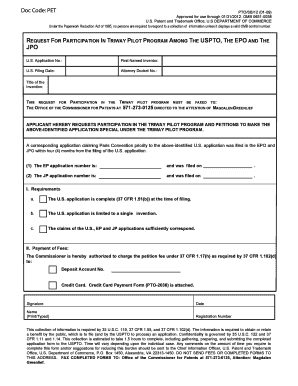
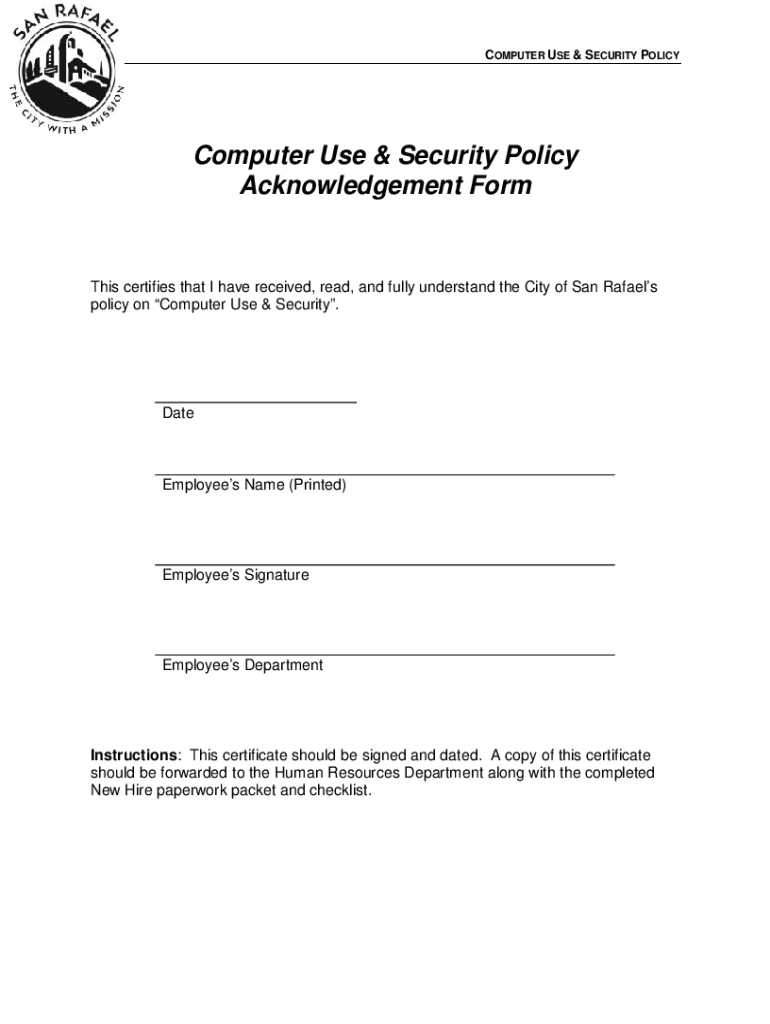
Get the free Computer Use & Security Policy Acknowledgement Form
Show details
COMPUTER USE & SECURITY POLICYComputer Use & Security Policy Acknowledgement Forms certifies that I have received, read, and fully understand the City of San Rafael's policy on Computer Use & Security.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign computer use amp security
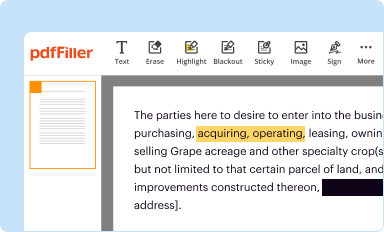
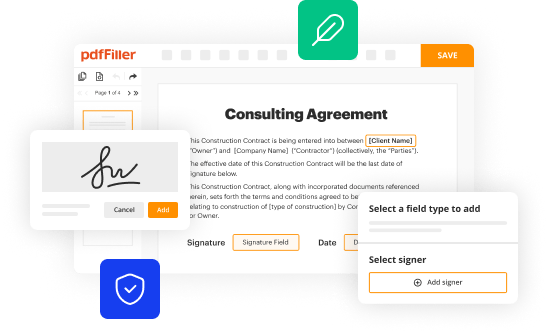
Edit your computer use amp security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
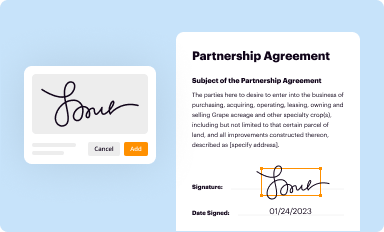
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
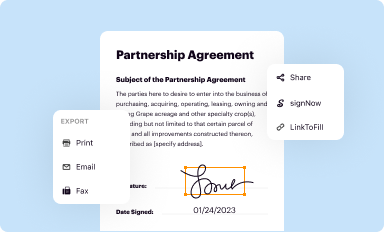
Share your form instantly
Email, fax, or share your computer use amp security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit computer use amp security online
Use the instructions below to start using our professional PDF editor:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit computer use amp security. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
With pdfFiller, it's always easy to work with documents. Try it!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out computer use amp security
How to fill out computer use amp security
01
To fill out computer use amp security, follow these steps:
02
Start by ensuring that you have a reliable antivirus software installed on your computer. This will help protect against malware and other security threats.
