
Get the free Breaching vs - blogs nwifc
Show details
Accounting Tracking System (FEATS). Photo by Rebecca ... Email: food skagitcoop.org. 5a. Program .... The PSP Biennial Work Plan 2009-2011, The Habitat Monitoring Strategy for the Tidal Skagit Delta.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign breaching vs - blogs
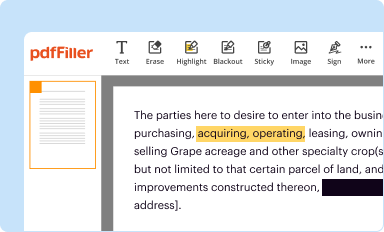
Edit your breaching vs - blogs form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
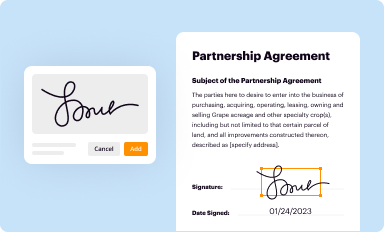
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
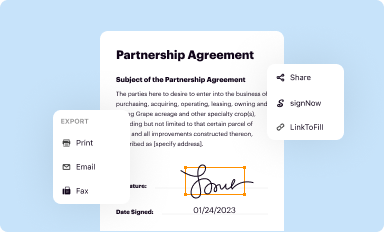
Share your form instantly
Email, fax, or share your breaching vs - blogs form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit breaching vs - blogs online
Follow the steps down below to use a professional PDF editor:
1
Sign into your account. It's time to start your free trial.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit breaching vs - blogs. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out breaching vs - blogs
How to fill out breaching vs - blogs:
01
Firstly, it is important to understand the concept of breaching vs blogs. Breaching refers to actions or events that violate a set of rules or norms, while blogs are online platforms where individuals or organizations can share their thoughts, opinions, or information. To fill out breaching vs - blogs, you need to analyze and compare these two concepts.
02
Identify the purpose of your analysis. Before filling out breaching vs - blogs, determine why you need this information. Are you conducting research, writing an essay, or seeking to understand the implications of certain actions? This will help you structure your analysis effectively and ensure you address the relevant aspects.
03
Gather information on breaching. Familiarize yourself with different forms of breaching, such as social, legal, or cultural breaches. Explore examples and case studies to grasp the different ways in which breaching can occur. Understanding breaching will provide you with a foundation to compare it with the concept of blogs.
04
Research blogs and their characteristics. Study the various types of blogs available, such as personal blogs, professional blogs, or corporate blogs. Understand their purpose, audience, and the potential benefits they provide. This will help you distinguish between breaching and blogs and identify their unique attributes.
05
Compare and contrast the characteristics. Make a list or a table of the characteristics of breaching and blogs. This can include aspects such as intent, impact, legality, online presence, and consequences. Analyze the differences between breaching and blogs and highlight their key distinctions.
06
Assess the importance and relevance of breaching vs blogs. Consider the implications of breaching and blogs in different contexts. Think about individuals or groups who may be affected by breaches or benefit from blogs. Understanding the significance of each concept will help you determine who needs to be aware of breaching vs blogs.
Who needs breaching vs - blogs?
01
Researchers: Scholars, sociologists, or psychologists studying human behavior, societies, or online platforms may find the analysis of breaching vs blogs relevant. It can provide insights into the factors that drive breaching behavior or the impact of blogs on communities.
02
Content creators or bloggers: Individuals who are engaged in blogging or content creation may benefit from understanding the difference between breaching and blogs. This knowledge can help them ensure their content adheres to acceptable norms and avoid potentially breaching ethical, legal, or cultural boundaries.
03
Policymakers or regulators: Government officials, policymakers, or those responsible for developing regulations may require a comprehensive understanding of breaching vs blogs. This knowledge can assist in creating laws or guidelines that address the risks associated with breaching and ensure the promotion of responsible blogging.
In conclusion, filling out breaching vs - blogs requires a thorough analysis of both concepts, their characteristics, and a consideration of the relevant audience. Researchers, content creators, and policymakers are among those who may benefit from understanding and studying breaching vs blogs.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send breaching vs - blogs for eSignature?
breaching vs - blogs is ready when you're ready to send it out. With pdfFiller, you can send it out securely and get signatures in just a few clicks. PDFs can be sent to you by email, text message, fax, USPS mail, or notarized on your account. You can do this right from your account. Become a member right now and try it out for yourself!
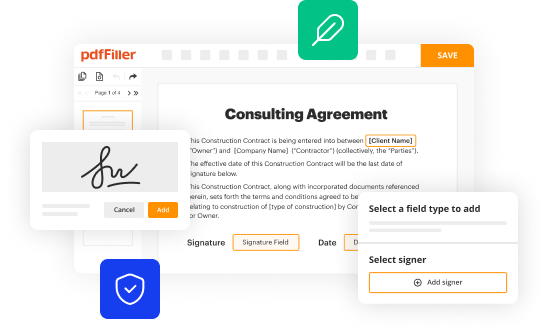
How do I edit breaching vs - blogs online?
pdfFiller not only allows you to edit the content of your files but fully rearrange them by changing the number and sequence of pages. Upload your breaching vs - blogs to the editor and make any required adjustments in a couple of clicks. The editor enables you to blackout, type, and erase text in PDFs, add images, sticky notes and text boxes, and much more.
Can I edit breaching vs - blogs on an iOS device?
Create, edit, and share breaching vs - blogs from your iOS smartphone with the pdfFiller mobile app. Installing it from the Apple Store takes only a few seconds. You may take advantage of a free trial and select a subscription that meets your needs.
What is breaching vs - blogs?
Breaching vs - blogs refers to a comparison between two different types of security breaches reported on blogs.
Who is required to file breaching vs - blogs?
Any organization or individual who experiences a security breach and writes about it on a blog is required to file breaching vs - blogs.
How to fill out breaching vs - blogs?
To fill out breaching vs - blogs, one must document the details of the security breach, the impact it had, any action taken to address it, and lessons learned from the incident.
What is the purpose of breaching vs - blogs?
The purpose of breaching vs - blogs is to provide transparency about security incidents, share knowledge to prevent future breaches, and learn from past mistakes.
What information must be reported on breaching vs - blogs?
Information such as the nature of the breach, the systems affected, the vulnerabilities exploited, the timeline of events, and the response to the incident must be reported on breaching vs - blogs.
Fill out your breaching vs - blogs online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Breaching Vs - Blogs is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















