Get the free Leader in Cyber Security Solutions Check Point Software
Show details
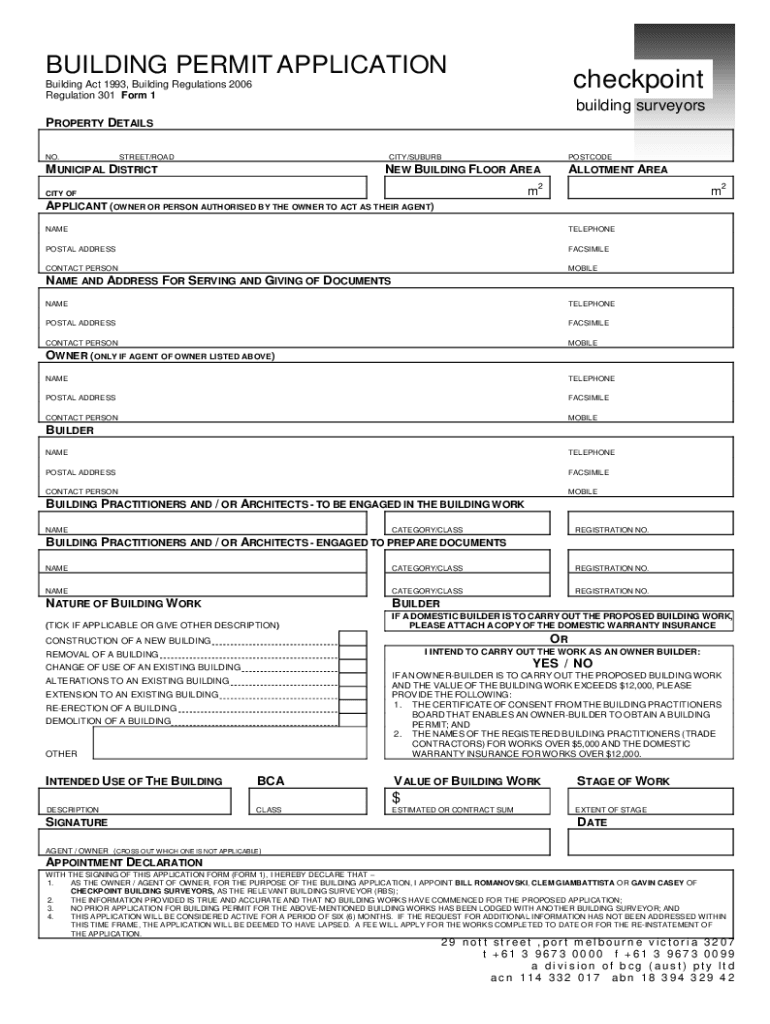
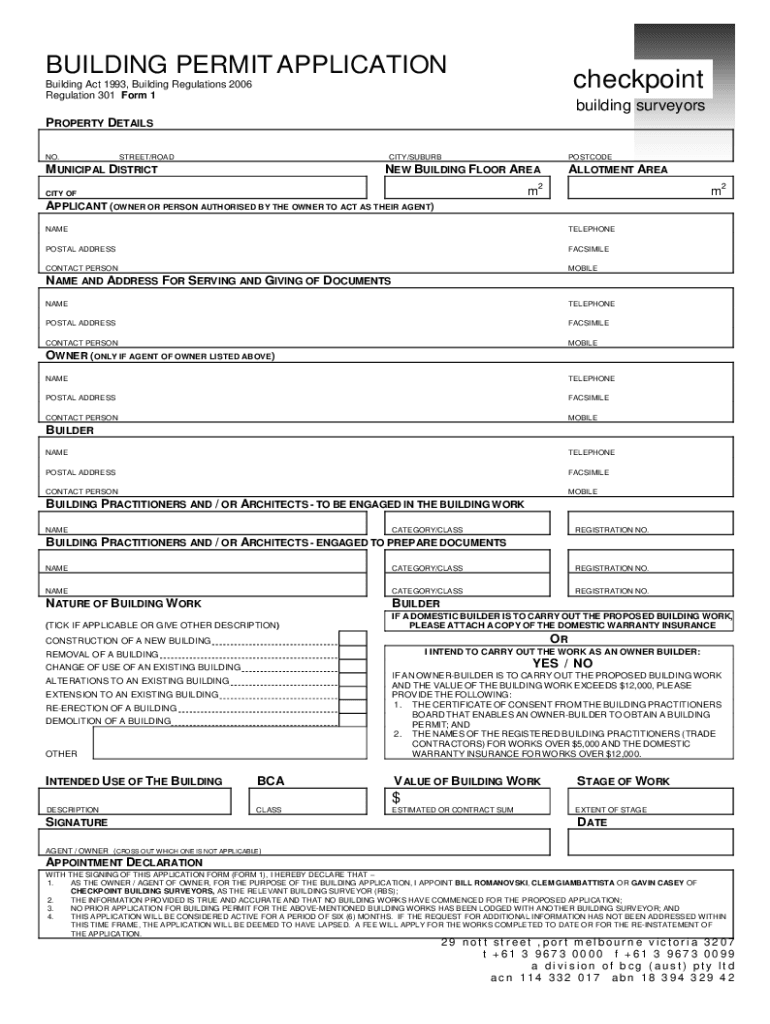
BUILDING PERMIT APPLICATIONcheckpointBuilding Act 1993, Building Regulations 2006
Regulation 301 Form 1building surveyorsPROPERTY DETAILS
NO.STREET/ROADCITY/SUBURBMUNICIPAL DISTRICTPOSTCODENEW BUILDING
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign leader in cyber security

Edit your leader in cyber security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your leader in cyber security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit leader in cyber security online
To use our professional PDF editor, follow these steps:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit leader in cyber security. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
pdfFiller makes working with documents easier than you could ever imagine. Try it for yourself by creating an account!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out leader in cyber security

How to fill out leader in cyber security
01
Start by conducting a thorough assessment of your organization's current cybersecurity infrastructure and policies.
