Get the free Computer Security Incident Handling Guide - NIST Technical ...
Show details
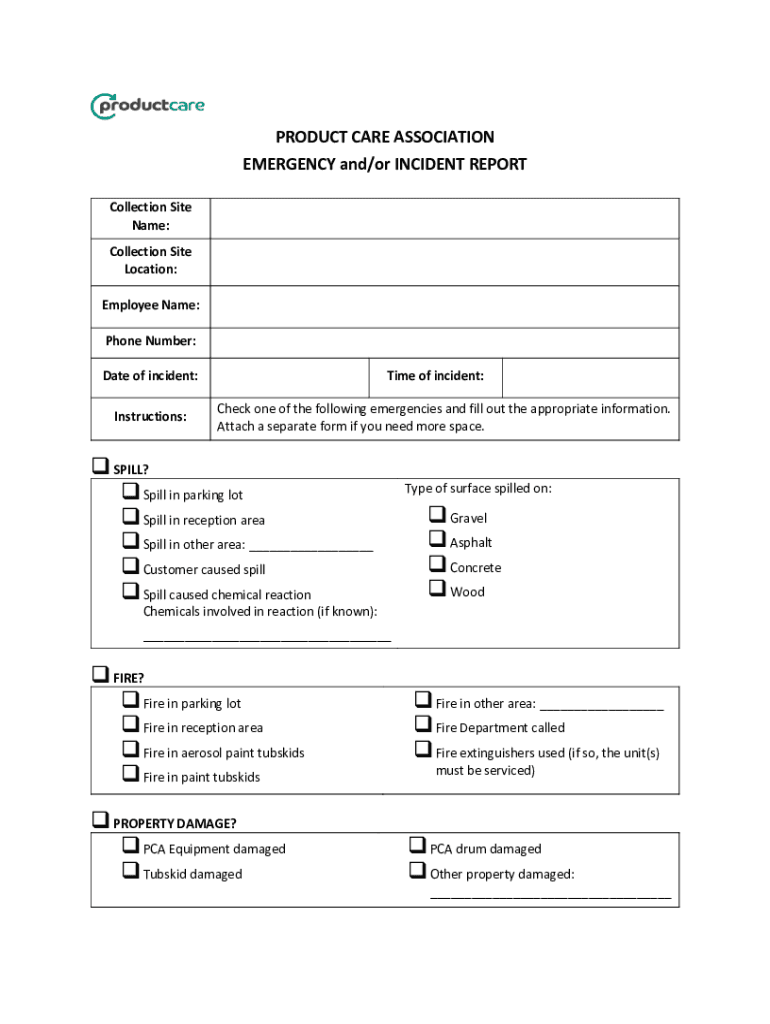
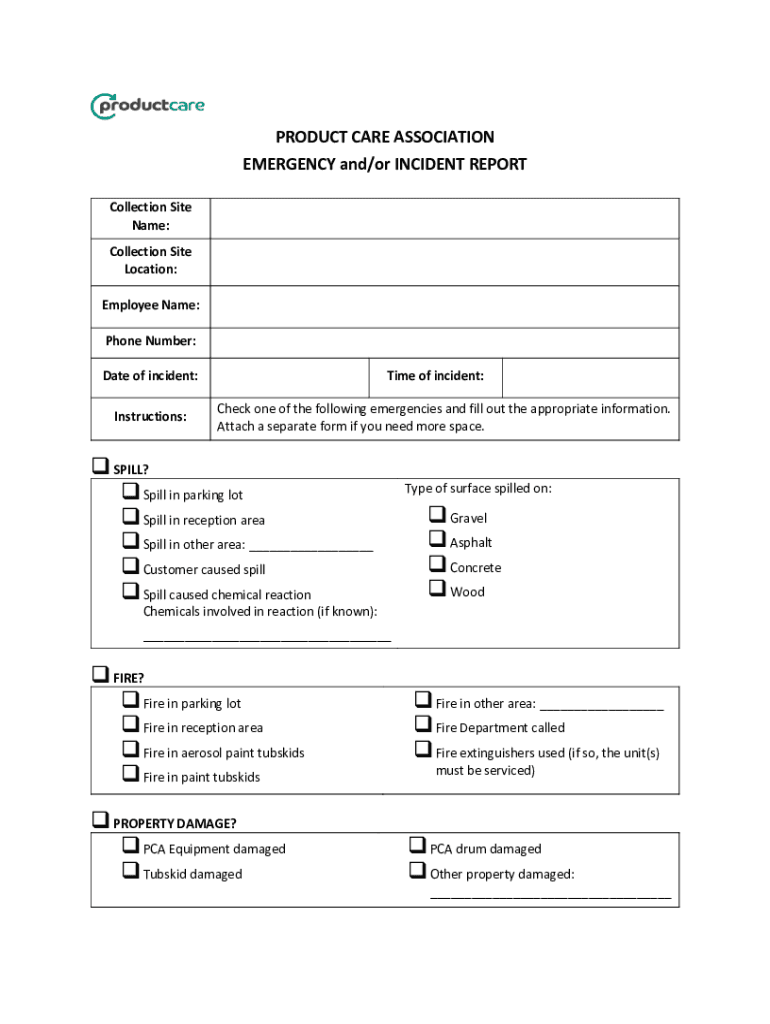
PRODUCT CARE ASSOCIATION EMERGENCY and/or INCIDENT REPORT Collection Site Name: Collection Site Location: Employee Name: Phone Number: Date of incident: Instructions:Time of incident: Check one of
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign computer security incident handling
Edit your computer security incident handling form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your computer security incident handling form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit computer security incident handling online
To use the services of a skilled PDF editor, follow these steps:
1
Log in to your account. Click on Start Free Trial and register a profile if you don't have one.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit computer security incident handling. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
With pdfFiller, dealing with documents is always straightforward. Try it right now!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out computer security incident handling
How to fill out computer security incident handling
01
To fill out computer security incident handling, follow these steps:
02
- Identify the incident: Determine if an incident has occurred and classify its severity.