03
Keep your operating system and all software up to date. Software updates often include important security patches that can help protect your computer.
04
Create strong and unique passwords for all your accounts. Avoid using easily guessable passwords and consider using a password manager to keep track of them.
05
Enable a firewall on your computer to add an extra layer of protection. This will help block unauthorized access to your system.
06
Be cautious when clicking on links or downloading files from unknown sources. These could contain malware or other security threats.
07
Regularly backup your important files and data. This will help protect against data loss in case of a security breach or system failure.
08
Educate yourself about common computer security threats and how to recognize them. This will make you better equipped to protect your computer and avoid falling victim to scams or attacks.
09
Use a virtual private network (VPN) when accessing the internet, especially on public Wi-Fi networks. A VPN will encrypt your internet connection and help protect your privacy.
10
By following these steps, you can ensure that your computer use amp security is effectively maintained.
Who needs computer use amp security?
01
Computer use amp security is important for anyone who uses a computer or connected devices. This includes individuals, businesses, and organizations of all sizes.
02
In today's digital age, computers are involved in almost every aspect of our daily lives, from personal communication and banking to sensitive business operations and government activities.
03
Without proper security measures, computers can be vulnerable to cyberattacks, data breaches, identity theft, and other malicious activities.
04
By implementing computer use amp security practices, individuals and organizations can greatly reduce the risk of these security threats and protect their sensitive information and digital assets.
05
Whether you are a home user, a small business owner, or part of a large organization, computer use amp security should be a top priority to safeguard your digital presence.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send computer use amp security to be eSigned by others?
When your computer use amp security is finished, send it to recipients securely and gather eSignatures with pdfFiller. You may email, text, fax, mail, or notarize a PDF straight from your account. Create an account today to test it.
How do I make changes in computer use amp security?
With pdfFiller, you may not only alter the content but also rearrange the pages. Upload your computer use amp security and modify it with a few clicks. The editor lets you add photos, sticky notes, text boxes, and more to PDFs.
How do I fill out computer use amp security on an Android device?
Use the pdfFiller Android app to finish your computer use amp security and other documents on your Android phone. The app has all the features you need to manage your documents, like editing content, eSigning, annotating, sharing files, and more. At any time, as long as there is an internet connection.
What is computer use amp security?
Computer use and security refers to the practices and protocols used to protect computer systems and networks from unauthorized access, data breaches, and other cybersecurity threats.
Who is required to file computer use amp security?
Entities such as businesses, organizations, and individuals who handle or process sensitive information are typically required to file for computer use and security compliance.
How to fill out computer use amp security?
To fill out the computer use and security, one needs to provide details about the systems in use, security measures implemented, and any incidents of data breaches or vulnerabilities.
What is the purpose of computer use amp security?
The purpose of computer use and security is to safeguard sensitive information, ensure data integrity, and maintain confidentiality in computer systems.
What information must be reported on computer use amp security?
Information that must be reported includes details about data practices, security protocols in place, incident reports, and compliance with relevant laws and regulations.
Fill out your computer use amp security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Computer Use Amp Security is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.