Get the free A Privilege Management Scheme for Mobile Agent Systems - csrc nist
Show details
A Privilege Management Scheme for Mobile Agent Systems W. A. Jansen National Institute of Standards and Technology 100 Bureau Dr., STOP 8930 Gaithersburg, MD 20899 (+1) (301) 975 5148 Jansen NIST.gov
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign a privilege management scheme

Edit your a privilege management scheme form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your a privilege management scheme form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit a privilege management scheme online
To use the professional PDF editor, follow these steps:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit a privilege management scheme. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
With pdfFiller, dealing with documents is always straightforward.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out a privilege management scheme

To fill out a privilege management scheme, you can follow these steps:
01
Identify the roles and responsibilities within your organization: Determine the different roles and the specific privileges and access levels required for each role.
02
Conduct a risk assessment: Evaluate the potential risks and consequences associated with granting certain privileges. Consider the potential impact on data security, confidentiality, and compliance.
03
Establish a hierarchy of access levels: Define different levels of access based on the roles within your organization. This may include privileges such as read-only access, write access, and administrative access.
04
Implement the principle of least privilege: Grant users the minimum privileges necessary to perform their tasks. Avoid assigning excessive privileges that are not required to minimize the risk of unauthorized access or misuse.
05
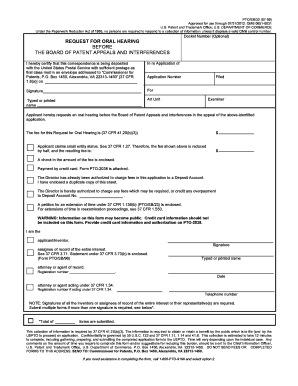
Create a process for requesting and granting privileges: Establish a formal process for users to request additional privileges. This may involve submitting a request form, undergoing approval from designated authorities, and periodically reviewing and updating access levels.
06
Document privileges and access control policies: Keep a record of the privileges granted to each user and maintain a comprehensive document outlining the access control policies in place. This documentation will help ensure transparency, accountability, and facilitate audits.
07
Regularly review and update the privilege management scheme: Conduct periodic reviews of the privilege management scheme to ensure it remains aligned with organizational needs and industry best practices. Update the scheme as required based on changes in roles, responsibilities, or technology.
Who needs a privilege management scheme?
01
Organizations with sensitive data: Companies that handle sensitive data, such as financial institutions, healthcare providers, or government agencies, often require a privilege management scheme to safeguard their information.
02
Enterprises with multiple user roles: Organizations with a diverse workforce and various user roles can benefit from a privilege management scheme to efficiently manage access levels and ensure appropriate privileges are assigned.
03
Businesses focused on compliance: Industries with strict regulatory requirements, such as financial services or healthcare, need to maintain a privilege management scheme to demonstrate compliance with industry regulations and protect customer data.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I edit a privilege management scheme in Chrome?
Download and install the pdfFiller Google Chrome Extension to your browser to edit, fill out, and eSign your a privilege management scheme, which you can open in the editor with a single click from a Google search page. Fillable documents may be executed from any internet-connected device without leaving Chrome.
How do I edit a privilege management scheme on an iOS device?
Use the pdfFiller mobile app to create, edit, and share a privilege management scheme from your iOS device. Install it from the Apple Store in seconds. You can benefit from a free trial and choose a subscription that suits your needs.
How do I complete a privilege management scheme on an Android device?
Use the pdfFiller app for Android to finish your a privilege management scheme. The application lets you do all the things you need to do with documents, like add, edit, and remove text, sign, annotate, and more. There is nothing else you need except your smartphone and an internet connection to do this.
What is a privilege management scheme?
A privilege management scheme is a set of policies and procedures implemented by an organization to effectively manage and control access to privileged resources or information within the organization.
Who is required to file a privilege management scheme?
The requirement to file a privilege management scheme varies depending on the specific legal and regulatory requirements of each jurisdiction or organization. Generally, organizations that handle sensitive or confidential information, such as government agencies or financial institutions, are required to have and file a privilege management scheme.
How to fill out a privilege management scheme?
Filling out a privilege management scheme typically involves documenting the policies, procedures, and controls that will be implemented to manage and control access to privileged resources or information. This may include identifying and categorizing privilege levels, specifying access control mechanisms, defining user roles and responsibilities, and outlining auditing and monitoring procedures.
What is the purpose of a privilege management scheme?
The purpose of a privilege management scheme is to ensure that access to privileged resources or information is appropriately controlled and managed within an organization. It helps prevent unauthorized access or misuse of sensitive data and reduces the risk of security breaches and insider threats.
What information must be reported on a privilege management scheme?
The specific information required to be reported on a privilege management scheme may vary depending on the legal and regulatory requirements of each jurisdiction or organization. However, it typically includes details of the privilege hierarchy, access control mechanisms, user roles and responsibilities, auditing and monitoring procedures, and any relevant security controls.
Fill out your a privilege management scheme online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

A Privilege Management Scheme is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.