02
Identify the specific skills and qualifications required for a leader in cybersecurity, such as knowledge of various security frameworks, risk management strategies, and incident response protocols.
03
Develop a comprehensive job description outlining the responsibilities and expectations of the cyber security leader role.
04
Advertise the position through appropriate channels, such as online job boards and cybersecurity professional networks.
05
Screen and interview potential candidates, focusing on their technical expertise, leadership abilities, and problem-solving skills.
06
Once a suitable candidate is identified, conduct background checks and reference checks to validate their qualifications and experience.
07
Offer the selected candidate a competitive compensation package, taking into consideration market rates for cybersecurity leadership roles.
08
Provide the necessary resources and support to enable the cyber security leader to effectively carry out their responsibilities.
09
Continuously evaluate and assess the performance of the cyber security leader, providing regular feedback and opportunities for professional development.
10
Stay updated on emerging cyber threats and trends in the cybersecurity landscape, ensuring that the leader in cyber security remains equipped to protect the organization.
Who needs leader in cyber security?
01
Any organization that values its sensitive data, intellectual property, and customer information needs a leader in cyber security.
02
This includes but is not limited to:
03
- Government agencies
04
- Financial institutions
05
- Healthcare organizations
06
- Technology companies
07
- Educational institutions
08
- Retail and e-commerce companies
09
- Manufacturing and industrial organizations
10
Essentially, any entity that deals with digital information and faces the risk of cyber attacks and data breaches requires a leader in cyber security to ensure the confidentiality, integrity, and availability of their systems and data.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I modify leader in cyber security without leaving Google Drive?
You can quickly improve your document management and form preparation by integrating pdfFiller with Google Docs so that you can create, edit and sign documents directly from your Google Drive. The add-on enables you to transform your leader in cyber security into a dynamic fillable form that you can manage and eSign from any internet-connected device.
How do I make edits in leader in cyber security without leaving Chrome?
leader in cyber security can be edited, filled out, and signed with the pdfFiller Google Chrome Extension. You can open the editor right from a Google search page with just one click. Fillable documents can be done on any web-connected device without leaving Chrome.
How do I complete leader in cyber security on an iOS device?
Install the pdfFiller iOS app. Log in or create an account to access the solution's editing features. Open your leader in cyber security by uploading it from your device or online storage. After filling in all relevant fields and eSigning if required, you may save or distribute the document.
What is leader in cyber security?
A leader in cyber security refers to an individual or organization that plays a critical role in developing strategies, policies, and practices to protect digital assets and information systems from cyber threats.
Who is required to file leader in cyber security?
Organizations that handle sensitive information and engage in cyber security practices are often required to file leader in cyber security reports, which may include companies in finance, healthcare, and critical infrastructure sectors.
How to fill out leader in cyber security?
Filling out a leader in cyber security typically involves collecting relevant data about cyber security measures, reporting incidents, and demonstrating compliance with established cybersecurity frameworks and regulations.
What is the purpose of leader in cyber security?
The purpose of a leader in cyber security is to enhance the overall security posture of an organization, reduce vulnerabilities, and ensure a proactive approach to managing potential cyber threats.
What information must be reported on leader in cyber security?
Organizations must report information such as incidents of data breaches, security measures implemented, employee training programs, and compliance with regulatory requirements in their leader in cyber security filings.
Fill out your leader in cyber security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Leader In Cyber Security is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.