them or the organization's operations.
07
- Regulatory authorities and industry regulators who oversee compliance with security standards and may require organizations to submit breach was and that as part of their obligations.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I modify breach was and that without leaving Google Drive?
Using pdfFiller with Google Docs allows you to create, amend, and sign documents straight from your Google Drive. The add-on turns your breach was and that into a dynamic fillable form that you can manage and eSign from anywhere.
Can I sign the breach was and that electronically in Chrome?
Yes. With pdfFiller for Chrome, you can eSign documents and utilize the PDF editor all in one spot. Create a legally enforceable eSignature by sketching, typing, or uploading a handwritten signature image. You may eSign your breach was and that in seconds.
How do I edit breach was and that straight from my smartphone?
The pdfFiller apps for iOS and Android smartphones are available in the Apple Store and Google Play Store. You may also get the program at https://edit-pdf-ios-android.pdffiller.com/. Open the web app, sign in, and start editing breach was and that.
What is breach was and that?
A breach is an instance where a law, obligation, or duty is violated. In the context of regulations, it typically refers to a failure to comply with set guidelines or disclosure requirements.
Who is required to file breach was and that?
Organizations or individuals who are subject to regulatory requirements and have experienced a breach involving sensitive information or failing to meet compliance standards are required to file a breach report.
How to fill out breach was and that?
To fill out a breach report, you need to gather all relevant information about the breach, including the nature of the breach, data involved, number of individuals affected, and the steps taken to address the breach, and submit it according to the specific guidelines provided by the regulatory authority.
What is the purpose of breach was and that?
The purpose of filing a breach report is to inform regulatory bodies about the violation and to ensure that appropriate measures are taken to mitigate the impact of the breach and protect affected individuals.
What information must be reported on breach was and that?
The information that must be reported includes details about the breach, such as date and time of the incident, types of data compromised, affected individuals, and the measures taken to rectify the breach.
Fill out your breach was and that online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Breach Was And That is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















