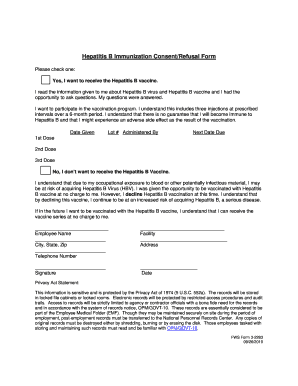
What is Ination security management: A case study of an ... Form?
The Ination security management: A case study of an ... is a fillable form in MS Word extension required to be submitted to the required address in order to provide some information. It must be filled-out and signed, which can be done in hard copy, or via a particular solution such as PDFfiller. It helps to fill out any PDF or Word document right in the web, customize it according to your needs and put a legally-binding e-signature. Right after completion, the user can send the Ination security management: A case study of an ... to the appropriate receiver, or multiple ones via email or fax. The template is printable as well due to PDFfiller feature and options offered for printing out adjustment. In both digital and physical appearance, your form should have a clean and professional outlook. Also you can save it as the template to use it later, so you don't need to create a new document again. All that needed is to amend the ready sample.
Template Ination security management: A case study of an ... instructions
When you are ready to begin completing the Ination security management: A case study of an ... form, it is important to make certain all required information is prepared. This very part is important, as far as errors can result in unpleasant consequences. It is always annoying and time-consuming to resubmit forcedly entire word form, not speaking about penalties resulted from missed due dates. Handling the figures requires a lot of focus. At first glimpse, there’s nothing tricky about this. However, there's no anything challenging to make a typo. Professionals advise to store all sensitive data and get it separately in a document. When you've got a writable sample, you can just export it from the document. Anyway, all efforts should be made to provide true and correct data. Doublecheck the information in your Ination security management: A case study of an ... form when filling out all important fields. You are free to use the editing tool in order to correct all mistakes if there remains any.
How should you fill out the Ination security management: A case study of an ... template
In order to start completing the form Ination security management: A case study of an ..., you'll need a writable template. When using PDFfiller for completion and submitting, you may get it in several ways:
- Look for the Ination security management: A case study of an ... form in PDFfiller’s library.
- You can also upload the template with your device in Word or PDF format.
- Finally, you can create a document all by yourself in PDFfiller’s creator tool adding all necessary object via editor.
Whatever choise you make, you will get all features you need under your belt. The difference is, the Word form from the archive contains the required fillable fields, and in the rest two options, you will have to add them yourself. Yet, this action is dead simple thing and makes your template really convenient to fill out. These fields can be placed on the pages, you can remove them too. There are different types of these fields based on their functions, whether you’re entering text, date, or place checkmarks. There is also a signing field if you want the word file to be signed by others. You are able to sign it yourself with the help of the signing tool. When you're done, all you need to do is press Done and move to the submission of the form.