03
- Report the incident: Notify the appropriate personnel, such as the incident response team or management.
04
- Gather information: Collect as much information as possible about the incident, including the time, date, and location of the event.
05
- Assess the impact: Evaluate the potential impact of the incident on the organization's systems, data, and operations.
06
- Contain and mitigate: Take immediate steps to contain and mitigate the incident to prevent further damage.
07
- Investigate: Conduct a thorough investigation to determine the cause of the incident and gather evidence for analysis.
08
- Notify stakeholders: Inform relevant stakeholders, including internal and external parties, about the incident and its potential impact.
09
- Document and analyze: Document all relevant details of the incident and analyze the data to identify patterns or vulnerabilities.
10
- Remediate and recover: Develop and implement a plan to remediate the incident, recover affected systems, and strengthen security measures.
11
- Evaluate and improve: Evaluate the incident response process, identify areas for improvement, and implement necessary changes to enhance future incident handling.
12
- Learn and educate: Share lessons learned from the incident with the organization's staff and provide awareness training on incident handling best practices.
Who needs computer security incident handling?
01
Computer security incident handling is needed by any organization or individual that utilizes computer systems.
02
This includes businesses of all sizes, government agencies, non-profit organizations, educational institutions, and individuals who rely on technology for their operations or personal activities.
03
Effective incident handling helps to protect sensitive information, prevent unauthorized access, minimize the impact of security incidents, and maintain the integrity and availability of systems and data.
04
Therefore, it is essential for any entity that values the security and confidentiality of their digital assets to have a computer security incident handling capability in place.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I modify my computer security incident handling in Gmail?
It's easy to use pdfFiller's Gmail add-on to make and edit your computer security incident handling and any other documents you get right in your email. You can also eSign them. Take a look at the Google Workspace Marketplace and get pdfFiller for Gmail. Get rid of the time-consuming steps and easily manage your documents and eSignatures with the help of an app.
Can I create an eSignature for the computer security incident handling in Gmail?
You can easily create your eSignature with pdfFiller and then eSign your computer security incident handling directly from your inbox with the help of pdfFiller’s add-on for Gmail. Please note that you must register for an account in order to save your signatures and signed documents.
How do I fill out the computer security incident handling form on my smartphone?
You can easily create and fill out legal forms with the help of the pdfFiller mobile app. Complete and sign computer security incident handling and other documents on your mobile device using the application. Visit pdfFiller’s webpage to learn more about the functionalities of the PDF editor.
What is computer security incident handling?
Computer security incident handling refers to the process of detecting, managing, and mitigating security incidents to minimize impact and restore normal operations.
Who is required to file computer security incident handling?
Organizations that experience a computer security incident are required to file incident handling reports, including IT departments and security teams.
How to fill out computer security incident handling?
To fill out computer security incident handling, document the details of the incident, including the nature of the incident, affected systems, response actions taken, and any relevant timelines.
What is the purpose of computer security incident handling?
The purpose of computer security incident handling is to effectively manage incidents to reduce risks, protect sensitive data, ensure compliance, and enhance future security measures.
What information must be reported on computer security incident handling?
Information that must be reported includes the incident type, description, impact assessment, response actions, involved personnel, and recovery measures.
Fill out your computer security incident handling online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Computer Security Incident Handling is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















