Get the free Achieving Efficient Access to Large Integrated Sets of Semantic Data ... - icwe2008 ...
Show details
Eighth International Conference on Web Engineering Achieving Efficient Access to Large Integrated Sets of Semantic Data in Web Applications Peter Bellekens1, Keep van der Sluijs1, William van Woensel2,
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign achieving efficient access to

Edit your achieving efficient access to form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your achieving efficient access to form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit achieving efficient access to online
To use our professional PDF editor, follow these steps:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit achieving efficient access to. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
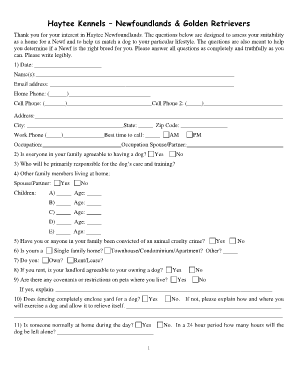
How to fill out achieving efficient access to

01
The first step in achieving efficient access to is identifying the specific resources or information that need to be accessed. This could include databases, files, websites, or any other relevant sources that play a crucial role in achieving goals or completing tasks efficiently.
02
Once the resources are identified, it is important to assess the level of access required. Determine whether read-only access is sufficient or if read-write privileges are necessary. This evaluation will help in establishing appropriate user permissions and security measures.
03
Implementing a robust access control system is key to achieving efficient access. This involves setting up authentication methods, such as passwords, biometrics, or multi-factor authentication, to verify the identity of users. Additionally, establishing user roles and groups can help streamline access based on job functions or responsibilities.
04
Establish clear policies and guidelines for accessing and managing resources. This includes outlining procedures for requesting access, granting or revoking access, and regularly reviewing user privileges. Clear documentation and communication ensure that access to resources remains efficient and aligned with organizational goals.
05
Regularly monitor and analyze access patterns and usage. This entails implementing monitoring tools and logging mechanisms to track who accesses what resources and when. Analyzing this data can help identify any inefficiencies, bottlenecks, or security concerns and allow for optimizations to be made.
06
Training and education are crucial for users to understand the importance of achieving efficient access and to learn best practices for accessing and managing resources. Provide training sessions or workshops to familiarize users with the access control system, user responsibilities, and the consequences of misuse or mishandling of access.
Who needs achieving efficient access to?
01
Organizations and businesses that deal with sensitive data or proprietary information need to achieve efficient access to safeguard their assets and maintain compliance with data protection regulations.
02
Professionals, such as project managers, researchers, or analysts, who require access to critical resources to perform their jobs effectively and make informed decisions.
03
Collaborative teams or departments within an organization that rely heavily on shared resources and need efficient access to enhance productivity and streamline workflows.
04
Information technology departments or system administrators who are responsible for managing access control systems and ensuring that users have the appropriate permissions to perform their tasks efficiently.
05
Individuals seeking personal productivity and ease of access to their own resources, such as personal files, email accounts, or digital assets.
In summary, achieving efficient access to involves a systematic approach to identify and manage resources effectively. This benefits various entities, including organizations, professionals, teams, system administrators, and individuals.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is achieving efficient access to?
Achieving efficient access refers to improving the ability to efficiently access certain resources or information.
Who is required to file achieving efficient access to?
The specific individuals or organizations required to file achieving efficient access reports may vary depending on the context and purpose of the access.
How to fill out achieving efficient access to?
The process for filling out achieving efficient access reports may vary depending on the requirements set by the governing body or organization.
What is the purpose of achieving efficient access to?
The purpose of achieving efficient access is to enhance productivity, streamline processes, and improve overall effectiveness in accessing and utilizing certain resources or information.
What information must be reported on achieving efficient access to?
The specific information to be reported on achieving efficient access reports may vary depending on the context and requirements of the access.
How can I modify achieving efficient access to without leaving Google Drive?
By integrating pdfFiller with Google Docs, you can streamline your document workflows and produce fillable forms that can be stored directly in Google Drive. Using the connection, you will be able to create, change, and eSign documents, including achieving efficient access to, all without having to leave Google Drive. Add pdfFiller's features to Google Drive and you'll be able to handle your documents more effectively from any device with an internet connection.
How do I complete achieving efficient access to online?
pdfFiller has made it simple to fill out and eSign achieving efficient access to. The application has capabilities that allow you to modify and rearrange PDF content, add fillable fields, and eSign the document. Begin a free trial to discover all of the features of pdfFiller, the best document editing solution.
Can I edit achieving efficient access to on an Android device?
You can. With the pdfFiller Android app, you can edit, sign, and distribute achieving efficient access to from anywhere with an internet connection. Take use of the app's mobile capabilities.
Fill out your achieving efficient access to online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Achieving Efficient Access To is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.