Get the free How to Extract Encrypted RAR File with or without Password
Show details
Continuer password remover
By Andrew Todd Updated September 15, 2017, RAR File Compressed File And Folders. RAR files make it easy for users to reduce the size of files and folders. RAR files can
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign how to extract encrypted

Edit your how to extract encrypted form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your how to extract encrypted form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit how to extract encrypted online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Log in to your account. Start Free Trial and sign up a profile if you don't have one.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit how to extract encrypted. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
It's easier to work with documents with pdfFiller than you could have believed. Sign up for a free account to view.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
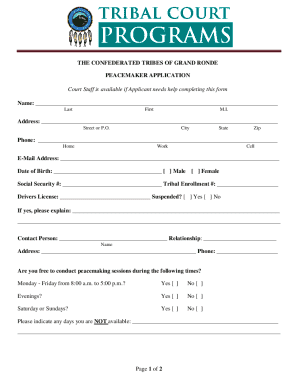
How to fill out how to extract encrypted

How to fill out how to extract encrypted
01
To fill out how to extract encrypted, follow these steps:
02
Step 1: Obtain the encrypted data that you want to extract. This can be in the form of a file or a text string.
03
Step 2: Identify the encryption algorithm used to encrypt the data. Common algorithms include AES, RSA, and DES.
04
Step 3: Determine the key or password required to decrypt the encrypted data. This is crucial for successful extraction.
05
Step 4: Use a suitable decryption tool or programming library that supports the encryption algorithm and key/password.
06
Step 5: Implement the decryption process using the chosen tool or library, following the provided documentation or guidelines.
07
Step 6: Apply the decryption algorithm and provide the necessary key/password when prompted.
08
Step 7: Once the decryption process is completed, you should obtain the extracted data in its original form.
09
Step 8: Validate the extracted data to ensure its integrity and accuracy.
10
Step 9: Store or use the extracted data as required.
11
Note: It is important to have the necessary permissions and legal rights to extract encrypted data. Always follow applicable laws and regulations.
Who needs how to extract encrypted?
01
Various individuals or entities might need to extract encrypted data, including:
02
- Cybersecurity professionals who are investigating security incidents or conducting forensic analysis.
03
- Law enforcement agencies that require access to encrypted data for criminal investigations.
04
- Researchers who are studying encryption algorithms and techniques.
05
- System administrators who may need to troubleshoot or recover encrypted data.
06
- Software developers who are working on implementing encryption or decryption functionalities.
07
- Individuals who have encrypted files but have forgotten the encryption key/password and need to recover their data.
08
Overall, anyone who encounters encrypted data and has a legitimate reason to access the underlying information may need to extract encrypted data.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I edit how to extract encrypted from Google Drive?
It is possible to significantly enhance your document management and form preparation by combining pdfFiller with Google Docs. This will allow you to generate papers, amend them, and sign them straight from your Google Drive. Use the add-on to convert your how to extract encrypted into a dynamic fillable form that can be managed and signed using any internet-connected device.
How can I send how to extract encrypted to be eSigned by others?
Once you are ready to share your how to extract encrypted, you can easily send it to others and get the eSigned document back just as quickly. Share your PDF by email, fax, text message, or USPS mail, or notarize it online. You can do all of this without ever leaving your account.
How do I edit how to extract encrypted on an iOS device?
Create, modify, and share how to extract encrypted using the pdfFiller iOS app. Easy to install from the Apple Store. You may sign up for a free trial and then purchase a membership.
What is how to extract encrypted?
How to extract encrypted refers to the methods or processes used to retrieve data that has been secured by encryption, ensuring that only authorized users can access the original content.
Who is required to file how to extract encrypted?
Individuals or entities that handle encrypted data and need to report or document their encryption processes and security measures are often required to file how to extract encrypted.
How to fill out how to extract encrypted?
Filling out how to extract encrypted typically involves providing necessary details regarding the encryption methods used, the types of data encrypted, and any relevant access procedures.
What is the purpose of how to extract encrypted?
The purpose of how to extract encrypted is to provide a framework for securely retrieving encrypted data while ensuring compliance with legal and regulatory standards.
What information must be reported on how to extract encrypted?
Information that must be reported includes the encryption algorithms used, data categories, access controls, and any incidents of unauthorized access.
Fill out your how to extract encrypted online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

How To Extract Encrypted is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.